
Web Exploitation Essentials: 20 Repeated Patterns – Shocking Real-World Lessons I Learned the Hard Way
I didn’t pick up web exploitation from some tidy checklist or textbook walkthrough. Nah—I earned my stripes the hard way: botched tests, facepalm-worthy oversights, and more than a few false positives that sent me chasing ghosts at 2 a.m. If you’re low on time and high on curiosity, this guide cuts through the noise and gives you a fast, high-signal map of what actually shows up in real-world apps.
Inside, you’ll get 20 recurring exploit patterns, the telltale signs that give them away, and the practical fixes that stop them from turning into 3 a.m. fire drills. I’ll walk you through where tools lead you astray, where your gut can save you a solid half hour (or more), and how to build a slim, repeatable testing flow you can start using right now—even if your app is already live and breathing down your neck.
This isn’t some theory-heavy academic fluff. It’s the stuff I wish someone had sat me down and told me before my first “client’s-about-to-call-legal” moment.
- Look for pattern signals, not just payloads
- Confirm impact with small, safe steps
- Document fixes that survive refactors
Apply in 60 seconds: Pick one endpoint you own and write down its trust boundaries in one sentence.
Table of Contents
Mindset and scope: how to win fast in 2025
The fastest testers I know aren’t the ones with the biggest payload library. They’re the ones who can name the trust boundary in 10 seconds and predict the failure mode in 30. When I was newer, I treated every endpoint like a lottery ticket. I scanned everything, celebrated “critical” alerts, and then spent 45 minutes discovering I’d just found a debug banner and my own overconfidence.
In 2025, the shape of real-world apps—microservices, managed auth, feature-flag sprawl, AI-assisted dev—means the same old mistakes wear new clothes. A modern bug often hides in the seams: service-to-service calls, cached permissions, and “temporary” admin paths that never die.
- Think in patterns. The payload is the last mile.
- Start with identity and data flow. That’s where impact lives.
- Keep your proof small. A 2-step confirmation beats a 20-step guess.
- Map who can call what
- Check where data is transformed
- Identify the “silent” internal hops
Apply in 60 seconds: Sketch a three-box diagram: client → API → internal service.
- Do you have written permission for this target? Yes/No
- Is the scope explicit about domains, IPs, and accounts? Yes/No
- Is there a defined stop condition for production risk? Yes/No
- Do you have a test account with least privilege? Yes/No
Next step: If any answer is “No,” pause and get scope clarified before you run deeper tests.
Save this checklist and confirm the current scope on the owner’s official authorization record.

Pattern set 1: auth and session missteps
If web exploitation had a “top chart,” identity issues would still be getting radio play. These problems are durable because teams ship features faster than they design permission models. The most repeated sub-patterns I keep seeing:
1) Broken object-level authorization
The classic: you can access someone else’s resource by changing an ID. The 2025 version is trickier—IDs might be opaque, but the resource filter is still missing in a downstream service. I once celebrated a “fixed” endpoint, only to realize the mobile API still leaked the same data path through a different route. That was a humbling 25-minute walk back to the whiteboard.
2) Token confusion and session shadowing
Multiple token types (access, refresh, service tokens) invite mix-ups. Look for places where a backend accepts “any valid token” rather than the right kind of token. The exploit isn’t always dramatic; sometimes it’s a quiet role uplift that turns a support user into an auditor.
3) Password reset and magic link edge cases
Reset flows are a gold mine for business shortcuts: weak rate limiting, overly generous link reuse, or account enumeration. Even robust identity providers don’t save you if your app logic stitches the flow incorrectly.
- Test identity flows with two accounts and three roles.
- Look for caching of permissions with a TTL that outlives a role change.
- Confirm whether mobile and web share the same authorization layer.
Show me the nerdy details
When apps front an identity provider, the weakest point is often the application’s authorization layer, not the provider. Pay attention to where roles are translated into permissions and where those permissions are cached or serialized for speed.

Pattern set 2: input handling beyond classic SQLi
Classic SQL injection isn’t dead, but it’s no longer the only headline. The repeated pattern now is “query translation risk”: your input crosses frameworks, parsers, and filters on its way to a data store.
4) NoSQL injection through flexible filters
When the app accepts JSON filters, operators can slip through. The punchline is that the “boring” search box becomes the most dangerous because it’s built to be flexible. I once spent 47 minutes chasing a dramatic-looking payload only to find the real weakness was a single unvalidated filter key in a quiet endpoint.
5) GraphQL overexposure
GraphQL issues often look like data leakage rather than raw injection: introspection left on, overly broad resolvers, or missing field-level authorization. The exploit path is usually short—sometimes two queries are enough to map forbidden data shapes.
6) XSS with modern templating
Frameworks help, but XSS persists in rich-text, markdown renderers, and third-party widgets. The repeated trap is “safe-by-default” assumptions undone by a custom escape helper or a rushed UI plugin.
- Confirm where sanitization happens: client, API, or renderer.
- Test stored pathways, not just reflective ones.
- Look for “HTML allowed” flags that become global by accident.
- Probe JSON filters safely
- Validate GraphQL resolver boundaries
- Audit rich-text rendering paths
Apply in 60 seconds: Identify one endpoint that accepts a JSON body and list the expected keys.
Pattern set 3: deserialization and template traps
These bugs rarely announce themselves. They hide behind convenience features: “import your settings,” “upload a workflow,” “sync your profile.”
7) Unsafe deserialization
Even if your core app is clean, a legacy microservice might still accept serialized objects. The modern signal is a file or blob that stores “state.” If you see a “restore session” or “import config” feature, slow down and inspect how the server interprets it.
8) Server-side template injection
SSTI appears when devs allow user-defined templates or dynamic email formatting. The exploit shape often starts as a harmless-looking preview function. I once treated a template preview bug as “just UI,” then discovered it had server execution reach. That mistake cost me an extra hour and a bruised ego.
9) Expression language surprises in low-code features
Workflow engines and rule builders can be powerful and dangerous. The repeated issue: the platform exposes more expression power than the UI admits.
Show me the nerdy details
For SSTI and deserialization, you don’t need to escalate to fancy payloads early. First confirm whether user-controlled data is being interpreted as code or as data. The smallest proof-of-interpretation is often the safest and fastest.
Pattern set 4: file and path abuse
File-centric bugs keep showing up because apps love uploads, exports, and “shareable reports.” The pattern is reliable: if the app handles files, there’s a chance it trusts filenames or paths too much.
10) Path traversal through “helpful” file APIs
Download endpoints that accept a filename parameter are classic. The 2025 twist is indirect traversal through storage abstraction layers where validation is one layer too high.
11) Insecure file upload and content-type confusion
Uploads are often protected by extension checks or MIME sniffing, but the real risk can be where the file is served from. A safe upload folder becomes unsafe if it’s mapped to a dynamic renderer or a misconfigured CDN rule.
12) PDF/office renderers and conversion pipelines
Document conversion services can open a door to SSRF-like effects or sandbox escapes. You don’t need to assume the worst—just treat conversion features as privileged compute.
- Check how the app names, stores, and serves uploads.
- Verify whether private buckets can be referenced publicly.
- Look for “export to HTML” features that render user content.
- Choose automation when you need broad coverage across 50+ endpoints quickly.
- Choose manual when identity, business logic, or multi-step flows drive impact.
- Hybrid when you can use scans to surface entry points, then verify with targeted requests.
Time/cost trade-off: A light scan can save 20–30 minutes, but manual validation often saves hours of false-positive cleanup.
Save this card and confirm the current testing rules on the target’s official security policy page.
Pattern set 5: SSRF and network pivots
SSRF is a bridge bug. It turns an innocent “fetch this URL” feature into a network read primitive. The repeated signal is any server-side integration that accepts user influence over a destination—webhooks, image fetchers, URL previews, document importers.
13) URL fetchers with weak allowlists
Most teams implement an allowlist. Fewer teams maintain it correctly across redirects, DNS changes, or alternate IP ranges. The exploit shape is often subtle: one overlooked subdomain, one redirect rule, or one internal hostname exposed through a staging config.
14) Cloud metadata and internal service discovery
Even when teams block the famous metadata IPs, internal admin panels, service registries, and monitoring endpoints can still be reachable. The risk is not always “steal secrets”—sometimes it’s “learn just enough topology to plan the next move.”
- Test URL preview features with safe, controlled endpoints you own.
- Check redirect handling and DNS resolution order.
- Document any internal hostnames you can infer through error messages.
Show me the nerdy details
SSRF defense is layered: strict parsing, canonicalization, DNS pinning, and egress controls. If you only rely on string matching, you’re betting the house on perfect URL parsing under pressure.
Pattern set 6: business logic and race conditions
This is where hackers and auditors become awkward cousins. Business logic bugs are rarely about syntax; they’re about meaning. The repeated pattern is “the app does what you asked, not what it intended.”
15) Price, quota, and coupon manipulation
Even non-commerce apps have “value levers”: credits, usage tiers, free trials, rate limits. A missed server-side check can allow double redemption or unauthorized plan upgrades.
16) State machine breaks
If an action should be Step 3 but can be triggered at Step 1, you have a logic gap. I once assumed a “completed” status was server controlled—only to realize the client could set it with a hidden parameter. That was a fast fix, but a slow lesson.
17) Race conditions in multi-request flows
The 2025 flavor is concurrency across microservices: two services update the same account state with slightly different timelines. The exploit path can be as simple as two rapid requests within 200–500 ms, especially around refunds, role changes, or one-time tokens.
- Define the expected state order
- Check server-side enforcement
- Test concurrency on high-value actions
Apply in 60 seconds: Pick one “one-time” action and ask, “What stops me from doing this twice?”
Pattern set 7: misconfig and supply-chain surprises
Misconfig bugs are the “open window” of modern systems. They’re boring until they’re catastrophic. The repeated pattern is divergence between environments: staging is permissive, production inherits it, and nobody notices because the UI looks fine.
18) Overly permissive CORS and debug features
CORS isn’t just a header issue; it’s a trust decision. When you see wildcard origins paired with credentialed requests, slow down. I once watched a team fix an endpoint-level CORS issue while leaving a global gateway rule untouched. The patch looked beautiful and solved exactly 0% of the real risk.
19) CI/CD secrets and artifact exposure
Build logs, test artifacts, and container registries sometimes leak more than the app. The exploit shape is “not the app itself, but the pipeline that feeds it.”
20) Third-party SDK and plugin privilege creep
Analytics, chat widgets, and feature flag SDKs can introduce injection or data exposure routes. The repeated mistake is granting them far broader scopes than their function needs.
- Compare staging vs production headers and access controls.
- Review gateway defaults and global policies.
- Audit third-party scopes once per release cycle.
Pattern set 8: observability, logging, and false positives
This section exists because I wasted too many evenings arguing with my own tools. In real engagements, false positives can burn trust faster than a low-severity bug ever could.
When scanners cry wolf
Automated tools often flag reflection as XSS, error messages as SQLi, and version banners as “exploitable.” The repeated fix is simple: verify exploit preconditions. If the code path lacks a sink, you’re staring at a mirage.
When logs become the vulnerability
Logs can leak tokens, internal hostnames, and stack traces. The 2025 twist is distributed tracing: a single trace ID can reveal a surprising amount of architecture if exposed publicly.
- Always reproduce with a minimal, safe proof.
- Check whether sensitive values are masked in logs.
- Review client-visible errors after major framework upgrades.
Show me the nerdy details
High-confidence reporting often comes down to preconditions: controllable input, reachable sink, and meaningful impact. If you can’t clearly show all three, label the finding as “needs verification” rather than forcing certainty.
Short Story: I once joined a test late, handed a scope doc, and promised “quick wins.” The scanner lit up a “critical injection” in a reporting endpoint. I felt like a hero for about five minutes. Then I noticed the payload never reached the database; it died in a validation layer that merely echoed my input back in a debug response. I had just discovered a loud, harmless reflection bug and inflated it into a crisis. The client didn’t yell.
They just went quiet in that way that makes your stomach drop. I spent the next hour rebuilding trust: showing the real data flow, explaining the difference between a scary string and a dangerous sink, and producing a smaller, clearer proof for two medium findings that actually mattered. That day taught me a basic rule: confidence isn’t volume. It’s precision.
Build your 20-pattern playbook
If you’re a time-poor operator, you don’t need 300 techniques. You need a repeatable routine that catches the shapes that explain 80% of real-world pain. Here’s a compact way to operationalize the 20 patterns above.
A 3-pass workflow that fits a real week
- Pass 1 (15–25 minutes): Map identity, roles, and sensitive objects.
- Pass 2 (30–45 minutes): Test high-value flows: upload, export, URL fetch, admin actions.
- Pass 3 (20–40 minutes): Validate business rules and concurrency edges.
- Endpoints in scope:
- Auth complexity (1 simple / 3 multi-role):
- Integration features present (0–3: uploads, webhooks, exports):
Estimate: ~3.5–6 hours for a focused pattern sweep.
Save this estimate and confirm today’s engagement hours with the project owner’s official scope document.
- Repeat the same pattern checks quarterly
- Track which patterns your org actually ships
- Turn fixes into reusable guardrails
Apply in 60 seconds: Add one regression test for an authorization check you just validated.
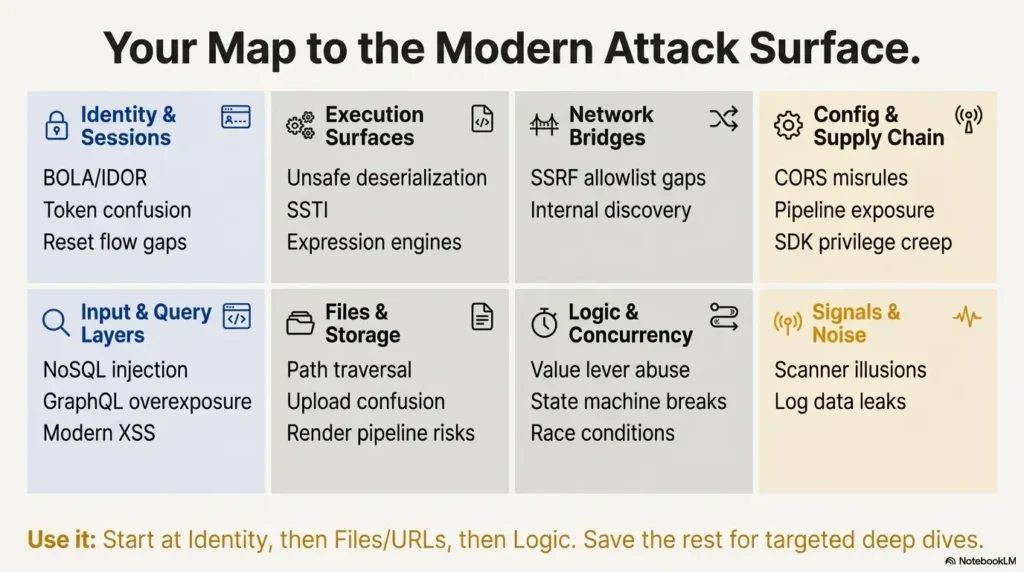
- BOLA/IDOR
- Token confusion
- Reset flow gaps
- NoSQL filter injection
- GraphQL overexposure
- Modern XSS paths
- Unsafe deserialization
- SSTI
- Expression engines
- Path traversal
- Upload confusion
- Render pipeline risks
- SSRF allowlist gaps
- Internal discovery
- Value lever abuse
- State machine breaks
- Race conditions
- CORS misrules
- Pipeline exposure
- SDK privilege creep
- Scanner illusions
- Log data leaks
Closing the loop: what to do in the next 15 minutes
Remember the opening promise: patterns first, panic last. The biggest shift that improved my results wasn’t a new tool—it was refusing to treat every alert as a story worth finishing. Once I started naming the pattern early, I stopped wasting time on seductive dead ends and started producing clearer, calmer reports.
Here’s a tight next step you can complete before your coffee cools:
- Pick one application you’re allowed to test.
- List the three most sensitive objects it stores.
- Map the roles that touch them.
- Run a mini sweep for: BOLA, upload/path risk, and one business rule.
If you find nothing, you still win—you just built a target-specific baseline that will catch regressions later. If you find something, you have a clean, pattern-based narrative for fixing it without drama.
Last reviewed: 2025-12; sources: OWASP Top 10, OWASP Cheat Sheet Series, PortSwigger Web Security Academy.

FAQ
What are the first three patterns I should learn if I’m new?
Start with broken object-level authorization, basic XSS in real rendering paths, and file/path misuse. Those three teach you how identity, input, and storage fail in the wild. Apply in 60 seconds: Pick one endpoint and ask, “What object is this protecting, and who is allowed to see it?”
How do I avoid false positives when using scanners?
Confirm preconditions: controllable input, reachable sink, and real impact. If one is missing, label it as “needs verification” and move on. Apply in 60 seconds: Try a harmless payload that proves data reaches the suspected sink without causing risk.
Is SSRF still worth prioritizing in modern cloud apps?
Yes, because integrations keep multiplying. URL previews, webhooks, and document importers are evergreen SSRF surfaces. Even partial internal discovery can be high impact. Apply in 60 seconds: List every feature that fetches a URL server-side.
What’s the quickest way to test for business logic issues?
Write the intended rule in one sentence, then try to break order, limits, or reuse constraints. Focus on high-value actions like role changes, credits, or one-time links. Apply in 60 seconds: Ask, “What happens if I do this twice?”
How should I report a pattern-based finding to get faster fixes?
Describe the pattern, the impacted object, the role boundary, and one safe reproduction path. Then propose a guardrail that survives refactors, like centralized authorization checks or schema validation. Apply in 60 seconds: Add one recommended unit or integration test to your report.
Do these patterns apply to mobile apps too?
Absolutely—mobile often exposes alternate APIs with slightly different authorization and validation. Treat mobile endpoints as first-class citizens in your threat model. Apply in 60 seconds: Compare one web request and one mobile request for the same action.
🧵 Closing the Loop: What I Wish Someone Told Me Earlier
Let me be blunt: I didn’t get better at web exploitation because I memorized more payloads. I got better because I stopped panicking every time Burp turned red and started asking one simple question:
“Wait… have I seen this shape before?”
I used to chase every reflected string like it owed me money. Once, I spent two hours debugging what I thought was a juicy injection point—turns out it was a marketing pixel echoing back my user-agent. I reported it. They thanked me… by unsubscribing me from their newsletter.
The real growth came when I embraced a boring truth:
Patterns repeat. People make the same mistakes, just wrapped in shinier frameworks and fancier UIs.
I stopped trying to be clever and started being consistent. I built a pattern-based checklist. I stuck to it. I stopped staying up until 3 a.m. writing “high-risk” reports for bugs that weren’t even bugs. I also started sleeping better (10/10 would recommend).
Here’s the ending I wish someone gave me on day one:
- You don’t need to find everything. You need to find what actually matters, faster.
- Most bugs aren’t hiding. They’re wearing a funny hat and hoping you won’t notice.
- Tools will whisper lies. Logs will gaslight you. But patterns? Patterns tell the truth.
So next time you’re staring at an endpoint wondering if it’s worth poking, don’t ask “What payload can I throw?” Ask:
“What pattern could this be repeating?”
If it fits? You’re five steps ahead.
If it doesn’t? You just saved yourself an hour of glorious nothing.
🚀 15-Minute Challenge (Still Worth It Even If Your Coffee’s Cold):
- Pick one app you’re allowed to test.
- List the three most sensitive things it holds.
- Map who can touch them and how.
- Check for:
✅ BOLA (Broken Object-Level Authorization)
✅ Upload/path funkiness
✅ A rule the business assumes but never enforces
If you find nothing? Great—you just mapped your future regression test.
If you find something? Even better—you’ve got a real story, not just a string match.
Last thought before you go:
I’ve made mistakes. You will too. What matters is that each time, you catch the shape faster.
And one day, a junior dev will walk up to you, baffled by a “weird bug,” and you’ll smile and say:
“Ah. Classic case of token shadowing.”
Like a wizard. But with less fireballs, and more HTTP headers.
Good hunting. And remember:
Patterns over panic. Always.
🛠️ — Last tested on: one too many production systems without coffee.
Keywords: Web Exploitation Essentials, authorization testing, SSRF, insecure file upload, business logic vulnerabilities
