Beyond the Trophy: Mastering the Kioptrix Learning Path
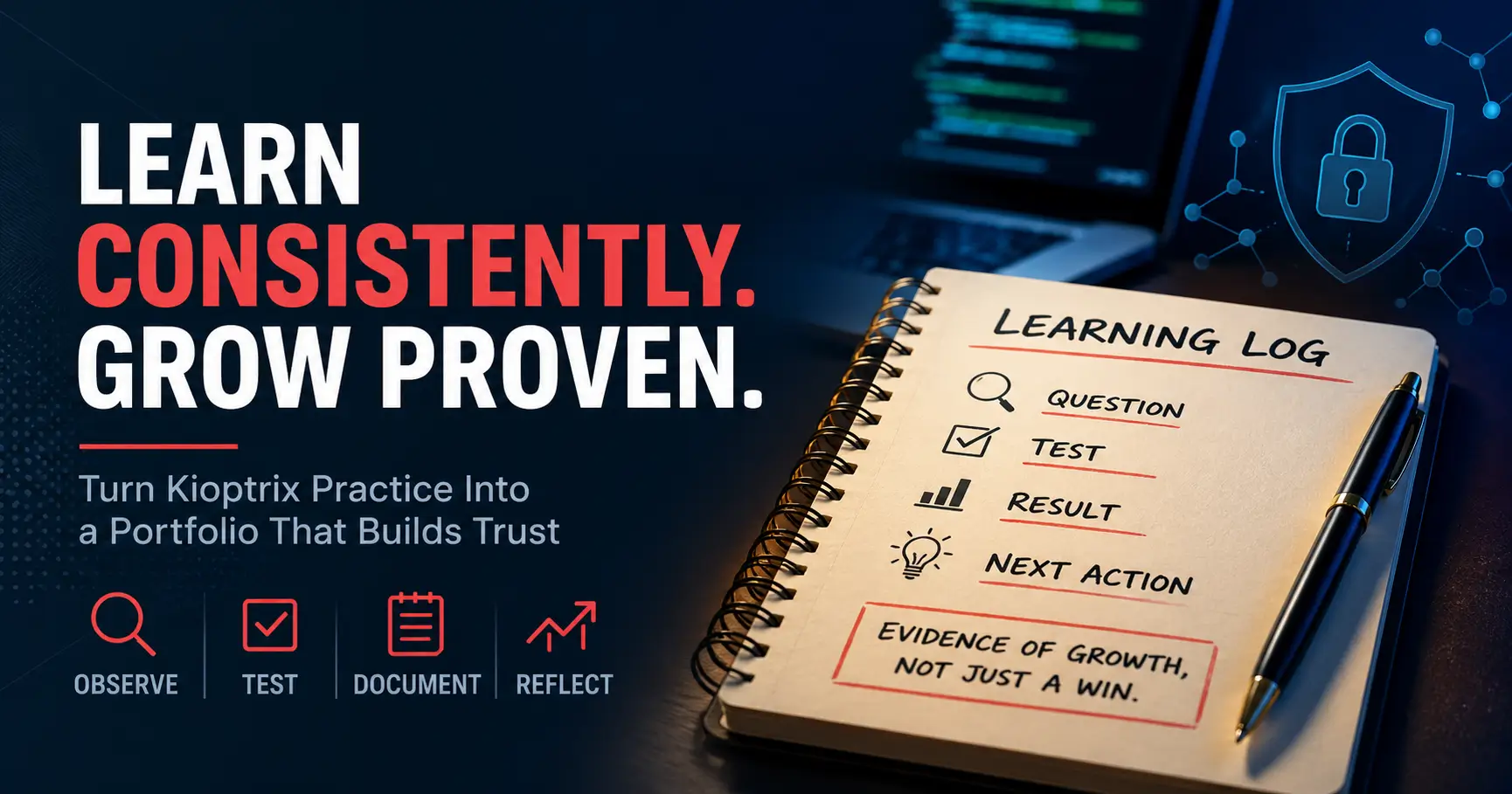
There is a quiet difference between finishing Kioptrix Level and having something worth showing afterward. While many can collect commands and screenshots, true expertise lies in documenting the why behind the how.
This guide transforms your lab session into a learning-consistency portfolio. We move beyond “hacking a box” to evidence-based cybersecurity growth by:
- ▹ Explaining enumeration and documenting failed hypotheses.
- ▹ Capturing decision points to build credibility with mentors and hiring managers.
- ▹ Applying a practical framework: One question, one test, one result, one next action.
No smoke machines. Just a cleaner trail, a better signal, and the habits of a professional.
Table of Contents
Fast Answer: Use Kioptrix Level as a learning-consistency portfolio by documenting what you tested, why you tested it, what changed your thinking, and what you would do next. Instead of presenting the lab as “I hacked a box,” frame it as repeatable cybersecurity practice: enumeration notes, evidence screenshots, failed hypotheses, decision points, and a clean reflection that proves growth over time.
Start Here: Kioptrix Is Better as a Learning Log Than a Trophy
Why “I rooted the box” Says Less Than You Think
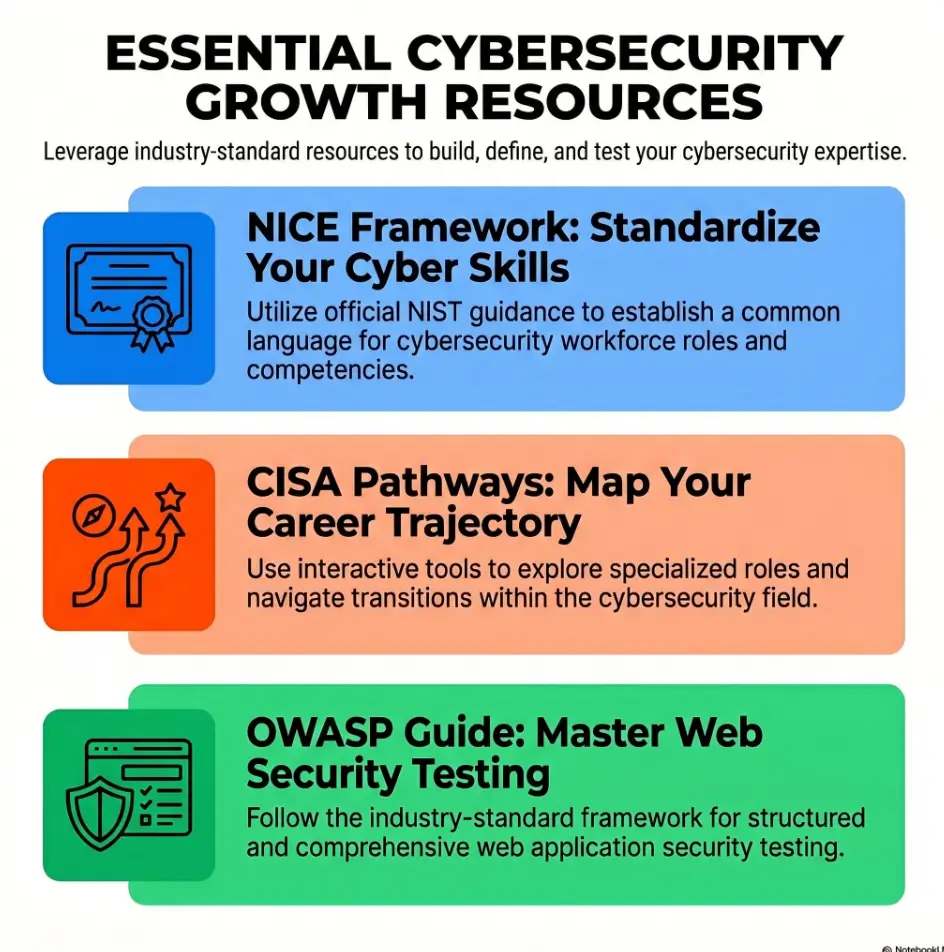
“I rooted the box” sounds satisfying. It is short, shiny, and dramatic. It also hides almost everything that matters.
It does not show how you handled uncertainty. It does not show whether you understood the services you found. It does not show whether you followed scope, kept notes, avoided random commands, or learned anything reusable. It is a fireworks sentence. Bright for 4 seconds, then smoke.
When you use Kioptrix Level as a learning log, the signal changes. You are no longer saying, “Look what I broke.” You are saying, “Look how I think when the path is unclear.” That is much more useful for mentors, hiring managers, study partners, and future-you on a sleepy Tuesday.
I learned this the unglamorous way. My first lab notes were basically command confetti: a few scans, a few screenshots, a heroic lack of explanation. When I came back 2 weeks later, I could not tell what I had believed at the time. The box had been “solved,” but the lesson had escaped through the window.
The Real Signal: Can You Explain Your Path Without Theater?
A mature Kioptrix write-up does not need smoke machines. It needs sequence.
- What did you observe first?
- Which service or clue mattered?
- What did you test next?
- What result changed your plan?
- What would you repeat differently next time?
That kind of writing shows learning consistency. It also shows restraint. In cybersecurity, restraint is not decorative. It is the guardrail that keeps curiosity inside legal, ethical, and useful boundaries.
What Hiring Managers and Mentors Actually Notice
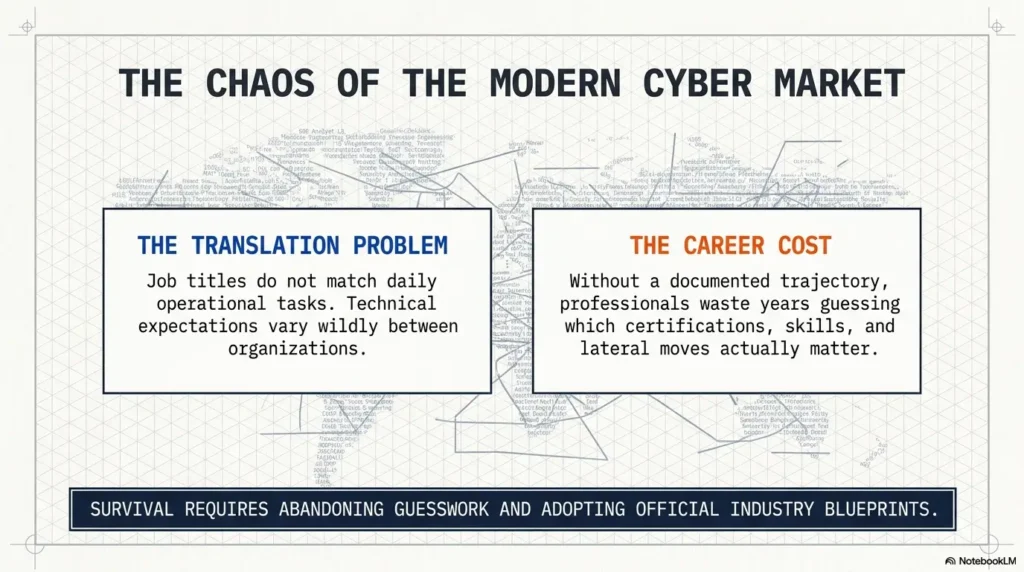
Entry-level cybersecurity candidates often worry that they need spectacular proof. Usually, they need clearer proof.
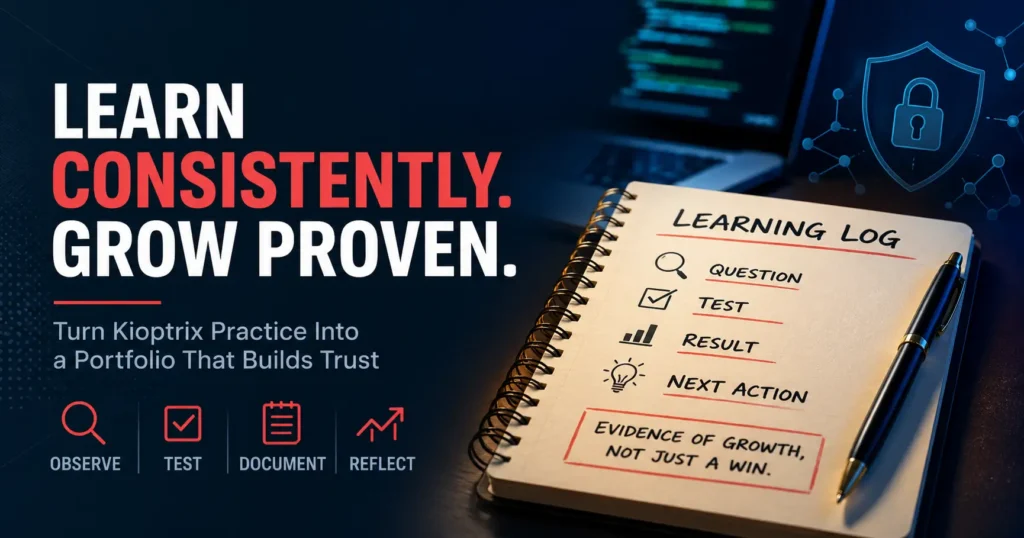
The NIST NICE Framework describes cybersecurity work using tasks, knowledge, and skills. That is a helpful reminder: your portfolio should not only show outcomes. It should show the habits behind the outcome, including method, evidence, judgment, and communication.
A mentor does not need you to pretend you were born holding an nmap command. They need to see whether you can notice, test, document, and improve. That is the difference between a trophy shelf and a workbench.
- Document the starting point before the ending.
- Explain why each test made sense.
- Save one reflection for next time.
Apply in 60 seconds: Open your last lab note and add one sentence beginning with “At this point, I thought…”
Who This Is For, and Who This Is Not For
This Is For Beginners Building a Cybersecurity Practice Habit
This guide is for the learner who wants a repeatable rhythm more than a dramatic reveal. Maybe you are studying after work. Maybe you are moving from help desk into security. Maybe you are building your first portfolio and wondering how to sound competent without sounding inflated.
Good. That is a sturdy place to start.
Kioptrix is useful because it gives beginners a contained lab environment. You can practice enumeration, web observation, service research, note-taking, and reflection without wandering into unauthorized territory. The lab is the sandbox. The learning log is the footprint you leave in the sand. If this is your first serious lab, a calm Kioptrix first lab setup can make the whole beginning feel less like fog and more like a doorway.
This Is For Help Desk, IT Support, and Career Switchers
If you come from help desk or IT support, you already have more relevant experience than you may think. Troubleshooting teaches pattern recognition. Ticket notes teach documentation. User support teaches communication under ambiguity. Cybersecurity simply changes the objects in the room.
A good Kioptrix write-up can connect those dots:
- “I identified exposed services and prioritized likely leads.”
- “I separated confirmed facts from guesses.”
- “I documented what failed so I could avoid repeating it.”
- “I kept the work inside a legal lab environment.”
That sounds far more professional than “I hacked Kioptrix.” It also travels better into interviews, LinkedIn posts, GitHub READMEs, and personal blogs. For readers coming from support roles, Kioptrix for help desk workers can help translate everyday troubleshooting habits into security-learning language.
This Is Not For People Trying to Prove They Are “Elite”
If the goal is to look dangerous online, this article will disappoint you in 11 different colors.
Kioptrix is not a stage for cosplay. It is a practice room. The best learners do not use every session to announce mastery. They use sessions to reduce confusion, one careful note at a time.
This Is Not a Shortcut Around Ethics, Scope, or Permission
Only practice in environments where you have permission. Legal labs, intentionally vulnerable machines, local virtual machines, and sanctioned CTF platforms are appropriate places to learn. Real systems that do not belong to you are not “practice.” They are someone else’s house.
In a portfolio, say this plainly. A single sentence can do the job:
“This write-up describes practice performed in a local, intentionally vulnerable lab environment.”
That sentence is small, but it carries a clean suit and good shoes.
Eligibility Checklist: Should This Kioptrix Session Become a Portfolio Entry?
| Question | Yes or No | Next Step |
|---|---|---|
| Was it done in a legal lab? | Yes required | State the scope clearly. |
| Did you record more than commands? | Prefer yes | Add reasoning notes. |
| Can you explain one decision point? | Prefer yes | Write a short reflection. |
Neutral action: If you cannot answer “yes” to the first question, do not publish the entry.
The Consistency Frame: Turn One Kioptrix Session Into Evidence
Show the Starting Point Before You Show the Win
A strong learning log begins before the exciting part. The start is where your judgment becomes visible.
Write down the date, the lab, the time box, and the session goal. Not a grand goal. Not “become a cyber wizard by dinner.” Something smaller:
- Run baseline enumeration.
- Identify exposed services.
- Research one unfamiliar version.
- Test one web path carefully.
- End with a next question.
A 30-minute session can count if it has a clean purpose. In fact, short sessions often create better notes because you are forced to choose. Long, foggy sessions can become a haunted attic of terminal scrollback. If you are not sure how long to sit with one session, a practical Kioptrix session length guide can help you choose a repeatable block instead of chasing heroic study marathons.
Capture One Question, One Test, One Result
The simplest frame is almost embarrassingly plain:
Question → Test → Result → Next thought.
For example:
- Question: Which services are exposed?
- Test: Ran a baseline scan inside the local lab network.
- Result: Found several open ports worth investigating.
- Next thought: Prioritize web-facing clues before deeper research.
This does not reveal dangerous magic. It shows method. You are building a breadcrumb trail, not handing out a flamethrower manual.
Let the Notes Prove the Practice
Your notes should make consistency visible even when the session feels unimpressive. Especially then.
Some sessions will not end with a breakthrough. That is normal. A “no visible progress” entry can still prove discipline if it captures what you ruled out and what you will try next.
Quiet portfolio truth: A clean record of narrowing the problem is often more credible than a dramatic ending with no explanation.
When I stopped treating every session as a mini-movie, my notes improved immediately. The hero did not need a cape. The hero needed timestamps and fewer open tabs.
The Portfolio Angle: What to Document So It Looks Professional
Environment Setup: What You Ran and Why It Was Safe
Begin with a simple lab statement. Keep it boring on purpose.
Example:
“This practice was completed in a local virtual lab using an intentionally vulnerable Kioptrix machine. No third-party systems were tested.”
That line does 3 useful things. It shows scope. It shows permission. It tells readers you understand the ethical boundary. In cybersecurity, a boring boundary is beautiful. It is the fence that keeps the garden from becoming a court case. If your setup is still wobbly, review the Kioptrix network setup before turning rough notes into public proof.
Enumeration Notes: Services, Versions, Paths, and Clues
Enumeration is where many beginners either shine or sprint into fog. Do not just paste output. Translate it.
Your portfolio note should explain what the output meant to you at that moment:
- Which services looked important?
- Which versions needed research?
- Which web paths deserved manual review?
- Which findings were confirmed facts?
- Which findings were only guesses?
OWASP’s Web Security Testing Guide treats information gathering and attack surface identification as serious testing activities, not filler before “the real part.” That is a useful mindset for Kioptrix too. Your early observations are not warm-up doodles. They are the map. For a deeper internal companion, a Kioptrix enumeration process can help you turn raw scan output into usable learning notes.
Decision Notes: Why One Lead Became More Important Than Another
Decision notes are where your portfolio becomes human. Anyone can show a command. Fewer people can explain why they chose the next step.
Try language like:
- “I prioritized the web service because it exposed more observable clues.”
- “I paused on this lead because the result did not match my assumption.”
- “I researched the version before testing because I did not understand the risk pattern yet.”
- “I returned to enumeration because my current path had become guess-heavy.”
That last sentence is gold. It shows you know when you are guessing. Many beginners keep digging because stopping feels like losing. In reality, stopping can be the most senior move in the room. A simple Kioptrix decision tree can also help you name when to continue, pause, research, or return to basics.
Evidence Screenshots Without Screenshot Hoarding
Screenshots should support your explanation. They should not replace it.
Use 3 to 6 screenshots for a compact portfolio entry. Include screenshots only when they prove something important: environment, scan summary, web clue, decision point, or final reflection. A folder with 47 images named “Screenshot 2026-04-25 at something something” is not evidence. It is digital confetti with anxiety seasoning.
Show me the nerdy details
A clean lab entry often separates artifacts into three groups: raw output, interpreted notes, and publishable evidence. Raw output can stay private. Interpreted notes explain what mattered. Publishable evidence should be minimal, scoped, and safe, with sensitive details removed if needed.
- Start with a legal lab statement.
- Translate tool output into human notes.
- Use screenshots only when they prove a point.
Apply in 60 seconds: Add a “Why I chose this next” line under one command in your notes.
The Quiet Power Move: Write Down Failed Hypotheses
Why Wrong Guesses Make Your Learning Look Stronger
Beginners often hide failed attempts because they think failure makes them look unready. The opposite is usually true.
A failed hypothesis, written clearly, shows that you can test an idea and update your thinking. That is the skeleton key of technical growth. It is also the daily bread of real security work, where the first explanation is often incomplete, the second explanation is suspiciously confident, and the third one finally starts behaving.
Write failed hypotheses like this:
- Hypothesis: This service may expose a useful web clue.
- Test: Checked the page manually and reviewed visible paths.
- Result: No useful lead found from that path.
- Decision: Return to service list and compare other exposed surfaces.
No drama. No shame. No “I wasted 2 hours because I am a raccoon with a keyboard.” Just learning.
How to Describe a Dead End Without Sounding Lost
The trick is to avoid emotional fog and record the boundary.
Instead of:
“This did not work, so I got stuck.”
Write:
“This path did not produce a confirmed clue, so I paused it and returned to enumeration.”
That phrasing is calm. It shows judgment. It also makes your future session easier because you can see what you already tried.
Here’s What No One Tells You: Clean Failure Notes Beat Loud Claims
A loud claim says, “Trust me.” A clean note says, “Inspect my thinking.”
That is why failed hypotheses are so useful in a portfolio. They make the work auditable. They show your process under uncertainty. They give mentors something specific to respond to. If you want a more formal way to review your own patterns, a Kioptrix self-assessment can turn those quiet failures into visible skill growth.
Mini Calculator: Is This Session Portfolio-Ready?
Give yourself 1 point for each item you completed:
- Wrote a legal lab scope statement.
- Captured at least 3 confirmed facts.
- Recorded at least 1 failed hypothesis.
- Ended with 1 next action.
Output: 3 to 4 points means the session is probably strong enough to refine into a portfolio entry. 1 to 2 points means keep it as a private learning note for now.
Neutral action: Add the missing item before you publish.
Common Mistakes: Don’t Turn Kioptrix Into Cybersecurity Cosplay
Mistake 1: Writing Only the Exploit and Skipping the Thinking
The exploit is not the whole story. In a learning portfolio, it may not even be the most important part.
If your write-up jumps from scan output to final result, the reader sees a magic trick but not a mind. Slow down. Show how you moved from evidence to decision. Even 2 extra paragraphs can change the tone from “copied steps” to “developing practitioner.”
Mistake 2: Copying Walkthrough Language Into Your Own Notes
Walkthroughs can be helpful. Copying their language into your own portfolio is where things become thin.
Borrow structure if needed, but write your own observations. Your phrasing should reflect what you actually understood at the time. If you only understood 60 percent, say that privately in your notes and improve the explanation before publishing. Polished confusion is still confusion, just wearing a tie.
Mistake 3: Posting Proof Without Context, Scope, or Reflection
A screenshot without context is a postcard from a place no one can verify.
Give readers the frame: legal lab, session goal, key observations, decision points, outcome, and reflection. You do not need to publish every command. You do need to make the learning trail clear. A focused Kioptrix lab report can help you separate evidence from noise before you publish.
Mistake 4: Making the Story About “Hacking” Instead of Skill Growth
There is a reason mature practitioners talk about testing, analysis, validation, documentation, and reporting. Those words age better.
“Hacking” may get attention. “I practiced controlled enumeration, documented assumptions, and improved my testing sequence” gets respect from the right people. The second sentence has fewer fireworks and better shoes.
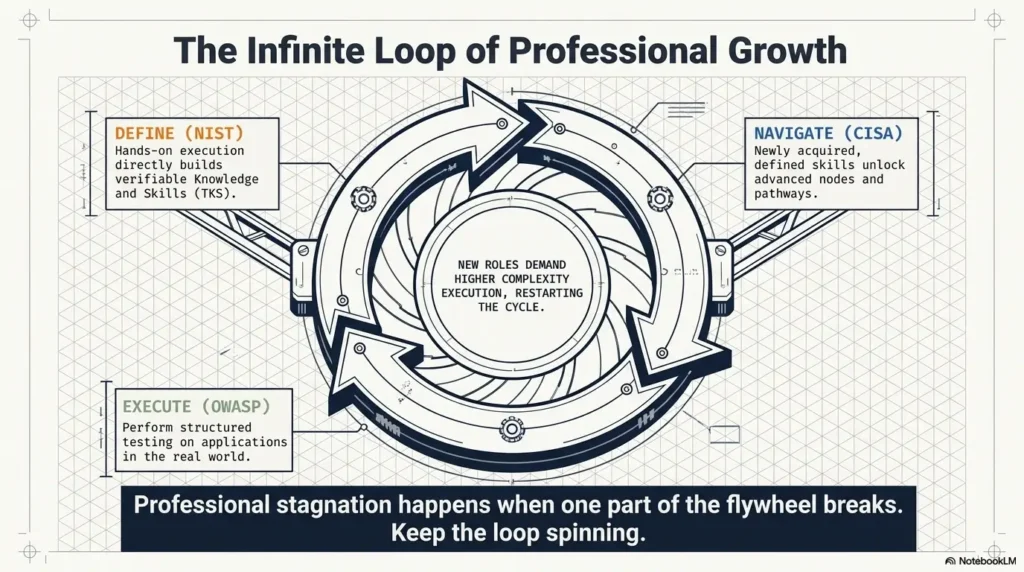
Infographic: The Kioptrix Learning-Consistency Loop
Legal lab, local target, clear boundary.
Services, versions, paths, visible clues.
One question, one method, one result.
Continue, pause, research, or return.
What changed, what remains, what next?
The Walkthrough Trap: Use References Without Losing Your Voice
When a Hint Helps and When It Steals the Lesson
Walkthroughs are not evil. They are power tools. Used carefully, they can save you from chewing on the same wrong assumption for 3 evenings. Used too early, they remove the exact friction that teaches you.
The goal is not to avoid help forever. The goal is to delay help long enough that your brain has something to attach the answer to.
Try this rule:
- Spend 20 to 30 minutes on your own focused attempt.
- Write down what you know and what you suspect.
- Read only enough hint material to choose a next direction.
- Close the reference and continue in your own words.
That last step matters. If the walkthrough’s voice becomes your voice, your portfolio starts sounding rented. When you do need a reference, use a Kioptrix Level walkthrough as a checkpoint, not as a substitute for your own reasoning.
The “Pause Before Reading” Rule for Better Retention
Before opening a walkthrough, write 3 lines:
- Facts: What I know.
- Guesses: What I think may matter.
- Question: What I need help deciding.
This turns the walkthrough into a targeted reference, not a replacement brain. It also protects your dignity. Getting stuck is not the problem. Outsourcing all your thinking too early is the problem.
Let’s Be Honest: Everyone Gets Stuck Somewhere
Every learner has a stuck place. Some get stuck reading service banners. Some get stuck interpreting web clues. Some get stuck because they opened 19 tabs and their browser now looks like a hedgehog having a paperwork crisis.
Do not write your portfolio as if you never got stuck. Write it as if you know what to do when you do.
- Attempt first with a time box.
- Write your own facts before reading.
- Return to your own notes after the hint.
Apply in 60 seconds: Add a “Before I looked this up…” line to your next Kioptrix note.
The Weekly Rhythm: Make Kioptrix Show Up as a Habit
The 30-Minute Session That Still Counts
Consistency does not require a heroic weekend. It requires a repeatable unit.
A 30-minute Kioptrix session can be useful if you define the edge of the work. For example:
- 5 minutes: review previous notes.
- 15 minutes: run or review one focused test.
- 5 minutes: write confirmed facts.
- 5 minutes: write the next action.
That is not glamorous. It is better than glamorous. It is survivable.
I have seen learners make more progress with three 30-minute sessions per week than with one dramatic 5-hour session that ends in snack wrappers and emotional static. Cybersecurity learning loves rhythm. It does not require thunder every time. A sustainable Kioptrix weekly habit can make that rhythm visible before motivation wanders off with the house keys.
What to Record When You Make No Visible Progress
No visible progress is still data. Record it carefully.
Use this format:
- What I tried: One sentence.
- What happened: One sentence.
- What I ruled out: One sentence.
- What I need to understand next: One sentence.
That turns frustration into structure. It also helps you avoid repeating the same dead end next time, which is basically giving your future self a sandwich and a flashlight.
How to End With a Next Question Instead of a Messy Tab Pile
Never end a session with “continue later.” That is too vague. Later-you will arrive confused and mildly betrayed.
End with a next question:
- “Which web path should I inspect manually first?”
- “What does this service version imply?”
- “Which finding is confirmed, and which is only a guess?”
- “Did I skip basic enumeration because I got excited?”
The next question is your bookmark. It is also the quiet bridge between sessions.
Decision Card: One Long Session vs. Three Short Sessions
| Choose This | When It Fits | Trade-Off |
|---|---|---|
| One 2-hour block | You need deeper focus and have energy. | Higher risk of sloppy notes near the end. |
| Three 30-minute blocks | You are studying around work or family. | Requires cleaner stopping points. |
Neutral action: Pick the rhythm you can repeat for 4 weeks, not the one that looks impressive once.
The Evidence Stack: Build a Learning Trail Over Several Sessions
Session 1: Baseline Enumeration and First Impressions
Your first session should not try to conquer the whole machine. It should build the starting map.
Record your environment, target, visible services, and first impressions. Separate facts from guesses. If something looks interesting, mark it, but do not let curiosity drag you into six directions at once.
A useful Session 1 note might end like this:
“Next action: review the web service manually and compare visible clues against the service list.”
Session 2: Narrowing the Attack Surface
Session 2 is about choosing. Beginners often feel they must chase everything. Professionals learn to prioritize.
Look for which exposed surface gives you the most useful information. Maybe the web service shows paths. Maybe a version number deserves research. Maybe your earlier scan needs validation because you rushed it. No shame. Rushed enumeration is how labs become haunted houses. If this keeps happening, a Kioptrix recon log template can slow the work down just enough to make it reusable.
Session 3: Testing One Path With Better Notes
Session 3 should test one path with more care. This is where your learning log gets rich.
Write what you expected before testing. Then write what actually happened. If the result surprised you, say why. That contrast is educational gold.
Session 4: Reflection, Cleanup, and Lessons Learned
Session 4 is where you turn rough notes into a portfolio-ready story.
Do not publish raw chaos. Clean it. Remove unnecessary output. Keep the decisions. Keep the dead ends that taught you something. Keep the ethical scope statement. Keep the reflection.
Short Story: The Night the Notes Saved the Lab
I once watched a learner return to a Kioptrix session after a long workday, convinced they had “made no progress” the week before. Their notes said otherwise. They had already ruled out one noisy path, confirmed a useful service clue, and written a next question so clear it almost tapped them on the shoulder. Within 15 minutes, they were moving again.
Nothing magical happened. No cinematic keyboard storm. The difference was a plain note written by a less-tired version of themselves. That is the secret kindness of good documentation. It lets your better hour help your worse hour. In cybersecurity learning, that is not a small thing. It is how consistency becomes visible.
- Session 1 maps the target.
- Session 2 narrows the surface.
- Session 3 tests one path carefully.
Apply in 60 seconds: Rename your next note “Session 1: Baseline and First Impressions.”
The Language Shift: Say “I Practiced” Better Than “I Hacked”
Replace Bragging Words With Skill Words
The language you use changes how your work is read.
Instead of leaning on “hacked,” “pwned,” or “destroyed,” use language that maps to professional behavior:
- Practiced enumeration.
- Documented assumptions.
- Validated observations.
- Prioritized leads.
- Reviewed evidence.
- Reflected on errors.
This does not make your writing dull. It makes it credible. A good portfolio should sound like someone you would trust near production systems, not someone who names their laptop “chaos goblin” and means it legally. If you are shaping public-facing proof, framing Kioptrix Level for LinkedIn can help you keep the tone professional without draining all personality from the story.
Describe Methods, Constraints, and Judgment
A mature summary includes 3 things:
- Method: What kind of practice did you perform?
- Constraint: What boundary or scope shaped the work?
- Judgment: What decision did you make based on evidence?
Example:
“In a local Kioptrix lab, I practiced baseline enumeration and web service review, documented confirmed findings separately from assumptions, and used failed hypotheses to refine my next testing path.”
That sentence is compact. It is also miles better than “I hacked a VM.”
The Sentence Formula for a Mature Portfolio Summary
Use this formula:
In a legal lab environment, I practiced [skill], observed [evidence], decided [action], and learned [reflection].
Examples:
- “In a legal lab environment, I practiced service enumeration, observed several exposed services, prioritized web review, and learned to separate confirmed facts from guesses.”
- “In a legal lab environment, I practiced documenting failed hypotheses, observed that one lead had no confirmed support, paused it, and learned to return to enumeration sooner.”
- “In a legal lab environment, I practiced using references responsibly, checked a hint only after writing my assumptions, and learned to keep my own voice in the notes.”
This language shift closes the curiosity loop from the beginning of the article. The goal was never to make Kioptrix look louder. The goal was to make your learning easier to trust.
FAQ
Is Kioptrix Level Still Useful for Beginners?
Yes, Kioptrix Level can still be useful for beginners when used as a controlled learning lab rather than a race. Its value comes from practicing enumeration, observation, service research, note-taking, and reflection. The machine itself is not the whole point. Your repeatable process is. Beginners who need a gentler doorway can also use Kioptrix for beginners to build confidence before turning notes into portfolio material.
Can I Put Kioptrix Practice on a Cybersecurity Resume?
You can mention Kioptrix practice on a resume if you frame it carefully. Keep it brief and skill-focused. For example: “Completed local cybersecurity lab practice focused on enumeration, documentation, and web service analysis.” A personal portfolio or GitHub write-up is usually a better place for the detailed story.
How Much Detail Should I Include in a Kioptrix Write-Up?
Include enough detail to show your reasoning, but not so much that the write-up becomes a raw terminal dump. A strong entry usually includes scope, goal, key observations, decision points, a few evidence screenshots, failed hypotheses, and a short reflection. For polish, use Kioptrix report writing tips to decide what belongs in the public version and what should stay in private notes.
Should I Mention Failed Attempts in My Portfolio?
Yes, if the failed attempt taught you something useful. Describe it calmly. Say what you expected, what happened, and how it changed your next step. Avoid turning the section into a confession booth. The point is learning, not self-punishment.
Is It Okay to Use Walkthroughs While Learning Kioptrix?
Yes, but use them with discipline. Try first, write your facts and guesses, then read only enough to choose a next direction. Afterward, close the reference and continue in your own words. That protects retention and keeps your portfolio honest.
How Do I Avoid Sounding Like I Am Bragging About Hacking?
Use skill language instead of conquest language. Say “practiced enumeration,” “documented assumptions,” “validated evidence,” and “reflected on failed hypotheses.” Also mention that the work happened in a legal lab environment. Professional clarity beats theatrical swagger.
What Screenshots Should I Include in a Kioptrix Learning Log?
Include screenshots that support a specific point: lab environment, scan summary, notable service clue, important decision point, or final learning result. Avoid screenshot hoarding. A few meaningful images are stronger than a gallery of unexplained terminal windows.
How Many Kioptrix Sessions Are Enough to Show Consistency?
Four well-documented sessions can show more consistency than one long write-up. Try documenting baseline enumeration, narrowing the attack surface, testing one path, and final reflection. The pattern matters more than the number.
Next Step: Create One Small Learning-Consistency Entry Today
Open a Blank Note With Three Sections: Facts, Guesses, Next Action
Do not wait until you have a perfect lab story. Start with a small entry today.
Create 3 headings:
- Facts: Confirmed observations only.
- Guesses: Possible leads, clearly labeled.
- Next Action: One concrete step for the next session.
This tiny structure can rescue you from the classic beginner swamp: lots of activity, little memory. It also makes your progress visible before the final result appears. If your notes keep scattering across files, a dedicated Kioptrix note-taking tool can give your learning trail a stable home.
Run One Legal Lab Session and Stop Before the Notes Get Foggy
Set a timer for 30 minutes. Work inside your legal Kioptrix lab. Run one focused enumeration or review task. Then stop and write. Stopping is not weakness. Stopping is how you keep the lesson from dissolving into terminal soup.
For broader testing discipline, OWASP’s Web Security Testing Guide is a useful public reference because it treats testing as a structured process that includes information gathering, analysis, and reporting. That mindset pairs well with lab-based learning.
Write a 5-Sentence Reflection That Future You Can Actually Use
End with 5 sentences:
- Today I practiced…
- I confirmed…
- I guessed…
- I was wrong about…
- Next time I will…
That is enough. Not forever, not for a book, not for a grand reveal. Enough for a real learning trail.
- Use facts, guesses, and next action.
- Stay inside legal lab scope.
- Write reflection before memory fades.
Apply in 60 seconds: Create the three headings now and fill in one line under each.
Kioptrix does not have to become a loud story about “hacking.” It can become something better: a record of patience, method, curiosity, and repair. The kind of record that says, quietly but firmly, “I can keep learning when the answer is not obvious.”
That is the portfolio signal worth building.
Your 15-minute next step: open one blank note, write your legal lab scope, list 3 confirmed facts, and end with 1 next question. Small enough to do today. Strong enough to start a trail.
Last reviewed: 2026-04.