
Kali Rolling & The Ruby Bundler Conflict
A Kali Rolling update can break msfconsole in under five minutes—not because Metasploit “suddenly sucks,” but because Ruby and Bundler quietly stopped agreeing on who’s in charge. One package moves, one lockfile stays, your shell picks the “wrong” Bundler first… and the whole framework trips over a version contract it didn’t write.
If you’re seeing Bundler-flavored errors after apt upgrade—lockfile complaints, “bundler requires Ruby…”, missing gems, or “cannot load such file”—the worst move is random reinstalls and global gem install band-aids. The cost isn’t just wasted time; it’s a Franken-Ruby that breaks something else the next day, right when you actually need the lab to run. (If your broader lab setup has been “accumulating fixes,” it’s worth revisiting a stable baseline like Kali Linux lab infrastructure mastery so your tooling stays predictable.)
This guide treats the failure like an operator would: capture the first meaningful lines, prove which Ruby/Bundler msfconsole is actually invoking, then choose the cleanest fix—either snap back to Kali’s packaged metasploit-framework (lowest drama) or rollback + pin the small set of versions that regressed so the next update doesn’t re-break you.
I’ll also show you a 60-second post-update smoke test and a “break-glass” note template that turns future breakage into a boring, predictable routine.
If msfconsole broke after a Kali Rolling update, don’t “reinstall everything” yet. This is usually a Ruby/Bundler mismatch + PATH/gem-path precedence: Metasploit expects the distro-packaged Ruby/Bundler/gems, but your system is invoking a different Bundler/Ruby first. Capture the exact error, verify which Ruby/Bundler msfconsole actually uses, then either realign to Kali packages (safer) or rollback + pin the breaking versions so the next update doesn’t re-break you.
Table of Contents
Who this is for / not for
For you if: you ran apt upgrade or apt full-upgrade on Kali Rolling, and now msfconsole fails with something Bundler-ish: “lockfile,” “could not find gem,” “bundler requires Ruby,” or a mysterious “cannot load such file.”
Not for you if: you intentionally installed Metasploit via a Ruby manager (RVM/rbenv/ruby-build) and mixed it with Kali packages. That’s not “wrong,” but it’s a different game with different rules—and it’s easy to accidentally build a Franken-Ruby. (If you’re building a broader operator workflow, keeping your shell environment sane—like a clean, repeatable Zsh setup for pentesters—helps prevent “my shell chose chaos” moments.)
- Apt-only: you install Metasploit with Kali packages and rarely use
gemdirectly. - Mixed gems: you’ve run
gem install …orbundle install“just to fix it once.” - Ruby manager: you use rbenv/RVM and have multiple Rubies installed.
- ARM/RPi: you’re on Raspberry Pi or another ARM device where packages can behave differently.
Next action: Pick the label that fits you and keep it in mind—your “type” determines which fix path is safest.
Personal confession: the first time I hit this, I assumed I’d “broken Metasploit.” Turns out I’d only broken the relationship between Metasploit, RubyGems, and Bundler. Like a band with the right musicians… playing in different keys.
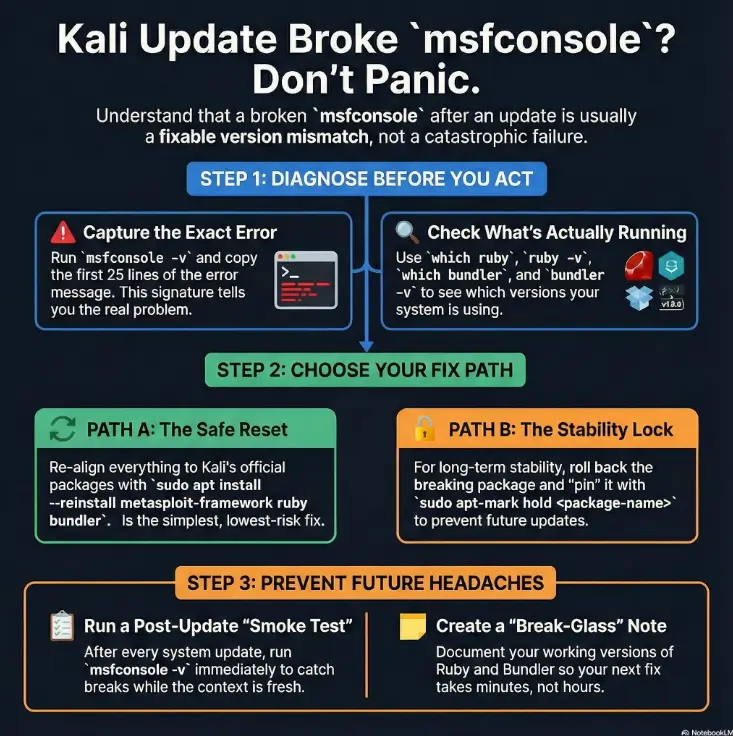
msfconsole broke today: capture the exact error first
Before you run a single “fix” command, grab the first meaningful chunk of the failure. I know it feels slow. But the difference between a Ruby version mismatch and a missing gem is often one line.
Paste the first 25 lines (the part that matters)
Run:
msfconsole -v
msfconsoleCopy the first ~25 lines of output (especially the first stack trace). That’s your “symptom signature.”
Classify it fast: Ruby version / Bundler lockfile / missing gem / OpenSSL symbol
- Ruby version mismatch: “bundler requires Ruby X” / “Your Ruby version is … but … required.”
- Bundler lockfile mismatch: “Your lockfile was created by an old Bundler version” / “You must use Bundler …”
- Missing gem: “Could not find gem … in any of the gem sources.”
- OpenSSL symbol / native extension: “symbol not found” / “cannot load such file openssl” / “LoadError … openssl.so.”
Curiosity gap: the one line that predicts the right fix path
If the error mentions Bundler and Ruby in the same breath, your fix is usually about which Ruby/Bundler is being invoked—not “reinstall Metasploit.” If it mentions OpenSSL symbols, you’re in library/ABI territory (we’ll cover that later).
- Bundler+Ruby wording = resolution order problem.
- Missing gem wording = gem path / package state problem.
- OpenSSL symbol wording = native library mismatch problem.
Apply in 60 seconds: Copy the first 25 lines of the error into a scratch note before touching anything.
Operator reality: “random fixes” work sometimes, but they also create weird side-effects you only discover later—usually 10 minutes before you planned to actually use Metasploit.
Ruby/Bundler reality check: what msfconsole is actually invoking
Here’s the sneaky part: your system can be “correct” and still be wrong. Kali packages may be fine, but your shell could be selecting a different Ruby or Bundler first. And Bundler is extremely literal—like a bouncer checking IDs under a bright flashlight.
Check 1 — Which msfconsole binary are you launching?
which msfconsole
type -a msfconsoleIf you see multiple entries, you’ve already found a clue. “Multiple entries” is how you get a perfectly normal day that ends in an error message.
Check 2 — Which Ruby loads first (system vs userland)?
which ruby
ruby -v
ruby -e 'puts RbConfig.ruby'If you use rbenv/RVM, which ruby can change based on shell initialization. That’s not evil. It’s just… chaotic when mixed with distro packages.
Check 3 — Which Bundler runs first (and from where)?
which bundler
bundler -v
bundle -vBundler versions matter because the lockfile encodes expectations. A lockfile created under one Bundler series can fail under another, even if the gems are “almost” the same.
Let’s be honest… PATH precedence breaks more labs than Bundler does.
I’ve watched smart people lose 45 minutes to this: they were fixing Metasploit, but the real issue was their shell politely choosing the wrong Ruby first. If you’re juggling multiple VMs or network modes, drift can hide in unexpected places—especially when your Kali workflow lives in VirtualBox; keeping your VM networking consistent (see VirtualBox NAT vs Host-Only vs Bridged) reduces “it worked yesterday” variables while you debug Ruby/Bundler today.
Show me the nerdy details
PATH precedence is a deterministic “first match wins” search. If your shell finds a user-installed Bundler before the distro Bundler, it will use it—even if your Metasploit package expects the distro environment. The same applies to Ruby, gem home paths, and vendor gem directories. When multiple ecosystems coexist, you need to verify which one is active rather than assuming.
- The first 25 lines of the
msfconsoleerror. which msfconsoleandtype -a msfconsoleoutput.ruby -vandbundler -v.- Whether you use rbenv/RVM (even “a long time ago”).
Next action: Save these outputs in a note titled “msfconsole break — before fixes.”
One more lived-experience moment: I once “fixed” msfconsole by installing Bundler globally. It launched. I celebrated. Then another tool that depended on distro Ruby broke the next day. That’s the tax you pay for quick wins without a map.
Gemfile.lock tells the truth: what Bundler expects
When people say “just run bundle install,” they’re accidentally skipping the part where Bundler asks, “Under what universe?” Your Gemfile.lock is the universe definition.
What the lockfile is really pinning (Bundler + Ruby assumptions)
A lockfile captures:
- Exact gem versions (and their dependency constraints).
- The Bundler version family it expects (often implicitly).
- Platform constraints that can matter on ARM vs x86.
The mismatch patterns in plain English
- “Old Bundler lockfile” errors usually mean: you’re running a different Bundler generation than the lockfile expects.
- “Could not find gem …” often means: the gem exists in the package ecosystem you’re not using, or your gem path is pointing somewhere incomplete.
- “Bundler requires Ruby …” means: the current Ruby can’t satisfy the declared constraints. No amount of optimism will change that.
Open loop: why a “correct” lockfile can still fail on Kali Rolling
Kali Rolling does what rolling distros do: it moves. If Ruby or Bundler moved forward, and Metasploit’s packaged gem set hasn’t aligned yet (or your shell pulls a different Bundler first), you can end up with a lockfile that’s internally consistent but externally incompatible with what’s being invoked.
- The lockfile defines the contract.
- Your active Ruby/Bundler must be compatible with it.
- Rolling updates can change the “active” tools without warning.
Apply in 60 seconds: Decide now: “am I returning to Kali’s packaged world, or maintaining my own Ruby world?”
Small comedic truth: Bundler doesn’t care about your deadline. It cares about versions. It’s like a metronome—unhelpful until you realize it’s keeping time so the band doesn’t collapse.
Fix path A: snap back to Kali-packaged Metasploit (lowest risk)
If you’re “apt-only” or “mostly apt,” this is usually the lowest-drama fix: get back to the distro-supported Ruby/Bundler/gem set and stop fighting your own machine. (This is the same philosophy behind keeping your baseline tooling tight—start from essential Kali tools, then add only what you can maintain.)
When path A is the right call (most apt-only installs)
- You didn’t intentionally set up a Ruby dev environment.
- Your goal is stability (labs, training, repeatable tooling), not Ruby experimentation.
- Your error started immediately after an apt upgrade.
Re-align to distro Ruby/Bundler instead of user gems
Start by confirming you’re not accidentally using a Ruby manager’s shims. Then, consider reinstalling the relevant packages cleanly so Metasploit and Ruby are aligned as Kali intends.
sudo apt update
sudo apt --fix-broken install
sudo apt install --reinstall metasploit-framework ruby bundlerIf your system is partially upgraded, fix that first. A half-upgraded state is where “mystery errors” breed.
Verify with a clean-shell launch (no hidden env vars)
Open a fresh terminal (or run a clean shell), then:
env -i HOME="$HOME" PATH="/usr/sbin:/usr/bin:/sbin:/bin" bash --noprofile --norc
msfconsole -vIf it launches in a clean environment but fails in your normal shell, you’ve basically proven the culprit: PATH precedence or shell init scripts. Kali’s Metasploit Framework guidance is the canonical “what Kali expects” reference.
My “been there” moment: I once spent 30 minutes reinstalling Metasploit, only to discover my shell was still calling a different Ruby because I’d installed rbenv months earlier for an unrelated project. Reinstalling didn’t change the selection order—so it didn’t change the outcome.
Fix path B: pin + rollback the breaking versions (stay-fixed strategy)
This path is for when you need Metasploit working and you don’t want the next Rolling update to undo your life choices. It’s also for when your environment must stay stable for weeks: a course, a lab sprint, a client assessment prep run. (No heroics required. Just boring stability.)
Find what changed (the smallest rollback that works)
The safest philosophy is “rollback the smallest set that restores compatibility.” You’re usually hunting changes in:
- Ruby (minor or patch upgrades can shift compatibility boundaries)
- Bundler (lockfile expectations)
- metasploit-framework package version
- native deps like OpenSSL (for extension loading issues)
Roll back only what you must (avoid collateral damage)
First, list recent package changes and candidates:
grep -i "upgrade " /var/log/dpkg.log | tail -n 40
apt-cache policy ruby bundler metasploit-framework | sed -n '1,160p'If an older compatible version is available in your configured repos, you can downgrade selectively. If it’s not available, you may need to use snapshots/backups or accept path A temporarily.
Pin intentionally: what to freeze vs what to let float
Pinning is a tool, not a lifestyle. The goal is to freeze only the packages that create the mismatch—while letting security updates proceed elsewhere.
sudo apt-mark hold ruby bundler metasploit-frameworkThat’s a blunt instrument, but it works as a temporary “stop the bleeding” move. The more precise approach uses apt preferences so you can pin versions deliberately.
Here’s what no one tells you… pins without a note become future sabotage.
You will forget you pinned things. Future You will run an upgrade, wonder why packages won’t move, and lose 20 minutes accusing the universe. Leave a note. Make it unmissable.
Show me the nerdy details
Apt pinning and holds are safety rails for rolling environments. Holds stop upgrades entirely for selected packages; pinning can bias the resolver toward specific versions/releases. Use them as temporary stabilizers, not permanent crutches. When you’re ready, you can undo holds with apt-mark unhold and remove pin files from apt preferences.
- Rollback the smallest set that fixes compatibility.
- Hold or pin only what’s necessary.
- Document what you froze so you can unfreeze safely later.
Apply in 60 seconds: If you need msfconsole working today, place a temporary hold and write a one-line note about why.
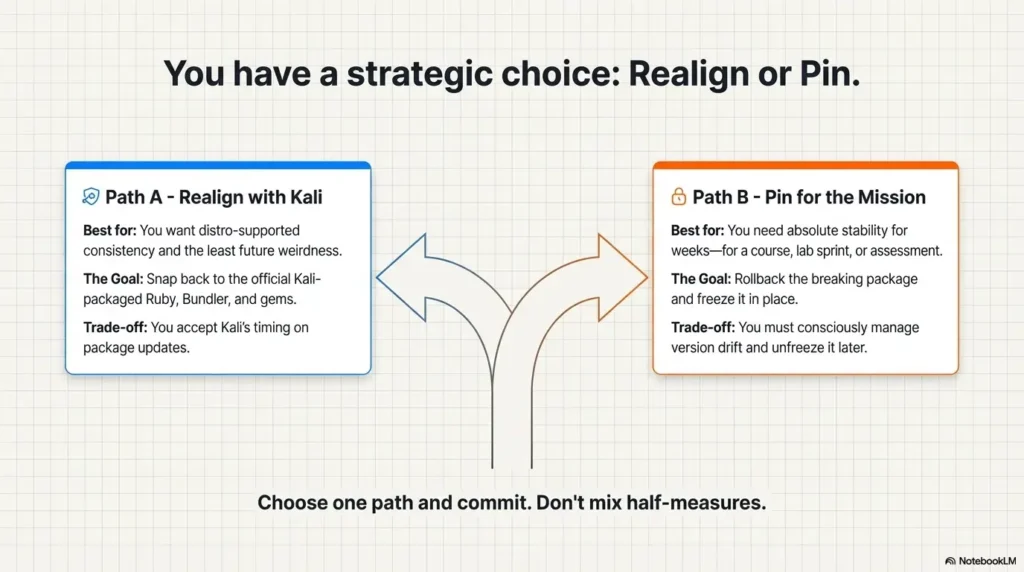
- You want distro-supported consistency.
- You don’t need custom Ruby tooling.
- You want the least “future weirdness.”
Trade-off: you accept Kali’s timing on package alignment.
- You need stability for weeks.
- You can tolerate “frozen” packages temporarily.
- You’re willing to document and unfreeze later.
Trade-off: you manage version drift consciously.
Next action: Circle A or B in your notes, then follow one path fully—don’t mix half-measures.
One more candid anecdote: the first time I used holds, I felt like I was “doing something wrong.” Then I realized every stable environment is just a series of controlled compromises. Stability is not accidental—it’s curated.
Common mistakes: the 5 moves that make it worse
This section exists to save you from the kind of “fix” that works at 2:03 PM and ruins your day at 5:47 PM.
Mistake #1 — Treating Kali like a Ruby dev box (mixing apt + gem installs)
Kali is fantastic, but it’s not a blank canvas. If you install gems globally with RubyGems while also depending on distro-packaged gems, you create overlapping ecosystems. Bundler will pick one and complain loudly about the other.
Mistake #2 — Running fixes inside a root shell (it changes gem behavior)
Running as root can change gem paths, permissions, and where Bundler writes. That’s why you sometimes see “it works as root but not as user” (or vice versa). It’s not magic. It’s paths.
Mistake #3 — Deleting gem directories at random
Deleting directories feels clean. It’s also the fastest way to break other tools that share Ruby dependencies. Prefer reversible actions: reinstall packages, undoable holds, and documented changes.
Mistake #4 — “Bundle install” without matching Bundler version
If the lockfile expects a different Bundler generation, forcing bundle install can mutate the environment in a way that’s hard to unwind. Sometimes you “fix” Metasploit but quietly damage reproducibility.
Mistake #5 — Upgrading with a broken repo state (partial upgrades)
If your apt sources are broken or you’re getting repository errors, you can end up partially upgraded. Partial upgrades are where version mismatches multiply. Fix your update pipeline first, then troubleshoot Metasploit. (If your failures started “right after a Windows update” in a dual-boot setup, fix boot stability first—see Kali dual boot GRUB recovery after Windows updates—then come back to Ruby/Bundler.)
- Apt-only is simplest and most repeatable.
- Root shells change the rules without warning.
- Random deletions create invisible damage.
Apply in 60 seconds: If you’ve been mixing apt and gem installs, decide which world you’re committing to for this machine.
Light humor, but true: the quickest way to become a Linux wizard is to break something in a creative way, then write down what you did so you can un-break it later. Documentation is basically time travel.
Edge cases that look similar: OpenSSL symbols, ARM/RPi, and repo drift
Not every crash is Bundler. Some failures wear Bundler’s outfit but are actually about native libraries, architecture differences, or a broken upgrade pipeline.
OpenSSL symbol errors (Ruby extension can’t load)
If you see errors that mention missing symbols or failing to load openssl.so, you’re likely dealing with an OpenSSL/Ruby extension mismatch. This can happen when OpenSSL libraries move forward and a native extension expects a different ABI.
In human terms: Ruby is trying to plug into OpenSSL, and the socket shape changed.
ARM/Raspberry Pi installs: packaging can differ (expect surprises)
On ARM (including Raspberry Pi), package availability and build variants can differ. If you’re on ARM and seeing repeated weirdness, lean toward distro-aligned installs and avoid mixing Ruby managers unless you truly need them.
sources.list / Release file / hash mismatch: fix the upgrade pipeline first
If apt is throwing repository errors (release file issues, hash mismatches, wrong suite names), Metasploit may be only partially upgraded. In that state, you can end up with incompatible combinations of Ruby, Bundler, and dependencies.
Show me the nerdy details
Native extension errors often point to ABI mismatches: a compiled extension links against a library version whose exported symbols differ from what’s currently installed. Rolling upgrades can change libraries like OpenSSL; if an extension was built for an older symbol set, it may fail to load. In such cases, reinstalling the package that provides the extension (or re-aligning to distro builds) is generally safer than manual gem compilation on a security-focused distro environment.
Most likely: wrong Ruby/Bundler invoked (PATH/gem precedence).
Go to: “Ruby/Bundler reality check” → Fix path A or B.
Most likely: Bundler generation mismatch vs lockfile expectations.
Go to: “Gemfile.lock tells the truth” → Fix path A or B.
Most likely: native extension / ABI mismatch.
Go to: “Edge cases” → re-align packages.
Accessibility note: This flowchart maps error signatures to the safest troubleshooting section.
Quick lived moment: I once chased a Bundler fix for 20 minutes before noticing the error mentioned OpenSSL symbols. That’s like trying to fix a flat tire by adjusting the radio. The system was yelling the truth—I just wasn’t listening.
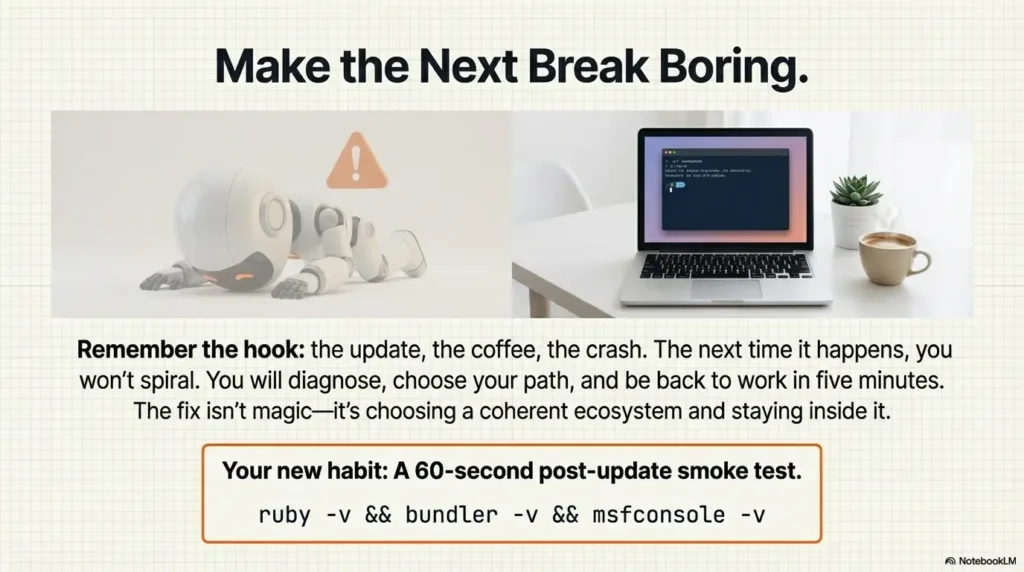
Make it survive Rolling: a 60-second post-update smoke test
Rolling distros reward routine. The easiest way to prevent late-night surprise breakage is a tiny post-update check. Not because you’re paranoid—because you’re tired.
Smoke test 1 — msfconsole -v launches cleanly
msfconsole -vIf this fails, stop and troubleshoot immediately while the change context is fresh.
Smoke test 2 — DB readiness (only if you use it)
If you use PostgreSQL-backed features, confirm your DB setup is healthy. Kali and Metasploit workflows vary here, so keep this lightweight and aligned with your habits.
Smoke test 3 — One basic module action (sanity, not exploitation)
Pick a harmless sanity action that proves the framework loads modules and responds. The point is “framework is coherent,” not “do anything risky.”
Curiosity gap: the single command that reveals “drift” early
After upgrades, run:
ruby -v && bundler -v && which ruby && which bundlerThis tiny bundle of facts tells you if your environment silently changed under your feet.
- Input 1: Do you use rbenv/RVM on this machine? (Yes/No)
- Input 2: Do you need msfconsole stable for > 2 weeks? (Yes/No)
- Input 3: Does msfconsole work in a clean shell but fail in your normal shell? (Yes/No)
Output: If (Input 3 = Yes) → focus on PATH precedence. If stability > 2 weeks → prefer rollback+pin. If Ruby managers are involved → avoid mixing fixes; choose one ecosystem and commit.
Next action: Write your three answers in one line, then follow the matching fix path fully.
Short Story: The night I learned “rolling” means rolling… (120–180 words) …
Short Story: I once updated Kali Rolling before a weekend lab sprint—because I wanted “fresh tools.” The update finished fast, and I felt smug for exactly eight minutes. Then msfconsole wouldn’t launch. I did what everyone does: Googled, copied a couple commands, and eventually got it working.
But the next morning, a different tool that depended on Ruby started failing, and I couldn’t remember which fix caused which break. The worst part wasn’t the error; it was the uncertainty. After that, I started doing two boring things: I captured the first 25 lines of errors, and I wrote a tiny recovery note after any fix. It didn’t make me feel smarter. It just made me faster—and honestly, a little calmer. …
FAQ
Why did msfconsole break right after apt upgrade?
Because Rolling updates can change Ruby/Bundler and dependencies quickly. If Metasploit expects a distro-packaged toolchain but your shell invokes a different Ruby/Bundler (or packages are partially upgraded), Bundler will refuse to proceed. The fix is to verify what’s being invoked, then either re-align to Kali packages or rollback+pin temporarily.
What does “Unable to find a spec satisfying metasploit-framework” mean?
It usually means Bundler can’t locate the required gem version in the gem paths it’s currently searching. That can happen if your gem ecosystem is split (apt gems vs user gems), if installs were performed under a different user/root context, or if the environment is in a partial upgrade state.
Why does “Your lockfile was created by an old Bundler version” show up?
Bundler versions are not always interchangeable with lockfiles. If your active Bundler is newer or older than what the lockfile expects, Bundler may refuse or behave unexpectedly. The stable approach is to use the Bundler that matches the environment Metasploit was packaged for—or return to Kali’s packaged ecosystem.
Is it safe to run sudo gem install bundler on Kali?
It can “work,” but it often creates a mixed ecosystem where RubyGems-installed Bundler competes with Kali’s packaged Bundler. That’s how you get a short-term win and long-term weirdness. If you do it, treat it as a conscious choice, document it, and be ready to manage that ecosystem going forward.
Can running as root cause Metasploit gem/bundler weirdness?
Yes. Root vs user context can change gem install locations, permissions, and environment variables. You can end up with gems installed under root-owned paths that your normal user can’t read (or vice versa), which looks like random missing-gem failures.
What does an OpenSSL “symbol not defined” error mean in Ruby?
It usually indicates a native extension was compiled against a different library symbol set than what’s currently installed. In Rolling environments, libraries like OpenSSL can move forward; re-aligning packages (or reinstalling the dependent package) is typically safer than manual compilation in a mixed environment.
Should I pin packages on Kali Rolling, or is that “bad practice”?
Pinning is a practical tool when you need stability. The key is to pin narrowly and temporarily, and to document what you pinned and why. That way, you can unpin later when the packaging ecosystem catches up.
How do I undo pins later without re-breaking Metasploit?
Undo holds gradually: unhold one package at a time, upgrade, and rerun your 60-second smoke test. If you used apt preferences pinning, remove or adjust the pin file, then upgrade in a controlled step rather than a big surprise leap.
Why does my update fail with Release-file or hash-sum errors?
Those errors usually point to repository configuration issues or mirror problems. Fix your apt pipeline first, then retry upgrades. Troubleshooting Metasploit on top of a broken update pipeline is like painting a wall while it’s still wet underneath.
Is Metasploit “supposed” to come preinstalled on Kali?
Kali has strong first-class support for Metasploit and related tooling, and many Kali environments include it or make it easily installable through packages. The simplest approach is to keep Metasploit aligned with Kali’s packaging unless you have a specific reason to maintain a separate Ruby toolchain. If you’re building out a learning stack around Kali, a curated list like pentesting tools you’ll actually use can help you keep installs intentional instead of “whatever fixes the error today.”
Next step: write your “break-glass” recovery note (one action)
This is the part that pays you back later. Write a tiny note. Not a blog post. Not a masterpiece. A scrap.
Save these 6 facts: msf version, Ruby, Bundler, gem paths, pinned packages, last-good date
Title: msfconsole break-glass note
1. msfconsole version: (output of msfconsole -v)
2. Ruby version + path: ruby -v ; which ruby
3. Bundler version + path: bundler -v ; which bundler
4. msfconsole path: which msfconsole
5. Holds/pins: apt-mark showhold (and any apt preferences notes)
6. Last known-good date: YYYY-MM-DDThis note is how you keep your future self from doing forensic archaeology at midnight. If you want real-world issue context and troubleshooting prompts, see Rapid7’s post-update breakage discussion.
Commercial-entity sanity check (neutral, real-world): the ecosystem you’re juggling here includes Kali Linux packaging, Rapid7’s Metasploit Framework, RubyGems and Bundler behavior, OpenSSL library compatibility, and sometimes PostgreSQL depending on how you use Metasploit. Naming the pieces helps you diagnose the right one instead of punching the whole stack.
Conclusion: make the next break boring
Remember the hook: a “normal” update, a cup of coffee, and suddenly msfconsole refuses to start. The open secret is that it’s rarely a mystical Metasploit failure. It’s usually version contracts and resolution order—Ruby/Bundler/gem paths deciding who speaks first.
If you take only one lesson: verify what msfconsole is actually invoking before you change anything. Then pick one path and commit: snap back to Kali’s packaged world for repeatable stability, or rollback+pin for controlled consistency through a training sprint. Either way, leave the break-glass note. Your future self will feel seen.
- Capture the error signature first.
- Confirm Ruby/Bundler selection order.
- Stabilize with re-align or rollback+pin, then document.
Apply in 60 seconds: Run the 60-second smoke test right now—before the next lab session.
Your next 15-minute move: open a fresh terminal, run the smoke test (ruby -v, bundler -v, msfconsole -v), and write the break-glass note while everything is still on-screen. That’s the fastest way to turn a fragile setup into a dependable one.
Last reviewed: 2025-12.

