
50 Pentesting Tools You’ll Actually Use (Sorted by Category) — My Shocking “No-Fluff” Stack
Stop Collecting Tools.
Start Building a Stack That Survives Stress.
I lost 47 minutes once to a “perfect” pentesting setup that didn’t produce a single defensible finding. That was the moment I stopped collecting tools—and started building a stack that survives stress.
Most people don’t struggle because they lack pentesting tools. They struggle because they install everything, then can’t decide what to run first, what’s safe in scope, or what actually turns into clean evidence (requests, responses, timestamps, impact).
Keep guessing and you lose the only two resources that matter on an engagement: time and credibility.
Pentesting tools are the software (and sometimes hardware) used to discover, validate, and document security weaknesses—typically across recon/OSINT, scanning and enumeration, web testing (proxies), internal/Active Directory work, and reporting—so findings are reproducible and fixable.
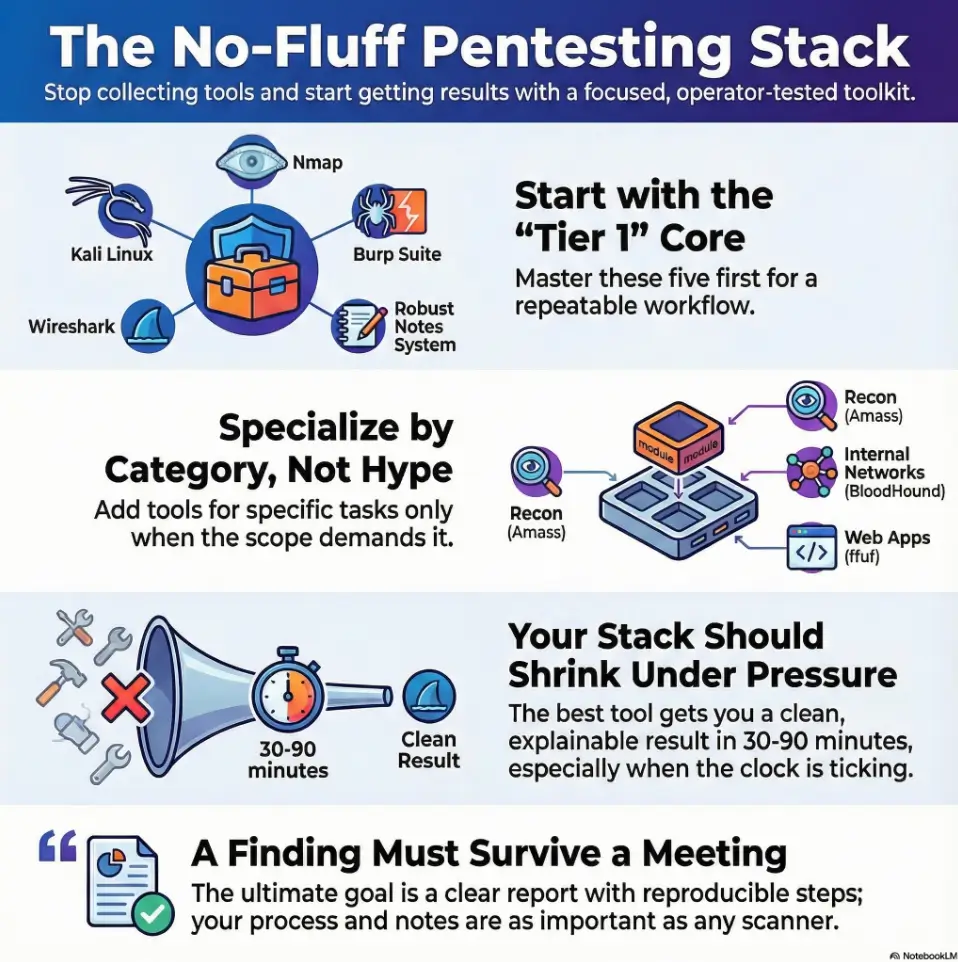
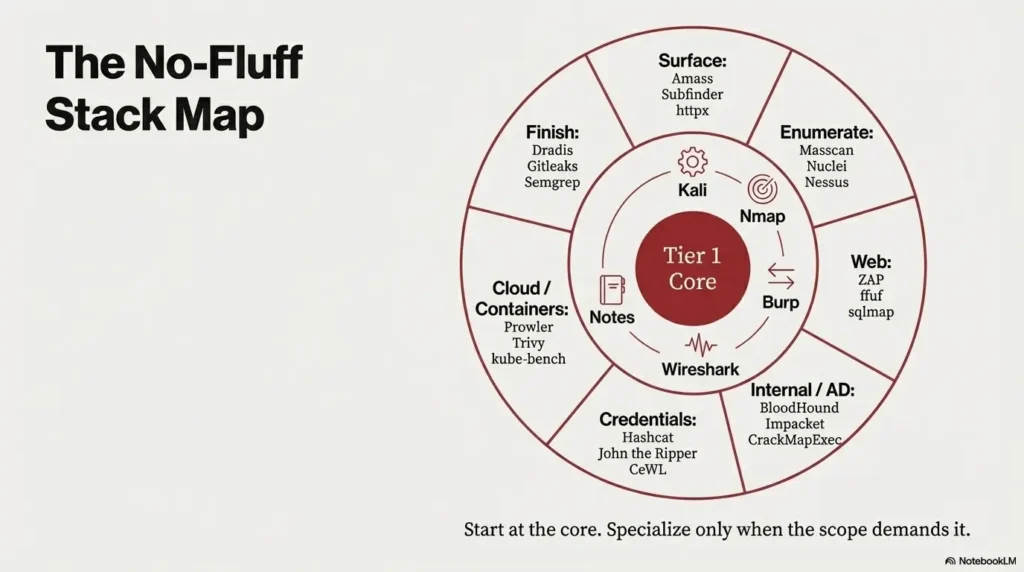
This stack helps you install the right five first, then expand by category only when scope demands it—Nmap for fast discovery and nuclei for triage, Burp Suite/OWASP ZAP for web proof, BloodHound for AD paths, and a reporting workflow that doesn’t collapse in meetings. It’s built around operator triggers: “when to grab what,” and how to keep your stack smaller under pressure.
Table of Contents
How to use this list without tool-hoarding
Rule one: only use tools you’re authorized to use. Written permission beats “but I was curious” every day of the week. This stack is meant for legitimate pentests, internal security work, lab practice, and sanctioned assessments.
Rule two: pick tools by decision pressure, not hype. If your job is to ship findings, the “best” tool is the one that gets you to a clean, explainable result in 30–90 minutes, not the one with the coolest logo.
- Start with Tier 1 tools that show evidence fast
- Add category tools only when the scope demands it
- Keep one “boring” reporting system to finish strong
Apply in 60 seconds: Open your last report and list the tools you actually used—those are your real Tier 1.
- Yes/No: Do you have written authorization and defined scope?
- Yes/No: Do you need web testing, internal network testing, or both?
- Yes/No: Are you expected to deliver a report with reproducible steps?
- Yes/No: Do you have a lab or change window to validate safely?
- Next step: If any answer is “No,” fix that before adding tools.
Save this checklist and confirm scope details on the official engagement paperwork.
My personal mistake: I once installed “everything,” then froze when a client asked, “Which tool produced this evidence?” I had screenshots, but no chain of reasoning. That was a two-hour lesson that felt like a week.
Tier 1 core stack you install first
If you only install five things today, make it these: an OS you can rebuild, a scanner, a proxy, a packet tool, and a note/report system. The goal is not perfection—it’s repeatability. Think: “Can I rerun this tomorrow and get the same evidence in under 20 minutes?”
| Tool | What you actually use it for | My “grab it when…” trigger |
|---|---|---|
| Kali Linux | A sane baseline environment with common tooling | I need a rebuildable VM in 15 minutes |
| Nmap | Service discovery and quick risk clues | I need the “what’s even here?” map in <30 |
| Burp Suite | Web traffic inspection and controlled testing | A login flow feels “weird” and I need proof |
| Wireshark | Packet truth when logs lie | Someone says “it’s encrypted” and I verify |
| Obsidian (or any notes) | Evidence, timelines, and reproducible steps | I want the report half-written by day one |
Show me the nerdy details
Repeatability beats novelty. Use snapshots for your VM, track tool versions, and keep a single “evidence template” note with sections for scope, target, timestamps, requests/responses, and screenshots. It’s boring. It also saves 60–120 minutes when you write the report.
Quick reality check: If your Tier 1 stack can’t produce a clean finding, adding 45 more tools won’t fix the process. It just gives you more ways to get distracted.
Recon and OSINT that stays legal
Recon is where you can waste the most time while feeling productive. I’ve watched people spend 2 hours on OSINT and still not know what to test first. Do recon that feeds your next concrete move: endpoints, tech stack hints, and exposed surfaces.
| Tool | Best use | Why it earns a spot |
|---|---|---|
| Amass | Attack surface mapping for domains | Turns “maybe subdomains” into a test list |
| Subfinder | Fast subdomain discovery | Speed when the clock is rude |
| httpx | Which hosts are actually alive | Cuts noise in 10 minutes, not an afternoon |
| theHarvester | Public emails, hosts, names | Helps craft realistic scenarios for defense |
| Shodan | Internet-exposed asset clues | Great for scoping risk, not “spraying” tests |
My “shocking” habit: I timebox recon to 25 minutes. If I can’t name the first test after that, I’m not doing recon—I’m avoiding work.
Scanning and enumeration that doesn’t waste hours
Scanning is a place where “more” feels safer. It isn’t. A smart scan answers a question: “What services matter, and what’s the fastest path to validate risk?” Keep your scan output explainable. If you can’t explain why you scanned it, you probably shouldn’t.
| Tool | Best use | Operator note |
|---|---|---|
| Masscan | Very fast port discovery | Use gently—speed can become chaos |
| Nuclei | Template-based checks | Great for triage, still requires validation |
| Nessus | Vuln scanning workflows | Good when reporting needs a structured trail |
| OpenVAS / Greenbone | Open vuln scanning option | Expect tuning; the defaults can be loud |
| netcat | Quick connectivity tests | The simplest tool can save 30 minutes |
Show me the nerdy details
Scan output is only “useful” if you can tie it to an identifier and impact. Use the CVE format when relevant, map common web issues to CWE identifiers, and when you talk tactics, keep a MITRE ATT&CK technique ID handy for framing. That structure reduces back-and-forth in review meetings by 20–40 minutes.
If your environment is the classic AMP stack, it helps to keep a simple reference for Apache/MySQL/PHP CVE mapping so you can explain “what this version means” without spiraling.
Web app testing that pays off fast
Web apps are where I’ve seen the biggest gap between “tool-heavy” and “result-heavy.” A good proxy setup plus a few focused helpers beats a dozen scanners that you can’t explain. If you only do one thing differently: capture clean evidence—requests, responses, timestamps, and the exact condition that changes behavior.
| Tool | Best use | Why it’s “actually used” |
|---|---|---|
| Burp Suite | Intercept, replay, organize tests | The workbench for web reality |
| OWASP ZAP | Proxy + scanning option | Solid free pick for many teams |
| ffuf | Fast discovery of hidden paths | Finds “forgotten” endpoints quickly |
| Gobuster | Directory and DNS brute-forcing | Simple, reliable, fast enough |
| sqlmap | SQL injection validation support | Use carefully; validate in scope only |
- Capture exact requests/responses as evidence
- Prefer small, controlled tests over loud automation
- Write the finding as you go
Apply in 60 seconds: Create a “Finding Template” note with fields for request, response, and impact.
Confession: My most embarrassing web miss was a one-line auth check bug I could have caught in 8 minutes—but I was busy running a scan I didn’t understand. If you want a clean mental model for “what a vulnerable app usually looks like,” keep a reference like vulnerable web app structure nearby so you don’t get hypnotized by tooling.
Active Directory and internal network essentials
Internal assessments often reward calm, methodical mapping. Your goal is to answer: “What can this identity do?” not “How many tools can I run?” When the environment is Windows-heavy, the tool choices get sharper and more predictable.
| Tool | Best use | What it replaces |
|---|---|---|
| BloodHound | Visualizing AD relationships and paths | A thousand confusing notes |
| Impacket | Windows protocol tooling for tests | Hand-rolled scripts under pressure |
| CrackMapExec | Internal validation workflows | Manual repetition across hosts |
| Responder | Controlled credential exposure tests | Guessing if a segment is “safe” |
| enum4linux-ng | SMB enumeration support | Scattershot commands |
Show me the nerdy details
For internal work, keep your notes tied to identities, not machines. Track “who you are,” “what you can reach,” and “what changed.” If you map a path, label it with a technique identifier (for example, an ATT&CK technique ID) so defensive teams can translate it into controls.
If you can’t (or shouldn’t) run BloodHound in an environment, it helps to keep an alternative workflow in your pocket—see AD profiling without BloodHound for a calmer, less “tool-dependent” approach.
- You need answers in <60 minutes
- The environment is fragile or rate-limited
- You’re validating one hypothesis
Tools: Nmap, httpx, Burp, Wireshark, notes
- You must show repeatable output
- Stakeholders want standardized evidence
- You need trend/coverage views
Tools: Nessus/OpenVAS, BloodHound, a reporting platform
Save this card and confirm which style matches your scope and reporting requirements.
Short Story: The day my “perfect stack” failed (120–180 words)
On one engagement, I arrived with a fresh VM, shiny aliases, and a folder full of “must-have” tools. I felt prepared—right up until the client’s network started throttling. My scans dragged. My dashboards stalled. My confidence did a slow, humiliating fade. Then I did something that felt almost childish: I opened a notes file, ran a small discovery pass, and checked one service by hand. Fifteen minutes later, I had a clean, explainable misconfiguration with screenshots and a clear impact statement. The fancy tooling wasn’t wrong. It just wasn’t right for that moment. That day taught me the quiet operator rule: your stack should work when the environment is messy, the clock is loud, and your brain is tired.
Passwords and credentials without drama
This category gets people emotional—fast. Keep it professional: you’re validating risk, not collecting trophies. If you handle credentials, treat them like live wires: minimize exposure, document handling, and follow engagement rules. Also: good wordlists and sane cracking workflows can save 1–3 hours compared to random guessing.
| Tool | Best use | Practical guardrail |
|---|---|---|
| Hashcat | Offline cracking validation | Use strict scope + retention rules |
| John the Ripper | Flexible cracking workflows | Great for quick checks and formats |
| CeWL | Target-themed wordlist building | More signal, less brute force |
| Crunch | Pattern-based wordlists | Use only when you have a real pattern |
| Kerbrute | Kerberos user validation tests | Be gentle; rate limits matter |
My rule: If I can’t explain how credentials will be handled in one sentence, I don’t touch this category yet. Not glamorous. Very sane.
Exploitation and post-exploitation with guardrails
Let’s be direct: these tools can be misused. Use them only in authorized work, and focus on controlled validation. In a real engagement, success is not “getting a shell.” Success is proving impact, limiting blast radius, and leaving the environment stable. Also, keep your “demo” steps reproducible: the report needs clarity more than swagger.
| Tool | Best use | Safer framing |
|---|---|---|
| Metasploit Framework | Controlled validation modules | Use to confirm, not to “spray” |
| Searchsploit | Offline exploit research index | Good for understanding, not auto-running |
| msfvenom | Payload generation for lab validation | Keep it lab-only unless scope is explicit |
| Sliver | Red-team style testing platform | Use only when rules are tight |
| Chisel | Tunneling for segmented tests | Document exactly what changed |
Show me the nerdy details
When you validate an issue, tie it to an identifier and a mitigation path. Use CVE identifiers when applicable, map to a CWE class for web issues, and describe the effect in business terms. “Remote code execution” sounds dramatic; “attacker can read customer records” is what leadership hears. That translation can cut review cycles by 1–2 days.
If you want a simple, repeatable arc for “what happens after RCE,” keep a tight reference like RCE → shell → privilege escalation so the work stays structured and explainable.
- Validate the smallest safe step
- Capture evidence cleanly
- Leave the environment stable
Apply in 60 seconds: Write a one-sentence “impact statement” before you touch an exploit tool.
Cloud and containers for modern environments
Cloud work punishes guesswork. It rewards inventory, permissions clarity, and boring checks. If you’re testing AWS/Azure/GCP, keep the scope crisp and document everything. A cloud finding without a clear permission path is a debate; a cloud finding with a permission path is a fix.
| Tool | Best use | What it helps you answer |
|---|---|---|
| Prowler | AWS security checks and posture | “What’s misconfigured?” |
| ScoutSuite | Multi-cloud auditing views | “What’s exposed at a glance?” |
| Trivy | Container image scanning | “What’s in this image?” |
| kube-bench | Kubernetes benchmark checks | “Is our config sane?” |
| kube-hunter | Kubernetes security probing | “What can an attacker see?” |
A small, honest number: A clean cloud permission map can save 45–90 minutes of confusion when you brief findings.
Wireless and near-field testing basics
Wireless testing is where people get tempted to “play.” Don’t. If you’re doing it professionally, keep the scope and environment explicit. Also: wireless problems often look like magic until you remember the boring basics—signal, encryption mode, and client behavior.
| Tool | Best use | Practical note |
|---|---|---|
| Aircrack-ng | Wi-Fi testing suite | Only in authorized environments |
| Kismet | Wireless discovery and monitoring | Great for visibility and inventory |
| hcxdumptool | Wi-Fi capture support | Keep logs and time windows clean |
| Bettercap | Network recon and interception lab work | Useful for demos with guardrails |
| Proxmark3 | RFID research and testing | Hardware-driven; be precise and ethical |
Local note: If you’re working in regions with strict radio and privacy rules (including South Korea and many EU countries), treat wireless testing like handling regulated equipment—get written approval, keep a defined physical boundary, and document timestamps. “We stayed in scope” should be provable in two sentences.
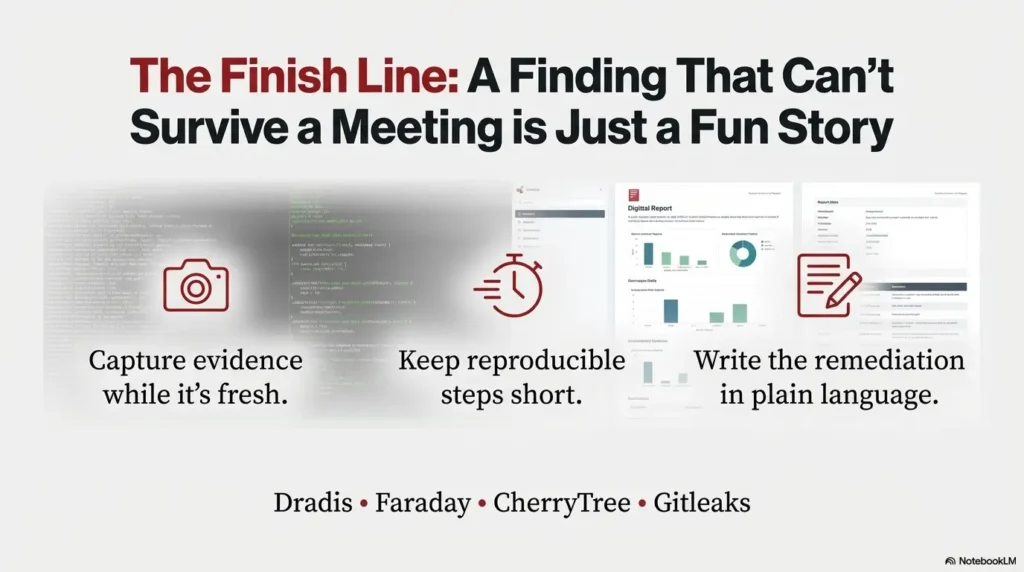
Reporting and workflow so findings survive meetings
The best pentesters I know don’t just find issues—they finish. That means evidence, reproducible steps, and a report that doesn’t make a security lead do interpretive dance. Your reporting stack is part of your tool stack. If you ignore it, you’ll pay later in rewrites.
| Tool | Best use | Why it matters |
|---|---|---|
| Dradis | Centralized reporting workflows | Makes collaboration less painful |
| Faraday | Team collaboration and data aggregation | Keeps findings from getting lost |
| CherryTree | Structured notes with hierarchy | Fast for solo operators |
| Gitleaks | Secret scanning for repos | Easy win; clear evidence |
| Semgrep | Code scanning with rules | Bridges appsec and pentest output |
If your deliverable is OSCP-style (tight steps, clean proof, minimal drama), keeping a reference like a professional OSCP report template nearby can keep your writing “report-shaped” from day one.
Estimate how long your “first evidence” pass might take if you keep it tight. This is not a promise—just a sanity check to stop runaway scope.
Result: —
Save this estimate and confirm timing with your engagement window and rate limits.
- Capture evidence while it’s fresh
- Keep reproducible steps short
- Write remediation in plain language
Apply in 60 seconds: Add a “Fix in one sentence” line to each finding draft.
Infographic: the no-fluff stack map
Read it left-to-right: build proof fast, then specialize only where scope demands.
FAQ
1) What’s the best pentesting tool for beginners?
Start with a proxy and a scanner: Burp Suite (or OWASP ZAP) plus Nmap. You’ll learn the “why” behind findings instead of memorizing tricks. 60-second action: Set up a notes template and capture your first request/response pair today. If you’re doing this in a lab, pairing that with a beginner-friendly Kioptrix Level 1 walkthrough can keep practice structured.
2) Do I need paid tools to do real pentests?
Not always. Many strong workflows are built on free tools, especially for recon, enumeration, and web validation. Paid tools often help with standardized reporting and coverage views. 60-second action: Write down your deliverable requirements—if it’s “report-ready output,” consider a structured scanner or reporting platform. It also helps to understand penetration testing vs vulnerability scanning so you don’t buy tooling for the wrong job.
3) How do I avoid getting overwhelmed by 50 tools?
Treat this list as a menu, not a mandate. Install Tier 1 first, then add one category at a time when scope demands it. 60-second action: Pick one category you actually need this week and ignore the rest. If your goal is OSCP, a 2-hour-a-day OSCP routine can be a surprisingly good “anti-tool-hoarding” constraint.
4) Which tools should I use for Active Directory assessments?
BloodHound for relationship mapping, Impacket for protocol-level testing, and a careful validation workflow tool like CrackMapExec are common. Keep everything authorized and documented. 60-second action: Create an “Identity Map” note with sections for users, groups, privileges, and reachable hosts. When the path starts forming, it helps to recognize privilege escalation patterns so your next step is reasoned, not random.
5) How do I keep my work ethical and legal?
Written authorization, defined scope, and careful evidence handling. Avoid “extra curiosity” tests outside scope, especially in wireless and credential work. 60-second action: Copy-paste your scope statement into the top of your notes and keep it visible while you test.
6) What’s the fastest way to improve my reporting?
Write findings as you go. Capture evidence with timestamps, include impact in plain language, and keep reproduction steps short. 60-second action: Add a one-line remediation suggestion to your next finding draft. If you’re practicing in labs, keep your notes aligned with a real deliverable like a Kioptrix pentest report format so “practice” turns into professional muscle memory.
Last reviewed: 2025-12. Key references I cross-check when writing reports: NIST vulnerability identifiers, MITRE ATT&CK technique mapping, and OWASP web testing guidance.
Conclusion: your 15-minute next step
Remember the hook—the “perfect stack” that found nothing? The fix wasn’t a new tool. It was a smaller stack with cleaner evidence. If you have 15 minutes, do this: install or open your Tier 1 tools, create a single notes template, and run one light, authorized discovery pass on a lab target. Then write one finding-style paragraph—even if the finding is “no issue observed.” That habit turns tools into outcomes. And outcomes are what get you rehired.
If you’re doing that “15-minute next step” inside a VM lab, make sure your environment is stable first—something as boring as VirtualBox NAT vs Host-Only vs Bridged can quietly prevent an hour of “why can’t I reach the target?” later.

