
The Architecture of Risk: Mastering Pentest Liability
One vague sentence in a pentest contract can turn a $15,000 engagement into a six-figure argument. The pain usually starts the same way: “Just sign our standard terms,” then weeks later you discover the liability cap is easy to bypass, the carve-outs are wide open, and the report reads like a warranty.
A strong penetration testing contract limitation of liability clause isn’t legal theater—it’s risk architecture. It sets a financial ceiling on claims, excludes certain damage types, and defines narrow exceptions (carve-outs) so liability is bounded to the actual service performed—not every downstream business loss after a security incident.
Table of Contents
Fast Answer
A strong penetration testing Limitation of Liability clause usually (1) sets a clear cap (often tied to fees paid), (2) excludes hard-to-quantify damages (like lost profits), (3) keeps carve-outs tight and definable (often limited to willful misconduct and narrow “can’t limit” risks), and (4) matches scope, evidence handling, and a dispute process—so your report doesn’t become Exhibit A in a lawsuit.
1) Scope first: why LoL fails when your SOW is fuzzy
The liability clause can’t rescue a vague scope
In penetration testing contracts, liability rarely explodes because the LoL clause is “missing.” It blows up because the SOW reads like a horoscope: “test the environment,” “identify vulnerabilities,” “provide recommendations.” When scope is fuzzy, the report starts acting like a guarantee—because it’s the only concrete thing anyone can point at.
A quick war story: I once saw a one-page SOW that didn’t name environments or dates. The client had an outage two months later and argued the pentest “covered everything.” The consultant’s LoL was fine on paper… but the scope wasn’t. The argument turned into: “You said you tested it.” That’s how Exhibit A is born.
Tie LoL to the exact services (testing window, systems, methods, exclusions)
Your LoL should point back to the SOW definitions. In plain English, you want the contract to say: “Liability is limited for these services, performed during this window, against these targets, using these methods, with these exclusions.”
- Testing window: start/end timestamps (and time zone), plus maintenance window rules.
- Targets: hostname/IP ranges, apps, APIs, cloud accounts, and what is explicitly out of scope.
- Methods: external vs internal, authenticated vs unauthenticated, social engineering/no social engineering.
- Constraints: rate limits, stop rules, “no destructive testing” boundaries.
- Dependencies: client-provided credentials, test accounts, whitelisting, staging parity, and who owns failures here.
Define “deliverables” so the report doesn’t imply guarantees
Define what the deliverable is (a report of findings within a time-bounded assessment) and what it is not (a certification of security, compliance, or breach prevention). This isn’t weasel language; it’s honest. A pentest is a snapshot. If your team already uses a standardized output, base this section on your Kali pentest report template so legal language and report language don’t drift apart.
Micro-heading: Let’s be honest… your “standard” SOW is doing you no favors
If your SOW doesn’t say “staging only” but you run tools against production anyway, you’re basically signing a blank check with your own pen. Your LoL can’t fix a scope mistake you didn’t admit was possible.
- Make the testing window, targets, and exclusions explicit.
- Define “deliverable” as a time-bounded report, not a guarantee.
- Write scope assumptions (credentials, whitelisting) as shared risks.
Apply in 60 seconds: Add one sentence: “Services are limited to the Targets during the Testing Window, subject to the Constraints in the SOW.”
Eligibility checklist: can you credibly push a tighter liability cap?
- Yes/No: You can run the test in staging (or production with strict stop rules).
- Yes/No: You will not store client data beyond minimal evidence (screenshots redacted, short retention).
- Yes/No: The SOW lists targets + exclusions clearly (no “entire environment” phrasing).
- Yes/No: The client provides test accounts/credentials and confirms authorization in writing.
- Yes/No: You are not doing incident response, managed detection, or ongoing SOC services.
Next step: If you answered “No” to two or more, tighten scope first before you argue about cap size.
2) Cap mechanics: pick a number that survives negotiation (and a judge)
Cap types that actually get accepted (fees paid, 12-month fees, fixed dollar cap)
Most buyers don’t hate caps. They hate caps that feel disconnected from reality. In a penetration testing limitation of liability clause, the “usual suspects” are:
- Fees paid (under the SOW): simplest, common for one-off tests.
- Fees paid in the prior 12 months: common in MSAs with multiple SOWs.
- Fixed dollar cap: easier for procurement to budget (e.g., $100k), but can be scary for small firms.
A small anecdote: I’ve seen “fees paid” accepted instantly when the SOW was clean and the consultant offered a crisp retest window. Same client fought for weeks when the SOW was vague and the report promised “secure.” The cap didn’t change. The context did. If you need a paired draft, keep your legal section and pen test SOW template versioned together.
“Per claim” vs “aggregate” caps (the quiet difference that changes everything)
This is where people accidentally volunteer to be sued twice. A per-claim cap can multiply fast if the client pleads separate causes of action. An aggregate cap keeps the cap as one ceiling for all claims tied to the contract.
Separate caps by risk bucket (testing vs incident handling vs data custody)
- Penetration testing services: cap tied to fees paid for the test.
- Incident response / emergency support: higher cap (or different terms).
- Data custody / hosting evidence: only if you truly store sensitive data.
Cap timing: when payment schedules accidentally shrink your protection
A classic trap: your cap is “fees paid,” but the client pays 10% up front and the rest net-60. If something goes wrong during testing, “fees paid” might be tiny at the exact moment you need the cap most. A practical fix: define “fees paid” as fees payable under the SOW, or “total fees under the applicable SOW,” not “paid to date.”
Mini calculator: “fees paid” vs “fees payable” cap
This is not legal advice—just a quick way to visualize exposure during negotiation.
Enter fees to calculate.
3) Hidden landmines: the phrases that quietly delete your cap
“Any and all damages” vs “to the maximum extent permitted”
Contract drafting has a recurring comedy: someone writes a firm cap, then a later sentence accidentally nukes it. One of the safest stabilizers is: “to the maximum extent permitted by applicable law.”
The one word that expands liability (“including” done wrong)
“Including” is the friend who means well and still sets your kitchen on fire. If you say “no consequential damages, including…” you want to be careful that the list is clearly within the excluded category.
When “gross negligence” becomes a cap-killer in practice
Buyers often ask for a carve-out for “gross negligence.” In pentesting, it can become a cap-killer because it invites hindsight. If you must accept it, define a clear threshold and tie it to concrete conduct.
Decision card: which cap structure fits this pentest?
Choose A: Fees payable (aggregate)
- Best for one-off tests with clean scope.
- Strongest “simple story” in negotiation.
- Works well when you minimize data custody.
Choose B: Fixed dollar cap
- Best when procurement needs a known ceiling.
- Useful if fees are small but risk is perceived high.
- Watch insurance limits and deductibles.
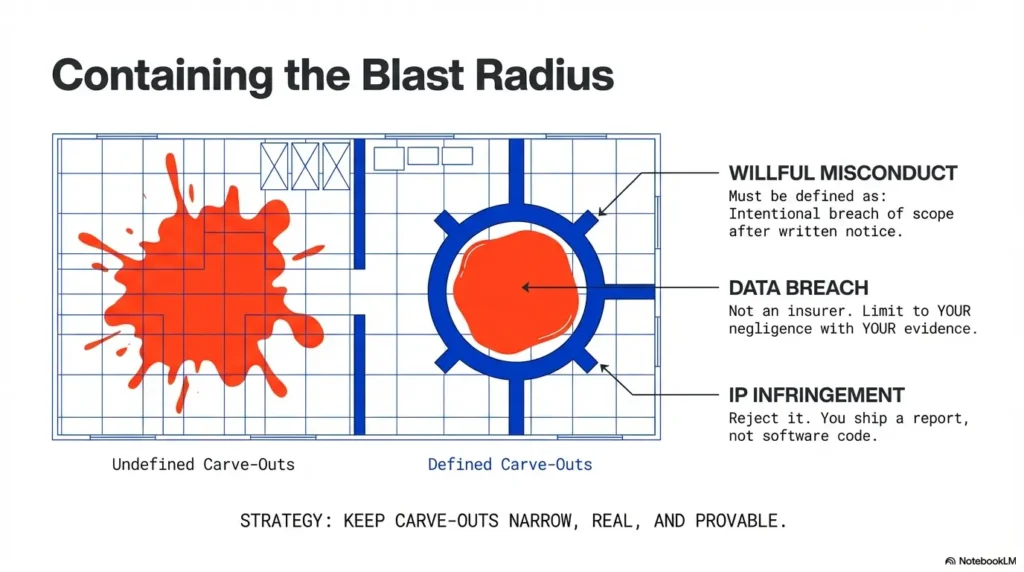
4) Carve-outs: keep them narrow, real, and provable
Carve-out categories buyers push for (and which you can often narrow)
Procurement teams tend to arrive with a “standard carve-out bundle”: willful misconduct, fraud, gross negligence, confidentiality breaches, IP infringement, data breaches, and sometimes violation of law. Your job is to keep carve-outs bounded.
The “willful misconduct” carve-out: define it or it swallows the rule
Define it in terms of intentional or knowing violation of the agreement (especially scope and stop rules), not “you should’ve known.”
IP infringement carve-outs: don’t accept them if you don’t ship code
If you’re not delivering software, a broad IP carve-out is usually mismatched. If procurement insists, narrow it to your deliverables and third-party claims directly caused by your materials.
Data breach carve-outs: align with whether you actually handle sensitive data
If you never store customer PII and you only collect minimal evidence, the carve-out should reflect that. Keep it tied to your systems and defined security failures on your side.
5) Excluded damages: make “no consequential damages” mean something
Consequential vs direct: the plain-English test that stops fights later
Direct damages look like a receipt for a specific cost caused by the breach. Consequential damages look like a chain reaction (lost profits, goodwill, business interruption, downstream churn).
“Lost profits / revenue / goodwill” lists that reduce ambiguity
Use a short list to reduce interpretive fights. Keep it readable and targeted.
Special rule for pentests: business interruption claims and “but for” theories
If testing touches production, pair stop rules with excluded damages language and explicit client responsibilities for redundancy, rollback, and backup.
6) The pentest twist: your report can become Exhibit A—design for that
Disclaimers that reduce “reliance” without sounding evasive
The report should be framed for internal risk management, tied to defined targets and testing windows, and not presented as certification of security. Keep statements bounded and factual.
Evidence handling: screenshots, logs, PII minimization, and retention windows
Evidence is where “helpful” can become “harmful.” Write explicit rules for minimization, redaction, retention, and secure transfer. If your workflow depends on proof artifacts, standardize naming and retention using a documented process such as a screenshot naming pattern for pentest evidence.💡 Read the official penetration testing contracts guidance
- Use time-bounded, target-bounded snapshot framing.
- Write “no guarantee” language in calm, professional terms.
- Minimize/redact/retain evidence with explicit windows.
7) Insurance alignment: make the clause match your actual coverage
Professional liability / E&O vs cyber
Many pentest disputes are framed as professional-services disputes (missed finding, flawed methodology, negligent advice). E&O often maps there; cyber may map to incidents in your own systems.
Contractual liability pitfalls
- Broad indemnities: can exceed policy response.
- Uncapped carve-outs: may dwarf practical coverage.
Subcontractors: flow-down LoL
If you use specialists, flow down confidentiality, scope rules, evidence handling, and cap logic so you are not the only deep pocket.
8) Dispute-proof drafting: the “fight path” you want when things go wrong
Venue, governing law, and attorneys’ fees
Choose governing law and venue intentionally. Avoid “any court anywhere” defaults when possible.
Notice-and-cure + escalation ladder
Set a pre-filing path: project lead meeting, executive meeting, mediation, then litigation/arbitration.
Limits on claims
Use a reasonable claims window so stale disputes do not dominate new work.
9) Who this is for / not for
This guide fits project-based testing with defined deliverables and optional retests: independent pentesters, boutiques, SaaS security teams, and MSPs.
It is not a direct template for 24/7 managed detection, incident response retainers, or fully managed SOC operations.
If your team is transitioning from exam-lab workflows into client delivery, align your process discipline first—for example, a repeatable VM lockdown checklist and lab logging standards reduce evidence chaos that later becomes legal chaos.
10) Common mistakes that trigger real claims (don’t do these)
Mistake #1: capping liability but promising outcomes
Don’t promise “secure/compliant/safe.” Promise services: test, document, recommend, retest.
Mistake #2: broad carve-outs that rewrite the deal
Narrow confidentiality and breach language to measurable, controllable facts.
Mistake #3: indemnity not aligned with LoL
Cap where possible, limit to third-party claims, avoid broad “all losses” obligations.
Mistake #4: scope creep in email instead of change orders
If the client asks for “one more endpoint,” issue a change order. This is where disciplined note systems help; even a simple note-taking system for pentesting can preserve who requested what and when.💡 Read the official web security testing standards guidance
11) When to seek help (legal + risk) before you sign
- Client demands uncapped liability or “all breaches” responsibility.
- You will access production, customer data, or privileged credentials.
- You test regulated or critical infrastructure environments.
- Procurement adds indemnities that conflict with your cap.
- Cross-border evidence storage and transfer issues appear.
12) FAQ: Limitation of Liability for penetration testing contracts (US)
1) What’s a reasonable liability cap?
Often 1x fees payable under the SOW; 2x–3x in higher-risk contexts. Scope clarity and insurance alignment matter more than folklore numbers.
2) “Fees paid” or 2x/3x?
“Fees payable” is generally safer than “paid to date,” especially with delayed payment schedules.
3) Should pentesters accept a “data breach” carve-out?
Only if tightly scoped to what you actually hold and control.
4) Are consequential-damage waivers enforceable?
Commonly used in commercial agreements, but enforceability is jurisdiction-specific and fact-specific.
5) Gross negligence vs willful misconduct?
Willful misconduct is typically intentional; gross negligence is often argued through hindsight and can be broader in practice.
6) Indemnity vs LoL?
Indemnity can override your cap if drafted broadly. Align them explicitly.
7) Can clients bypass the cap via misrepresentation claims?
They can try. Keep marketing/report claims bounded to testing scope and window.
8) Per-claim or aggregate?
Aggregate caps usually reduce multiplication risk.
FAQ
What is a “standard” limitation of liability clause template for penetration testing services?
Typically: an aggregate cap tied to fees payable under the SOW, consequential-damages waiver, narrow intentional-misconduct carve-out, and notice-and-cure + dispute path.
How do I keep procurement from adding carve-outs that make the cap meaningless?
Request definitions and thresholds; narrow to intentional conduct; tie to written notice and scope boundaries.
Should the pentest report include a reliance disclaimer?
Yes—professional, bounded, and truthful language tied to test window and targets.
Can I use one LoL clause for every pentest engagement?
Use a base clause, then adjust risk knobs: production, privileged access, regulated data, retention, subcontractors, and service type.
Conclusion
Let’s close the loop from the beginning: the clause that reduces lawsuit risk without killing the deal isn’t the one with the fanciest legal words. It’s the one where every piece agrees: scope tells the truth about what you tested, the cap is measurable, carve-outs are narrow and definable, consequential damages are clearly excluded, and the dispute path forces calm before chaos.
If you do one thing in the next 15 minutes, build a Liability Map: (1) services performed, (2) data/credential/production touchpoints, (3) insurance limits, and (4) preferred cap + carve-outs. Then rewrite your LoL so every term matches that map—no extras, no contradictions. If your audience also asks about certification pathways and service credibility, a contextual bridge to best certification after OSCP can naturally support trust-building without diluting this legal section.💡 Read the official cybersecurity control frameworks guidance
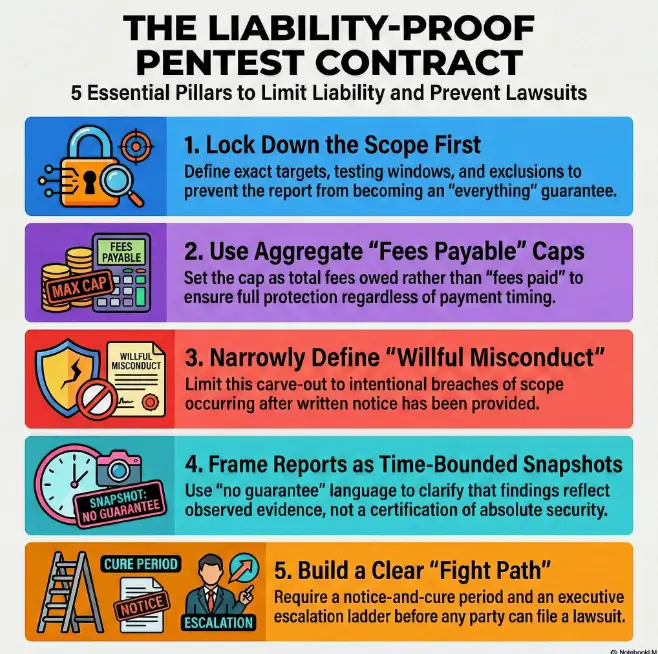
Infographic: The “Liability-Proof” Pentest Contract Flow
1) Scope Truth
Targets + window + exclusions + stop rules.
2) Cap Structure
Aggregate, fees payable, no timing shrink.
3) Carve-Out Control
Define and narrow exceptions.
4) Report + Evidence Shield
Snapshot framing + minimal evidence.
5) Dispute Path
Notice, cure, escalate, then file.
Negotiation-ready clause language (educational template)
Limitation of Liability (Educational Template)
(a) Cap. TO THE MAXIMUM EXTENT PERMITTED BY APPLICABLE LAW, IN NO EVENT WILL [SERVICE PROVIDER]’S TOTAL LIABILITY ARISING OUT OF OR RELATING TO THE SERVICES, THE DELIVERABLES, OR THIS AGREEMENT (WHETHER IN CONTRACT, TORT, OR OTHERWISE) EXCEED [THE TOTAL FEES PAYABLE UNDER THE APPLICABLE STATEMENT OF WORK] (THE “CAP”). THE CAP IS AGGREGATE AND APPLIES TO ALL CLAIMS ARISING OUT OF OR RELATING TO THE SAME OR RELATED FACTS, CIRCUMSTANCES, OR EVENTS.
(b) Excluded Damages. TO THE MAXIMUM EXTENT PERMITTED BY APPLICABLE LAW, IN NO EVENT WILL EITHER PARTY BE LIABLE FOR ANY INDIRECT, INCIDENTAL, SPECIAL, CONSEQUENTIAL, OR PUNITIVE DAMAGES, OR FOR ANY LOSS OF PROFITS, REVENUE, BUSINESS, GOODWILL, ANTICIPATED SAVINGS, OR BUSINESS INTERRUPTION.
(c) Carve-Outs (Narrow). NOTHING IN THIS SECTION LIMITS LIABILITY FOR A PARTY’S WILLFUL MISCONDUCT OR FRAUD. “WILLFUL MISCONDUCT” MEANS AN INTENTIONAL AND KNOWING MATERIAL BREACH, INCLUDING INTENTIONAL PERFORMANCE OUTSIDE AUTHORIZED SCOPE AFTER WRITTEN NOTICE.
(d) Scope + Snapshot. SERVICES ARE LIMITED TO TARGETS IN THE APPLICABLE SOW AND PERFORMED ONLY DURING THE TESTING WINDOW, SUBJECT TO CONSTRAINTS AND STOP RULES. DELIVERABLES ARE TIME-BOUNDED OBSERVATIONS, NOT GUARANTEES OF SECURITY, COMPLIANCE, OR BREACH PREVENTION.
(e) Evidence Handling. [SERVICE PROVIDER] WILL MINIMIZE AND PROTECT EVIDENCE, REDACT SENSITIVE DATA WHERE FEASIBLE, AND RETAIN EVIDENCE NO LONGER THAN [30/60/90] DAYS AFTER FINAL DELIVERY, UNLESS OTHERWISE AGREED IN WRITING.
And one final practical note: if your buyer wants stronger terms, offer a priced upgrade—higher cap, expanded insurance, or more controlled testing conditions. That is not stubbornness; that is honest risk pricing.
Last reviewed: 2026-01

