
Mastering the Kioptrix Methodology
Five minutes into a Kioptrix box, many beginners make the same mistake: they mistake activity for progress. A scan returns ports, banners, and half-familiar clues, and suddenly the session feels less like a legal lab and more like a live-fire audition.
That is where Kioptrix Level first lab anxiety really begins. Not because the box is impossibly hard, but because new pentesters are forced to make too many decisions before they have a method for sorting evidence. The result is frantic service-hopping, messy notes, weak hypotheses, and the creeping fear that everyone else somehow “gets it” faster.
Keep going like that, and you do not just waste time. You train yourself into bad habits that follow you into every future pentesting lab.
This guide gives you a steadier way in. It shows you how to turn enumeration into a decision-making process, how to read service discovery without rushing into exploitation, and how to build notes that reduce overwhelm instead of feeding it.
The trust signal here is simple: this is not written like swagger theater. It is built around real beginner failure points, evidence-first workflow, and the kind of calm structure that actually survives contact with confusion.
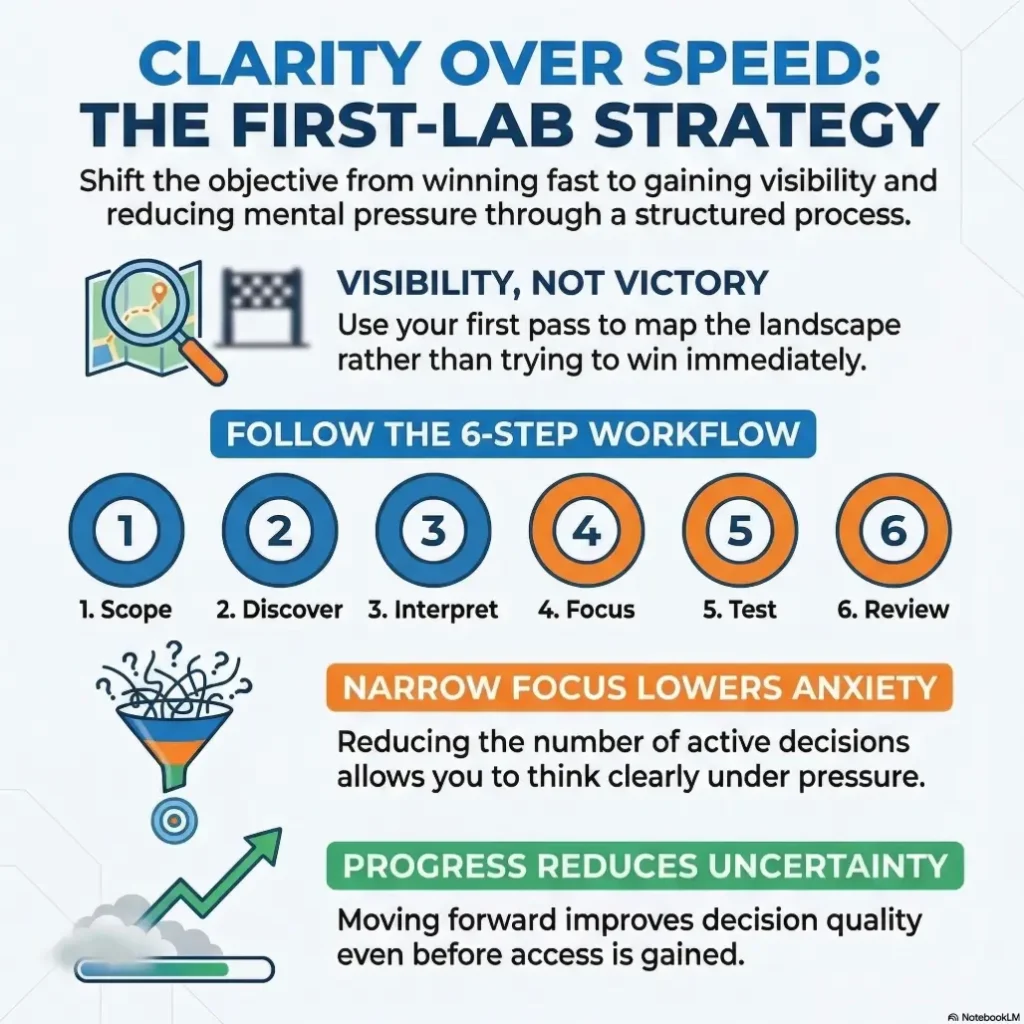
Here’s the shift:
- Less panic, more sequence
- Less guessing, more signal
- Less performance, more craft
Start there.
Table of Contents
Start Here First: Who This Is For / Not For
This guide is for the beginner who opens a legal practice lab and immediately feels their brain split into tabs. You know just enough to recognize a port scan, maybe enough to run a few commands, but not enough to feel steady. That is not failure. That is the normal sound of a new craft entering the room.
It is also for the learner who feels embarrassed by emotion. Security culture sometimes rewards the poker face. Meanwhile, your hands are hovering over the keyboard like two interns who were given different instructions. I have seen this pattern again and again: the issue is not always command syntax. The issue is sequencing under uncertainty.
This is not for anyone outside a legal, explicitly authorized lab. Kioptrix-style practice belongs inside permissioned learning environments. The point is defensive understanding, method-building, and safer professional habits. The moment that frame disappears, the whole exercise curdles.
- Use legal labs only
- Measure progress by reasoning, not speed
- Expect confusion at the start
Apply in 60 seconds: Write one line at the top of your notes: “My job is to understand the box before I try to beat it.”
First Comes Calm: Why New Pentesters Freeze on Kioptrix
The beginner’s panic is rarely about Linux. It is usually about too many decisions arriving at once. An IP resolves. A host responds. Several services appear. Suddenly every port looks urgent, every banner looks meaningful, and every tutorial you have ever half-read comes back like a flock of caffeinated pigeons.
That is why first-lab anxiety feels strangely disproportionate. The lab may be beginner-oriented, but your nervous system does not know that. It sees uncertainty plus technical language plus the quiet pressure of wanting to prove you belong. That is enough to make a simple workflow feel like a moral referendum on your intelligence.
I remember watching a new learner open three browser tabs, two terminal windows, one notes file, and a video walkthrough in under four minutes. It looked impressive until the twentieth minute, when nothing connected to anything else. They were not short on effort. They were drowning in unsequenced effort.
Kioptrix has long been framed as a place to learn basic tools and techniques, not as a stage for swagger. That is the right spirit to carry in. And tools like Nmap themselves are built around exploration and auditing, which is a useful corrective when your brain wants to skip straight to fireworks. In practice, the first win is often not technical at all. It is psychological: you stop mistaking urgency for importance.
Small truth, big relief: feeling overwhelmed does not mean you are behind. It usually means you need a narrower next step.
Eligibility checklist: Are you ready to begin this lab session?
| Check | Yes / No | Next step |
|---|---|---|
| Authorized lab only | Yes / No | Do not continue without explicit permission |
| Notes file open | Yes / No | Create one before scanning |
| Goal defined | Yes / No | Write what success means for today |
| Time box set | Yes / No | Choose a calm session length and stick to it |
Neutral next action: If you miss any row, fix that first. The box can wait two minutes.
Scope Before Swagger: The Ground Rules That Settle Your Nervous System
Before the first command, define the shape of the exercise. Which host is in scope? What network are you using? What counts as success for today? “Get root” is a destination, not a workflow. For a first session, success may be simpler and smarter: identify exposed services, map likely attack surface, and produce a reasoning trail you could explain out loud without mumbling into your hoodie.
Boundaries reduce panic because they reduce ambiguity. When a lab is clearly scoped, you no longer have to guess whether you are doing too much, too little, or something deeply silly. You are inside a marked lane. That steadiness matters more than beginners think.
There is also a professional dividend here. In real security work, you do not get extra points for improvising beyond the brief. You get trust by being precise. The earlier you build that muscle, the less likely you are to turn every exercise into keyboard jazz.
Write these four headings in your notes before you do anything else:
- Known facts
- Hypotheses
- Dead ends
- Next checks
I love this framework because it separates reality from optimism. Beginner notes often look like a compost pile of commands and vague feelings. Better notes behave like a courtroom. Facts sit in one chair. Guesses sit in another. Your future self will thank you with less swearing.
OWASP’s testing guidance has long treated information gathering and mapping as foundational work rather than decorative preliminaries. That idea is worth borrowing here. A calmer lab starts when you stop asking, “How do I win?” and start asking, “What do I know well enough to justify the next move?”
Scan Less Wildly: Your First 20 Minutes Need a Shape
The first 20 minutes should feel like setting a table, not raiding a pantry. Start with host visibility and service discovery. Keep the opening pass boring on purpose. Boring is underrated. Boring collects the facts that dramatic people later pretend they had all along.
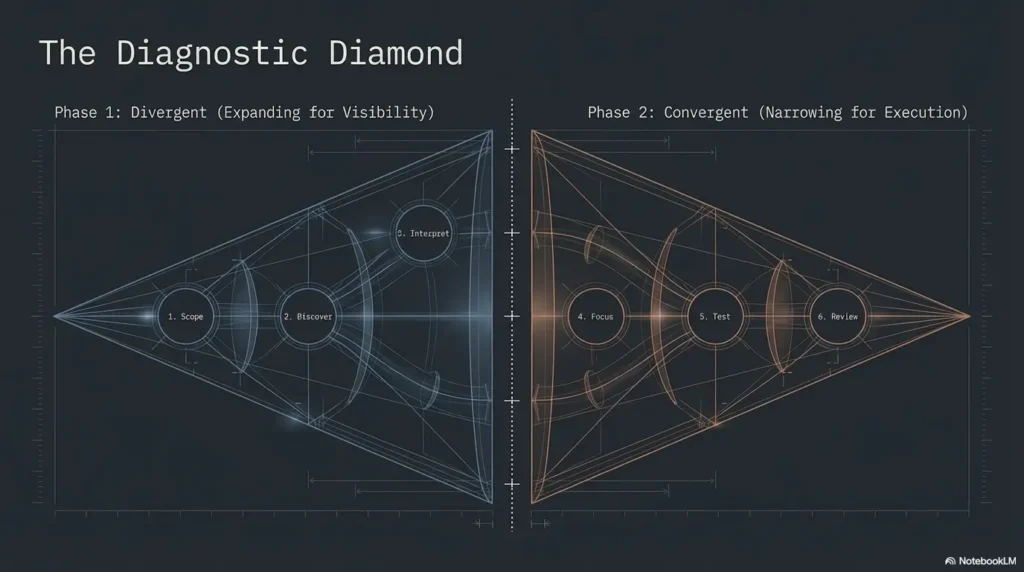
A clean beginner sequence is simple:
- Confirm the host is where you think it is
- Identify reachable services
- Record versions, banners, and anomalies
- Only then decide which service deserves deeper attention
Nmap’s own documentation emphasizes exploration, service auditing, and version identification. That is useful because it reframes the scan from “finding the magic exploit” to “building a reliable map.” And once you have a map, the anxiety drops. Not disappears, perhaps. But it loses its operatic solo.
Years ago, I watched someone rerun broad scans four times because the first output felt emotionally unsatisfying. The data barely changed. Their stress did. They were searching for certainty in repetition, which is a very human habit and a terrible method.
- Start simple
- Record what is exposed
- Delay interpretation until the data settles
Apply in 60 seconds: In your notes, create a mini table with three columns: service, observed detail, why it matters.
If you want that opening phase to feel less improvisational, a repeatable Kioptrix recon routine helps keep the first moves boring in the best possible way. And if your initial visibility work feels shaky, reviewing how to use Nmap in Kali Linux for Kioptrix can steady the basics before the box starts throwing shadows around the room.
Clues Before Payloads: How to Read the Box Without Rushing It
Open ports are not instructions. They are invitations. This sounds obvious until adrenaline shows up wearing running shoes. Then every service starts looking like a neon sign saying, “Touch me now.” Resist that impulse.
Each common service presents a different kind of question. HTTP may offer content, headers, application clues, or fingerprintable behavior. SMB may reveal naming hints, protocol behavior, or opportunities for structured enumeration. FTP, SSH, and other services each ask for a distinct investigative posture. The point is not to do everything. The point is to read the room before you start rearranging the furniture.
A useful beginner question is this: What does this evidence support, and what does it only suggest? Support is stronger than suggestion. A banner may support the presence of a service family. It may only suggest a version. That distinction matters because early certainty is often counterfeit. This is exactly where people benefit from slowing down around common banner grabbing mistakes instead of treating every returned string like gospel.
OWASP’s information-gathering sections keep returning to the same quiet principle: fingerprint first, map first, identify entry points first. That sequence is not bureaucratic fluff. It is emotional oxygen. It gives the mind a ladder when the box feels foggy.
There is a funny moment many beginners experience. You stare at a service long enough that it starts to feel personally insulting. It is not. The box is not judging you. The box is just sitting there, radiating clues with the charisma of a damp brick. Your job is to notice patterns anyway. When HTTP is the richest clue source, a more deliberate Kioptrix HTTP enumeration pass often tells you more than another round of generic poking.
Show me the nerdy details
Deeper technical notes, benchmarks, or methodology. For beginner labs, the most important distinction is between discovery output and validated interpretation. A service fingerprint can narrow possibilities, but confidence rises when multiple observations agree: port behavior, banner text, protocol response, page content, and version hints. Think in layers. One data point is a rumor. Three aligned data points begin to sound like evidence.
Don’t Exploit the Vibe: Why Early Guessing Wastes More Time Than It Saves
There is a special kind of beginner temptation that deserves a name. Let us call it exploit astrology. You see a service, feel a vibe, search a module, and decide the stars may align. Sometimes they do. More often, you burn 25 noisy minutes and come away with less understanding than when you began.
This is why “it might work” is such an expensive sentence in a first lab. It is not always wrong. It is just too weak to govern your time. Good exploitation follows narrowed possibilities. It is the child of enumeration, not its replacement.
Rapid7’s own Metasploit material describes the platform as part of a workflow for finding, exploiting, and validating vulnerabilities. That order matters. Finding and validation are not decorative parentheses around the fun part. They are the rails that keep the train from entering a lake.
I still remember the first time I watched a learner paste a module recommendation from a forum into their workflow before confirming version fit. They looked thrilled for exactly seven minutes. Then the result failed, the confidence collapsed, and suddenly they distrusted the entire lab. This is how guessing steals more than time. It steals narrative stability. If you do decide to bring Metasploit into the room, it helps to treat it as part of a Metasploit workflow for Kioptrix, not as a slot machine with a terminal prompt.
Decision card: When to keep enumerating vs when to test a path
| Situation | Better move | Trade-off |
|---|---|---|
| You have one weak clue | Enumerate more | Slower now, cleaner later |
| You have multiple aligned indicators | Test a narrow path | Some risk, higher learning value |
| You are acting because you feel stuck | Pause and review notes | Costs 2 minutes, often saves 20 |
Neutral next action: Before any exploit attempt, write the evidence that justifies it in one sentence.
Note-Taking Is Not Optional: Your Memory Will Betray You Faster Than the Box Will
Beginners tend to overestimate memory and underestimate drift. Ten minutes after a scan, you think you will remember what looked promising. Twenty minutes later, every service feels vaguely familiar and none of your reasoning is recoverable. This is how panic sneaks back in wearing a different hat.
Keep one running log. Not five scraps. Not screenshots scattered across your desktop like technical confetti. One log.
A strong first-lab note file usually contains:
- Timestamp or phase marker
- What command or check you performed
- What you observed
- What you think it may mean
- What you plan to check next
The magic is not in perfect prose. It is in separation. Facts should look different from guesses. Dead ends should be recorded without shame. Next steps should be explicit enough that, if you get coffee and return 15 minutes later, the thread is still intact.
A short anecdote here because it matters: the first time I saw a beginner recover beautifully from confusion, it was not because they knew more. It was because their notes were honest. They had written, “This path is weak because I only have one clue.” That single sentence saved them from looping back into the same bad idea later. Their future self inherited clarity instead of mystery. If you want a structure that scales beyond one practice box, borrowing ideas from note-taking systems for pentesting can make your lab history far more usable than a folder full of screenshots with names like final-final-2.png.
Know the target, network, and boundaries.
Identify services and collect visible facts.
Separate supported evidence from weak guesses.
Choose one promising service path at a time.
Only test paths that your notes can justify.
Record dead ends, update hypotheses, continue calmly.
One Service at a Time: The Anti-Spiral Plan for Overwhelm
When anxiety rises, beginners often service-hop. A little web checking, then a little SMB curiosity, then back to HTTP, then a glance at SSH, then a random search result that smells exciting. This feels active. It is usually dilution disguised as industry.
The anti-spiral rule is simple: pick the highest-signal service first and stay with it long enough to rule it in or out. “Long enough” does not mean forever. It means long enough to produce an honest interim judgment. Are the clues strengthening? Are they fading? Are you learning something specific, or just circling the same vague suspicion? For many learners, that decision becomes clearer after reading about which first service to investigate on Kioptrix instead of chasing whichever port looks the loudest.
I like a 15-to-20-minute service focus window for beginners. Not because the number is magical, but because it prevents both panic-pivoting and tunnel vision. At the end of the window, review your notes. If the path is cold, mark it cold. That is progress. Elimination is not glamorous, but neither is losing an hour to a dead corridor that kept whispering maybe.
The lab becomes emotionally smaller when you stop trying to solve all of it at once. The whole box may be a maze, but your next choice does not have to be.
- Choose one service path
- Give it a real window of attention
- Record why you pivot
Apply in 60 seconds: Pick the one service with the clearest observable details and label it “Primary Path” in your notes.
Common Mistakes That Make First-Lab Anxiety Worse
Some mistakes waste time. Others poison confidence. The second category matters more.
Running large toolsets too early. This often produces more output than understanding. It can make you feel productive while quietly dissolving your grip on the narrative.
Confusing output with findings. A scan result is not yet a conclusion. It is raw material. The difference sounds pedantic until you bet your next 30 minutes on a misread banner.
Skipping version fit. Beginners sometimes treat exploitability like a genre rather than a specific condition. “Looks old” is not a finding. “Matches multiple observed details” is closer.
Treating dead ends like personal failure. This one hurts most because it changes your posture. Once every cold path feels like proof you are not cut out for this, you stop investigating and start performing for an imaginary jury.
Reading walkthroughs too early. Help is not evil. Premature certainty is. If you open a full solution before your own mental map exists, you borrow the answer without building the pathway that made the answer meaningful.
I once saw a beginner abandon good notes because another learner in a chat room seemed “way ahead.” That comparison robbed them twice. First it spiked their anxiety. Then it made them ignore the evidence they already had. Security learning has enough friction without importing a spectator sport into it. If that pattern sounds familiar, a review of Kioptrix recon mistakes or broader Kioptrix enumeration mistakes can feel like turning on the house lights in a room that was starting to look haunted.
Quote-prep list: What to gather before you compare possible next paths
- Observed service names and likely versions
- Any accessible content, headers, or protocol responses
- Why one service appears higher-signal than another
- Which prior checks already ruled out weaker paths
Neutral next action: Do a 90-second review of these four items before switching services.
Don’t Do This When You Feel Stuck
Do not restart from zero every time confusion appears. Beginners do this because a clean slate feels emotionally pure. Unfortunately, it also erases your breadcrumbs. Review what you know before you relaunch anything.
Do not change five variables at once. If you shift tool, target assumption, service focus, note structure, and interpretation method together, you create a fog machine and then blame the room.
Do not assume silence means the path is wrong. Some checks are informative because they reveal little. Quiet results still narrow the field. A locked door is still a clue. It tells you something about where you are not going.
And please, on your first box, do not measure skill by speed. That metric is emotionally sticky and intellectually weak. Speed matters later, when judgment is already stable. Early on, speed mostly measures how fast you can become confused with confidence.
Short Story: The session that looked doomed at minute 35. A beginner had mapped several services, chased one weak idea too far, and felt the evening collapsing. They almost wiped the notes and restarted. Instead, they took three minutes and labeled every line in the file as fact, guess, or dead end. The room changed.
One neglected observation suddenly stood taller than the rest, not because it was dramatic, but because it was supported by two separate clues. They followed that thread calmly. The session did not become cinematic. No triumphant soundtrack appeared from the ceiling. But the learner finished with a clear reasoning trail and, more importantly, a new identity: not “the person who panics,” but “the person who can recover.” That shift is quieter than shell access, but it lasts longer.
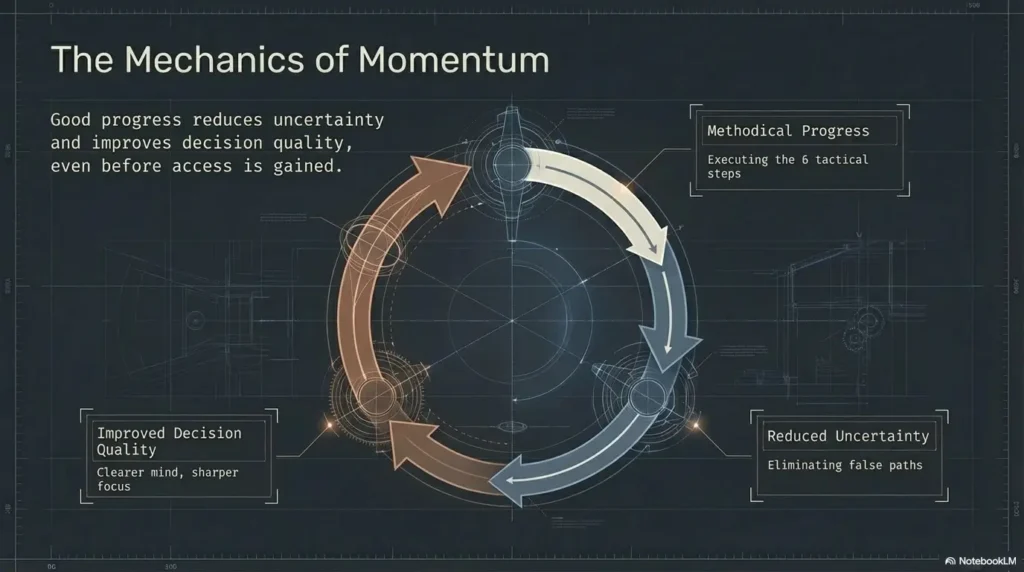
Momentum, Not Drama: What “Good Progress” Actually Looks Like
Beginners often define progress too narrowly. If they do not gain access, they conclude the session was thin. That is a brutal and inaccurate standard. In a first lab, good progress may mean a sharper service map, a better hypothesis, a cleaner elimination, or a calmer review loop.
Progress can look like this:
- You reduced the number of plausible service paths from four to one
- You identified which clues are strong and which are decorative
- You documented why a tempting path was weak
- You learned how to restart thinking without restarting the entire session
That may sound humble. It is. But humility is not the same as smallness. These are the skills that later make exploitation meaningful rather than theatrical. The people who look smooth on later boxes are usually standing on hundreds of moments where they learned to tolerate ambiguity without combusting.
There is also an emotional secret here. The first victory in many labs is not technical success. It is emotional regulation disguised as methodology. Once you realize that, your standard of success becomes more durable and, paradoxically, more professional.
- Cleaner map
- Better hypothesis
- Fewer bad options
Apply in 60 seconds: End your session by writing three wins that are not shell access.
Walkthroughs Without Dependence: How to Use Help Without Breaking Your Learning
Walkthroughs are not cheating by default. They are tools. The risk lies in timing and dosage. Open them too early, and they replace thought. Use them too late, and you may waste energy proving a point to nobody but your own pride.
A good rule for a first lab is this: take one honest independent pass first. Not a ceremonial five minutes. A real pass. Map the services, make a primary hypothesis, test your most defensible path, and record why you are stuck. Only then reach for help.
And when you do, prefer nudges over spoilers. Read enough to unblock the next step, not enough to outsource the entire narrative. If an external reference helps you understand a service, a protocol behavior, or a versioning clue, that is learning. If it hands you certainty before your own notes can hold it, that is dependency wearing a lab coat. For some people, the healthiest middle ground is starting with a broader Kioptrix level walkthrough only after they have documented their own map, rather than inhaling a full answer at minute six.
OWASP’s testing materials and official tool documentation are especially valuable here because they teach structure, not merely outcomes. Structure ages well. Spoilers age like sliced avocado.
One of the healthiest habits I have seen in beginners is writing a sentence before opening help: “What exactly do I need clarified?” That one line prevents doom-scrolling through solutions and turns assistance into a scalpel instead of a shovel. And if you want to keep the exercise grounded in reasoning rather than autopilot, trying Kioptrix Level 1 without Metasploit is often a surprisingly good discipline-builder.
FAQ
Is Kioptrix too hard for a first pentesting lab?
Not necessarily. It can be a solid first lab precisely because it teaches workflow, patience, and interpretation. The difficulty often comes less from the box itself and more from beginner sequencing. With a note-driven plan, it becomes much more manageable.
How long should a beginner spend before asking for a hint?
Long enough to produce a real evidence trail. In practice, that means you should already have mapped exposed services, picked a primary path, and written why you are blocked. Once your notes can state the problem clearly, a hint becomes useful instead of addictive.
Should I exploit the first thing that looks vulnerable?
No. Early exploitation based on weak clues often wastes time and confidence. A better approach is to collect multiple supporting signals first, then test a narrow path that your notes can justify.
What if my scan results do not match a walkthrough exactly?
That can happen. Environment differences, tooling versions, and setup variations can change how results appear. Do not panic. Focus on the underlying workflow: observe, interpret, compare clues, and keep the reasoning chain intact.
Do I need to know Metasploit before doing Kioptrix?
No. You can learn a great deal from service discovery, interpretation, and structured testing before Metasploit enters the picture. If you do use it later, treat it as part of a workflow, not as a substitute for one.
How do I know which service to investigate first?
Choose the one with the strongest observable detail set. Look for richer banners, more accessible content, or clearer fingerprinting clues. Pick the service that gives you the most evidence, not the one that merely feels exciting.
Is taking notes really that important in a beginner lab?
Yes. Notes protect you from memory drift, repeated mistakes, and false certainty. They also turn confusion into something you can inspect instead of something you merely feel.
What should I do if I feel overwhelmed halfway through?
Stop adding new inputs. Review your notes and label each line as fact, guess, dead end, or next check. Then choose one path to continue. Overwhelm often drops when the number of live decisions drops.
Next Step: Build a First-Lab Decision Sheet Before You Touch the Box
Now we can close the loop from the opening panic. The problem was never just that the box had ports, or services, or hidden pathways. The problem was that everything arrived at once and demanded significance before you had a structure to receive it. The cure is not bravado. It is a decision sheet.
Before your next session, create a plain document with four headings: known facts, hypotheses, dead ends, next checks. Beneath that, add one line that defines today’s success. Keep it modest and concrete. “Produce a defensible service map” is an excellent first target. So is “justify one primary path with evidence.” Those goals build the part of you that later handles more complex labs without turning into a weather system.
Here is the final practical frame. In your first 15 minutes, do not try to become impressive. Try to become legible to yourself. That single shift changes everything. It turns the lab from a performance into an investigation, from a dare into a craft. If you want a fuller bridge from this first-box mindset into a longer progression, the Kioptrix labs beginner roadmap is a natural next place to keep the momentum honest.
Mini calculator: How much focus time should this session really have?
Input 1: Total available minutes
Input 2: Number of service paths you expect to inspect
Output idea: Give the first path at least one-third of your session. Example: 60 minutes total and 3 possible paths means the first path deserves about 20 focused minutes before you pivot.
Neutral next action: Write your session length and first-path time box before you begin.
That is the concrete next action within 15 minutes: build the note template first, define success second, and only then begin enumeration. Calm is not separate from method here. Calm is method.
Last reviewed: 2026-03.

