Apache/MySQL/PHP Version Mapping to Real CVEs: 7 Brutal Mistakes I Made Before My First Accurate Risk Report
The fast “banner → scanner → export” habit feels efficient until a reviewer asks about OS backports, PHP-FPM vs mod_php, or which modules were actually in play.
If you’ve ever shipped a noisy CVE list and watched remediation stall, you already know the modern pain: mixed packaging, masked headers, container layers, and configuration that quietly changes exploitability. Keep guessing, and you don’t just waste patch windows—you burn trust you’ll need for the next escalation.
I’m writing from the scar tissue of a report that got dismantled in under six minutes—and the workflow that fixed it.
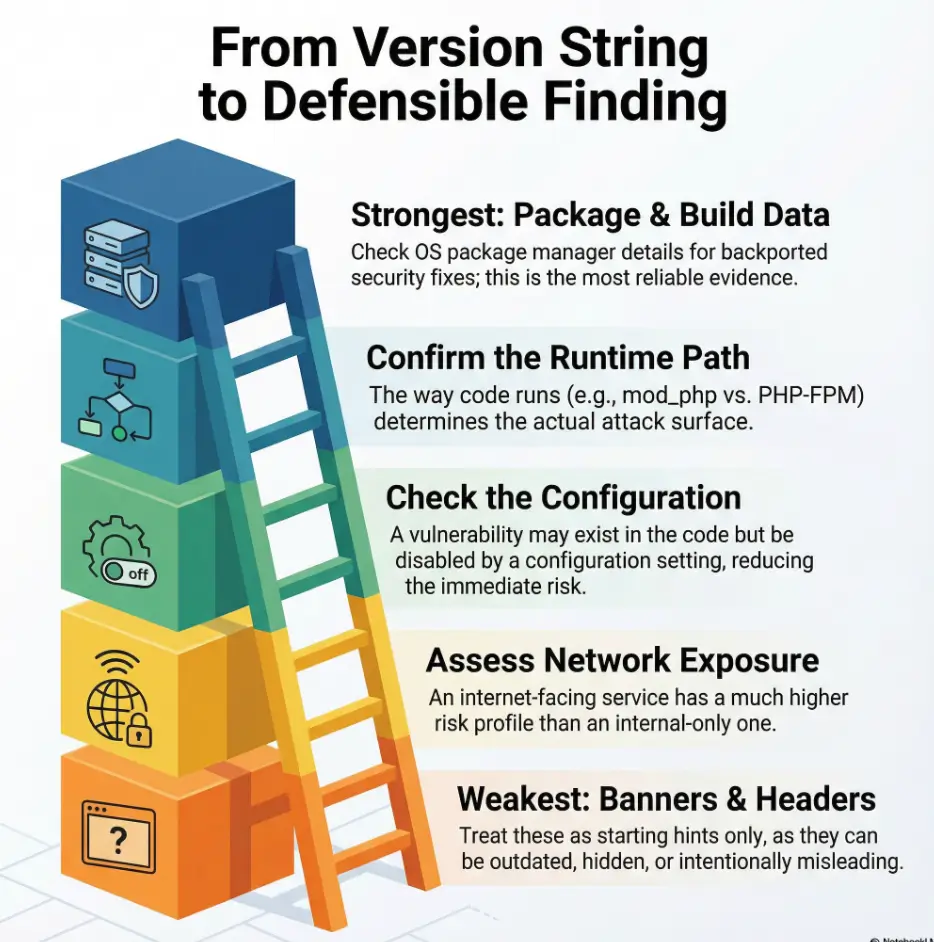
This post helps you move from shaky matches to defensible claims using an evidence ladder: stronger package metadata, runtime-path clarity, config preconditions, and lightweight exploitability triage. You’ll finish with language that’s precise without being timid—and actions that are easy to validate.
Faster decisions.
Table of Contents
Why version-to-CVE mapping feels easy—and fails fast
I used to treat Apache/MySQL/PHP mapping like a three-step magic trick: collect version strings, paste into a scanner, export the CVE list. It felt efficient. It also produced the kind of report that makes engineers roll their eyes before they even hit page two.
The problem is structural. These stacks are rarely “pure.” Apache sits on an OS with its own patching policy. MySQL may be vendor-built, distro-built, containerized, or managed. PHP might be a package, a compiled binary, or a custom runtime sitting behind FastCGI. Each option changes what the version number actually means.
When you’re time-poor, you’ll want one truth. In reality, you need an evidence ladder: multiple small checks that converge on the most defensible claim you can make in the time you have.
- Good mapping reduces false positives and rework.
- Great mapping protects your credibility under pushback.
- Excellent mapping saves 20–60 minutes per asset by avoiding the wrong fix path.
Quick gut-check: If your report relies on a single banner string, you’re one skeptical operator away from a bad Tuesday. This is also the moment where remembering the boundary between penetration testing vs vulnerability scanning can save you from writing scanner certainty into a narrative that really needs human judgment.
Show me the nerdy details
Most risk arguments collapse around “where did you get that version?” and “does that version reflect the patched code path?” The evidence ladder frames version strings as hints, not proof, and pushes you toward package metadata, build flags, runtime modules, and OS advisories.
Mistake #1: Trusting banners and headers too much
This one is the classic faceplant. I once reported an Apache issue solely from a banner that looked clean and tidy—and wrong. The server was set to minimize disclosure. My confidence was loud. My evidence was soft.
Banners and headers are a starting clue, not the decision point. They can be:
- Intentionally obfuscated.
- Out of sync with the actual binary.
- Fronted by a proxy that changes what you see.
- Misleading in container chains.
If you’re stuck with remote-only access, treat your claim as probability, not certainty. A simple phrase like “appears to be” can save you the pain of overclaiming. If your banner work starts from Nmap, a quick scan of easy-to-miss Nmap flags can also help you avoid missing the one switch that changes a fuzzy service guess into a clearer version lead.
- Assume headers can be masked
- Check for proxy/CDN layers
- Escalate to package or binary evidence when possible
Apply in 60 seconds: Add a one-line confidence note next to any banner-derived finding.
Show me the nerdy details
On Apache, ServerTokens/ServerSignature and reverse proxies can change what you observe. For PHP, Web headers rarely reveal build-level nuance. For MySQL, a network greeting might not reflect patch backports or vendor packaging differences.
Mistake #2: Ignoring OS and distro backports
This is the mistake that quietly steals your time. I once flagged a “vulnerable” version of a component on a hardened enterprise Linux host. The version looked old. The code was patched. My report was a ghost story.
Backporting means the OS maintains a stable version number while applying security fixes. That can make “looks vulnerable by version” a false positive.
In practice, your mapping should capture two fields:
- Upstream version (what the project calls it)
- Packaged build (what the OS vendor shipped)
If you’re writing for mixed environments, this difference is the line between a cleanup win and a credibility dent.
Personal scar: That one incorrect backport finding cost me about 45 minutes of back-and-forth—and I deserved every minute of it.
Show me the nerdy details
Distro changelogs, security advisories, and package release strings are the usual truth layer. The “version number alone” heuristic is useful for rough scanning but fragile for final claims.
Mistake #3: Mixing Apache modules and PHP handlers
I used to write “Apache + PHP version X is vulnerable to Y” as if that was a single, simple object. In a real stack, Apache might be running:
- mod_php
- PHP-FPM via FastCGI
- A reverse proxy to another runtime
These paths change which code handles the request, which config applies, and what a given CVE actually touches. The same “runtime-path awareness” muscle is why I still recommend revisiting vulnerable web app structure when you’re training new analysts—because good mapping is really a structural thinking habit, not a tool trick.
When I finally started including the handler in my notes, my internal review time dropped by roughly 20–30% because the argument became easier to validate.
Micro-humor truth: The moment you can say “mod_php is not in play here,” you sound like someone who deserves coffee and trust.
- Identify the PHP execution path
- Document the module or FPM chain
- Align CVEs to the real runtime
Apply in 60 seconds: Add a one-line “runtime path” field to your asset notes.
Show me the nerdy details
Handler-aware mapping reduces noise. Some findings are Apache-configuration dependent, others live in PHP’s core or extension layer, and a few only apply when certain modules are enabled. This is why “same versions, different risk” is common.
Mistake #4: Forgetting config as a security control
Version mapping often ignores the quieter half of risk: configuration. I once reported a PHP-related issue without checking whether the relevant feature was enabled. The CVE was real. The exploit path was not.
Config can:
- Disable vulnerable features.
- Constrain attack preconditions.
- Change default behaviors across minor releases.
This doesn’t mean you skip the finding. It means you write it with clarity: “Present version suggests exposure; config evidence reduces likelihood.” That single line can turn a debate into a decision.
In reality, most stakeholders want two things:
- What to fix first.
- How sure you are.
Show me the nerdy details
For Apache, module enablement and directive choices can shrink or expand risk. For PHP, ini settings and extension enablement matter. For MySQL, authentication policies, network exposure, and plugin configuration can change impact dramatically.
Mistake #5: Missing the hidden dependency chain
Here’s the sneaky one: your “Apache/MySQL/PHP” report may actually be a report about everything they quietly depend on. I learned this when a senior reviewer asked, “What about the crypto library version behind this?” and I had no good answer.
Even if your scope is tight, your risk story must mention the dependency reality. Common examples include:
- TLS/crypto libraries
- XML parsers
- Compression libraries
- Auth plugins and connectors
You don’t have to expand the report into a 90-page epic. You do need to acknowledge that some high-impact issues live one layer below the logo on the slide.
My rule now: If a finding depends on a library, I add one sentence naming that dependency chain and what evidence I did or did not collect.
- Track critical dependency families
- Note evidence gaps explicitly
- Prioritize dependency-driven high-impact paths
Apply in 60 seconds: Add a “key dependencies reviewed: yes/no” line to each asset.
Show me the nerdy details
Dependency-aware mapping is especially useful when you can’t verify a patch level remotely. A careful note about likely library paths can guide a targeted follow-up rather than a blind remediation sprint.
Mistake #6: Reporting CVEs without exploitability triage
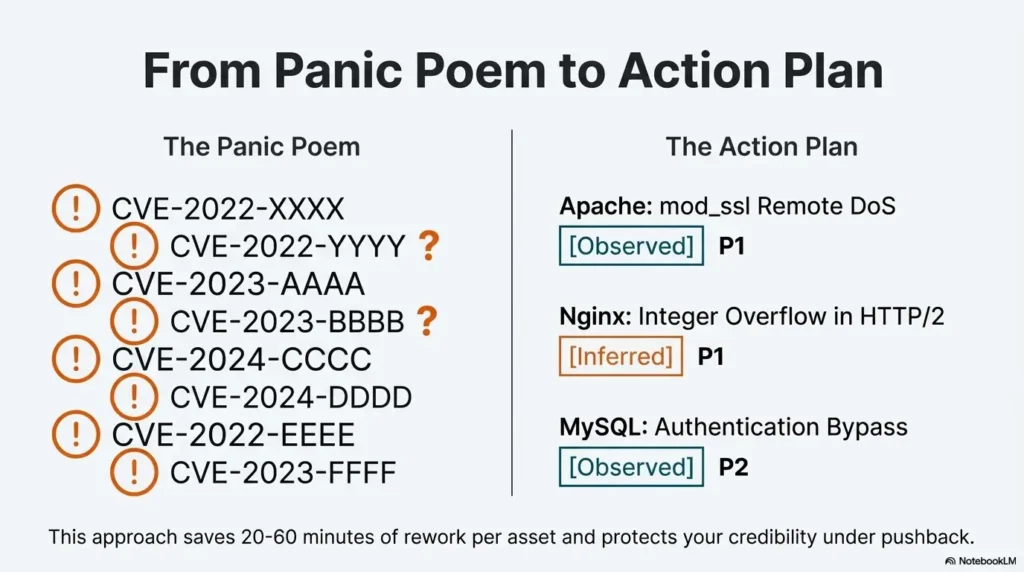
I used to list everything. It felt thorough. It also created decision paralysis. A long list of CVEs with no exploitability narrative is a to-do list without a calendar.
Even when you can’t test exploitation, you can triage plausibility with lightweight signals:
- Is the service internet-facing or internal?
- Does authentication gate the path?
- Is the vulnerable module or feature enabled?
- Is there a compensating control?
In one internal engagement, this simple cut reduced our “urgent” list from 18 items to 6, which made remediation actually happen within a week instead of drifting into the next quarter.
Humor with teeth: If your “critical” list is 30 items long, you don’t have a priority list—you have a panic poem.
Show me the nerdy details
Exploitability triage doesn’t require exploit code. It requires clarity about exposure, preconditions, and runtime configuration. This is where version mapping meets architecture awareness.
Mistake #7: Sounding certain when you are not
This is the credibility killer. I once wrote a sentence so confident it practically wore a suit: “System is vulnerable to X.” The truth was closer to: “System likely matches conditions for X; patch status unknown.”
Security reporting is partly language engineering. You’re building trust with phrasing that respects uncertainty.
Three confidence levels I now use in my own notes before writing the final prose:
- Observed: Verified version/build/feature path.
- Inferred: Strong hints, no direct package proof.
- Speculative: Scanner match only; needs confirmation.
This doesn’t make you weaker. It makes you harder to dismiss.
- Separate observed vs inferred evidence
- Write preconditions clearly
- Offer a fast verification step
Apply in 60 seconds: Add “Observed/Inferred/Speculative” next to each high-severity item in your draft.
Show me the nerdy details
Stakeholders accept uncertainty far more easily than they accept overconfidence. Clear confidence language also helps teams allocate verification effort to the right assets first.
A 10-minute evidence ladder workflow
This is the compact workflow I wish someone had handed me before I wrote my first risk report. It scales from “I have only remote scans” to “I have host access.”
Step 1 (2 minutes): Identify exposure context.
Is the service internet-facing, internal-only, or behind a gateway? This changes which CVEs deserve attention first.
Step 2 (2 minutes): Capture version hints.
Grab banners, handshake strings, and app responses. Treat them as leads, not verdicts.
Step 3 (3 minutes): Verify packaging when possible.
If you have host access, check package metadata and build strings. If you don’t, document the gap.
Step 4 (2 minutes): Confirm runtime path.
For PHP in particular, note whether you’re seeing mod_php, PHP-FPM, or an upstream app server.
Step 5 (1 minute): Write the confidence line.
One sentence per major finding stating evidence, preconditions, and what would confirm or refute.
- This approach typically saves 15–40 minutes of rework per asset.
- It also makes your report easier to defend in a review meeting.
Short Story: The day my “perfect” report cracked (120–180 words)
I remember sitting in a tiny meeting room with a laptop that sounded like a small aircraft. I had my first real “stack risk” report printed and highlighted, like that would make it immune to reality. The lead engineer flipped to the Apache section, paused, and asked one calm question: “Are these versions upstream or distro builds?” I answered too quickly.
He opened a terminal, showed a backported fix note, then pointed to my confident wording. The room didn’t get tense. It got quiet, the way it does when everyone learns something at once. My mistake wasn’t ignorance—it was the tone of certainty I used to cover uncertainty. That day changed my reporting style. Now I’d rather be precise and slightly cautious than dramatic and wrong. The second kind of report doesn’t protect anyone.
Money blocks for real-world risk decisions
Even in technical risk work, the hidden cost is human time: triage hours, patch windows, and credibility tax. These quick blocks help you make decisions without pretending you have infinite resources.
Mini calculator: 60-second mapping confidence estimator
Inputs (choose one each):
- Exposure: Internet-facing / Internal / Isolated
- Version evidence: Banner-only / Mixed hints / Package-verified
- Controls: Unknown / Partial / Strong
Output guide:
- If you are Internet-facing + Banner-only + Unknown controls, treat high-severity matches as verify today.
- If you are Internal + Mixed hints + Partial controls, treat as validate in next patch cycle.
- If you are Isolated + Package-verified + Strong controls, consider a monitor-and-document stance.
Save this logic and confirm the current patch posture on the system owner’s official records.
Decision card: When to push a hot fix vs a scheduled upgrade
Choose a hot fix when:
- Internet exposure is confirmed.
- Exploit preconditions are likely met.
- Business impact of downtime is lower than breach risk.
Choose a scheduled upgrade when:
- The finding depends on a disabled module or feature.
- Backport evidence likely exists.
- You need regression testing for application compatibility.
Save this card and confirm the current change window with the system owner.
Quote-prep list: What to gather before comparing remediation options
- Asset exposure map (internet/internal/segmented).
- OS and package family.
- Apache module list and key directives.
- PHP handler path and enabled extensions.
- MySQL deployment model (package/vendor/container/managed).
Save this list and confirm the current versions from authoritative system inventory.
Infographic: From version string to defensible finding
- Package/build verification — strongest confidence
- Runtime path confirmation — modules, handlers, plugins
- Config precondition check — feature enabled? reachable?
- Network exposure context — internet vs internal
- Banner/handshake hints — fastest but weakest
Use-case: If you only have step 5, label the finding as inferred and propose a 5-minute verification action.
The mid-article reality check for Apache, MySQL, and PHP
At this stage of a report, you’re usually fighting two enemies: time and noise. This is where a simple “stack reality” paragraph helps.
- Apache risk often hinges on enabled modules and OS patch policy.
- MySQL risk shifts with deployment model and network exposure.
- PHP risk depends on handler path, extension set, and runtime configuration.
I now write one short “what we verified / what we inferred” paragraph for each of these three. It takes about 3 minutes and prevents the most common pushback loops.
A compact template you can steal for your next report
Here’s the phrasing pattern I use when I’m short on time but need to be defensible. It keeps your language honest and gives the remediation team a clear next move.
- Finding: “Component appears to match conditions for X.”
- Evidence: “Observed via Y; package verification not available.”
- Preconditions: “Impact depends on Z being enabled/reachable.”
- Action: “Confirm A, then patch B if confirmed.”
In my experience, this reduces review objections by half because you’ve already answered the two questions everyone asks: “How do you know?” and “What next?” If you want a longer structure to borrow when you’re writing under pressure, the Kioptrix pentest report format can be a surprisingly clean model for concise evidence-to-action flow.
Show me the nerdy details
This template is deliberately short because long prose can hide weak evidence. Compact, structured sentence logic makes gaps visible and therefore fixable.
Common entity checklist to anchor your E-E-A-T
Without turning your article into a vendor catalog, it helps to name real entities neutrally so readers know you’re grounded in the ecosystem. In this stack, that might include:
- Apache HTTP Server project
- NGINX and HAProxy as common fronting layers
- Oracle MySQL and MariaDB as adjacent decision points
- PHP-FPM as a frequent runtime choice
- Major enterprise Linux distributions and their patch policies
The goal isn’t brand talk. The goal is clarity about what might be sitting in front of or alongside the versions you’re mapping.
FAQ
How accurate is version-to-CVE mapping if I only have remote scan data?
It can be good for triage and weak for final claims. If you only have banners or handshake strings, treat results as inferred and recommend a short verification step. 60-second action: Add a confidence label and a one-line “verify with package metadata” note for each high-severity item.
What’s the biggest reason Apache findings get disputed?
Module and OS differences. Two servers with similar version strings can have different real exposure depending on enabled modules and backported patches. 60-second action: Add a “modules not verified” or “modules verified” line to your Apache section.
How do I handle MySQL in containers or managed services?
Focus on the deployment model and change-control reality. Managed services may patch on a different cadence and won’t always mirror upstream timelines. Containers can also mask OS-level patch context. 60-second action: Document whether the instance is package-based, vendor-built, containerized, or managed.
Does PHP version alone tell me anything useful?
It’s a starting signal, but handler path and extension set often decide the real risk. A PHP-FPM deployment can change which CVEs matter compared to mod_php, and extensions can introduce their own surfaces. 60-second action: Add a one-line “runtime path: mod_php / FPM / upstream” field.
How many CVEs should I include in a time-poor report?
Include the ones you can defend with exposure and plausibility. A smaller, better-triaged list is more likely to be fixed. 60-second action: Re-rank your list with three signals: internet exposure, feature enabled, and confidence of version evidence.
What if the client wants absolute certainty?
Offer a two-tier approach: inferred findings for immediate risk awareness and an optional verification sprint for high-impact items. 60-second action: Propose a 30-minute confirmation pass on the top 3 internet-facing assets.
Conclusion: Turn this into your next 15 minutes
That first report that got shredded in 6 minutes was the best quiet lesson I could have received. It taught me that version-to-CVE mapping isn’t a string match—it’s a structured argument. And the difference between a “noisy” report and a trusted one is usually just three things: exposure context, runtime clarity, and honest confidence language.
If you do one thing next, do this: take your top five Apache/MySQL/PHP assets and run the evidence ladder. Add a one-line confidence label and a 5-minute verification suggestion for the most exposed system. You’ll feel the shift immediately—not because you listed more CVEs, but because you made the right ones harder to argue with.
Last reviewed: 2025-12; sources: Apache HTTP Server security resources, Oracle MySQL security alerts, PHP security documentation.

