
Stop the “Slow Bleed” of Your SOC 2 Budget
Most founders don’t blow their startup security budget on one bad purchase—they bleed it out in hidden labor and midnight screenshot hunts.
The pain isn’t “we need more security.” It’s stalled deals, fuzzy ownership, and budgeting that feels like guesswork dressed up as planning. Delaying only invites the rework tax: burnt hours and audits that land before you’re ready.
Choose Your Lane
- Tier 1 $500 / month
- Tier 2 $1,000 / month
- Tier 3 $2,000 / month
This is a practical, field-tested method: a three-bucket cost model (tools, people-time, milestone fees) and a 90-day execution sprint tied to real procurement friction.
Table of Contents
Start Here: Pick Your SOC 2 Budget Lane in 5 Minutes
The 3 inputs that change everything (team size, data sensitivity, sales pressure)
If you only remember one thing: SOC 2 cost is not “tool price.” It is risk + operating rhythm + deal urgency. Three inputs decide your lane fast:
- Team size: 5 people with shared laptops is one universe; 35 people across regions is another.
- Data sensitivity: Basic app telemetry vs customer PII vs HR/payroll + production logs.
- Sales pressure: “Nice to have next year” vs “procurement blocked this quarter.”
A founder I advised once tried to “save money” by deferring onboarding/offboarding rigor for six months. He saved about $300 monthly in tooling, then lost two weeks to evidence backfill when a buyer requested access control history. Cheap quarter, expensive season.
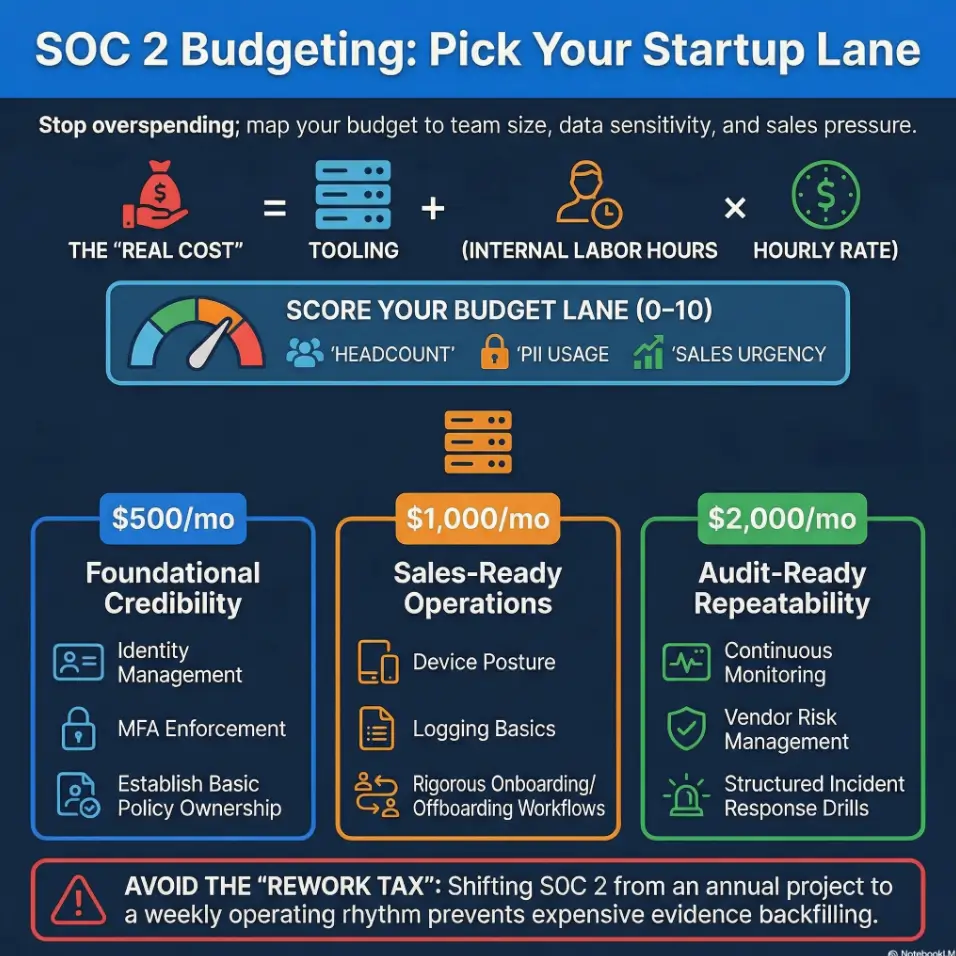
A quick scoring model for $500 vs $1,000 vs $2,000/month
Score yourself 0–2 on each line. Add the total:
- Headcount > 15 (0/1/2)
- Handles PII or employee data at scale (0/1/2)
- Enterprise RFPs this quarter (0/1/2)
- Dedicated control owners exist (0/1/2)
- Security questionnaires are stalling deals (0/1/2)
0–3: start around $500. 4–7: $1,000 lane. 8–10: $2,000 lane.
- Low score: prioritize fundamentals and consistency.
- Mid score: pay for speed in evidence collection.
- High score: fund repeatability and leadership cadence.
Apply in 60 seconds: Run the 5-line score with your ops lead and assign your lane before buying anything.
Let’s be honest… most teams underprice internal time, not software
In early-stage teams, founder/ops time is the hidden line item nobody invoices. Yet it drives outcomes more than another dashboard. If one founder spends 6 hours/week on policy edits, questionnaire responses, and “where is that screenshot?” hunts, your real monthly cost can quietly exceed $2,000 in labor even with a $400 tool bill.
My rule of thumb: if your team spends more than 20 person-hours/month gathering evidence, your next dollar should reduce evidence friction—not add a new control domain.
Calculator Logic First: What Counts as “SOC 2 Spend” (and What Doesn’t)
Fixed monthly costs vs one-time implementation costs
Use a calculator with three buckets:
- Fixed monthly: compliance platform, endpoint management, log retention, lightweight training.
- One-time setup: policy baseline, control mapping, initial hardening, evidence taxonomy.
- Periodic external: readiness review, audit and report costs, occasional specialist support.
When teams mash these together, monthly numbers look scary and random. Separating them makes planning sane. AICPA defines the SOC reporting framework; your spend is about proving controls operate over time, not producing a one-week document sprint.
Hidden line items: founder hours, evidence cleanup, policy drift
The most common “we didn’t budget for this” items:
- Founder/ops reviews: approvals, exceptions, policy communications.
- Evidence cleanup: duplicate screenshots, missing timestamps, orphaned tickets. A repeatable screenshot naming pattern prevents this from snowballing.
- Policy drift: written policy says one thing, real operations do another.
I once watched a team spend 9 hours fixing naming inconsistencies alone (“JML,” “JoinerMoverLeaver,” “On/Offboarding”). Not glamorous, but auditors and buyers read consistency as maturity.
Why audit fees can distort your monthly view
Audit and readiness costs are often periodic, but finance teams mentally divide them by 12 and panic. Better framing: treat audit as a milestone cost triggered by operating confidence. If controls are immature, paying for audit early is like ordering dessert before the stove is on.
Money Block: Fee/Rate Table (illustrative ranges, varies by scope and firm)
| Line item | Typical range | Notes |
|---|---|---|
| Compliance platform | $200–$1,200/mo | Automation depth and integrations vary widely. |
| Endpoint/security ops tooling | $100–$1,000/mo | Depends on seat count and retention needs. |
| Readiness support | $0–$8,000 one-time | Can be founder-led or advisor-assisted. |
| Audit/report | $8,000–$30,000+ periodic | Scope, trust criteria, complexity, and firm drive variance. |
Neutral action: map each line to fixed monthly, one-time, or milestone before approving budget.
Show me the nerdy details
Use a three-ledger method: (1) recurring tool contracts, (2) labor hours by owner and control family, (3) milestone external spend. Track variance monthly and tag every cost as “control creation” or “control operation.” If your “creation” share stays high after month 3, your process is unstable.
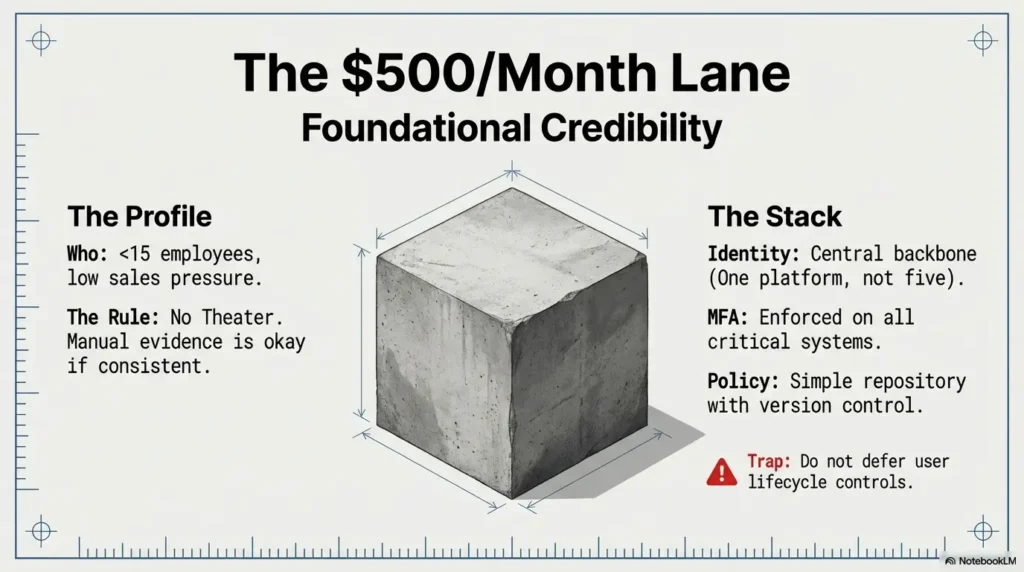
$500/Month Plan: Bare-Minimum, No-Theater Compliance
Tool stack priorities: access control, MFA enforcement, policy management
This lane works when you’re early, careful, and disciplined. You are optimizing for credible basics, not perfect automation. Priorities:
- Central identity + mandatory MFA for all critical systems.
- Basic access review rhythm (monthly or quarterly, but scheduled).
- Simple policy repository with version control and ownership.
At this tier, avoid buying five platforms. One clean identity backbone and documented procedures beat a messy stack every time. If you need to define assessment boundaries early, use a clear penetration test SOW template and align it with your control scope.
Control scope: what to defer without creating audit pain later
Safe deferrals (for many seed teams): advanced detection engineering, heavy GRC workflow customization, deep vendor scoring models. Do not defer user lifecycle controls, device hygiene, backups, incident logging, or documented change management.
One founder told me, “We’ll write incident response later.” Then a minor outage happened, and they spent half a day arguing where postmortem notes should live. The pain wasn’t technical; it was procedural emptiness.
The minimum evidence cadence that still passes smell-test review
- Monthly: access reviews, key policy acknowledgments, critical patch checks.
- Quarterly: vendor list review, risk register refresh, tabletop-lite incident drill.
- Per event: onboarding/offboarding tickets, exceptions approvals.
- Identity and MFA first.
- Document who owns each control.
- Collect evidence as operations happen.
Apply in 60 seconds: Create a one-page control owner sheet with due dates for this month.
Money Block: Eligibility Checklist (Yes/No)
- Do you have fewer than ~15 active employees? Yes/No
- Can one owner run a monthly evidence routine? Yes/No
- Are enterprise buyers not requiring immediate Type II timing? Yes/No
- Can you enforce MFA across all critical systems this month? Yes/No
If you answered “No” to 2+ items, consider moving to the $1,000 lane now. Neutral action: mark your first “No” as the next investment target.
$1,000/Month Plan: The “Close Deals Without Chaos” Setup
What to add first: device posture, logging basics, onboarding/offboarding rigor
This is the lane where many B2B SaaS teams should live. You’re not trying to look big; you’re trying to move deals without operational drama. Add, in order:
- Device posture controls: encryption, update compliance, baseline hardening.
- Logging basics: enough retention and visibility to investigate incidents.
- Joiner-Mover-Leaver rigor: deterministic onboarding/offboarding workflow with approvals.
I’ve seen a single clean offboarding process reduce buyer follow-up questions by half during security reviews. Not because it’s flashy, but because it signals operational adulthood.
Where this tier wins: faster security questionnaires and fewer fire drills
With lightweight automation, questionnaire answers become repeatable. Instead of Slack archaeology, you point to named controls, assigned owners, and recent evidence. That speed affects revenue velocity more than people admit. Teams that standardize documentation often adapt faster to buyer asks using a consistent pentest report template for technical evidence packages.
At this tier, you can often cut prep time for standard questionnaires from “half-day scramble” to roughly 60–90 minutes when your control mapping is maintained.
Open loop: the single control buyers silently use to judge maturity
Buyers rarely say this directly, but they watch access lifecycle hygiene: who got access, why, how fast revoked, and whether records are clean. If this looks sloppy, everything else feels risky, even if your policy PDF is beautiful.
Money Block: Decision Card — When $500 vs $1,000
Choose $500 when sales pressure is low and one owner can sustain evidence cadence.
Choose $1,000 when questionnaires are slowing deals and manual evidence takes over 20 hours/month.
Trade-off: $1,000 spends more cash to recover founder focus and sales velocity.
Neutral action: estimate monthly hours saved if evidence capture becomes semi-automated.
$2,000/Month Plan: Audit-Ready Operations, Not Just a Badge
Building for repeatability: monitoring, vendor risk, incident response drills
This lane fits teams where compliance friction is revenue friction. You’re investing in repeatability across people, not heroics by one operator. Priorities:
- Improved monitoring and alert triage process.
- Vendor risk workflow with inventory, tiering, and review cadence.
- Structured incident response drills and post-incident closure actions.
A Series A team I worked with moved from “quarter-end dread” to a weekly 30-minute security ops standup. Same people, different rhythm. Their month-11 evidence panic dropped dramatically because controls were operating continuously.
When fractional security leadership becomes ROI-positive
If your team regularly handles buyer escalations, legal security addenda, and cross-functional control conflicts, fractional security leadership can become cost-positive. Good leadership here means fewer dead-end purchases and cleaner decision paths between engineering, ops, legal, and sales.
At this maturity, you stop asking “Which tool is best?” and start asking “Which owner will run this every month?” That one question prevents budget leaks. For client-facing security engagements, tightening legal language early with a penetration test limitation-of-liability clause helps reduce rework in procurement and legal review.
Open loop: why mature teams still fail evidence reviews in month 11
Because the program looked operational, but evidence lineage was weak: mismatched timestamps, unowned exceptions, stale vendor records, and unclear scoping notes. Mature-looking dashboards can hide fragile process bones.
- Fund owner discipline and review cadence.
- Strengthen vendor and incident workflows.
- Prioritize evidence lineage quality.
Apply in 60 seconds: Audit one control’s evidence chain from policy to proof; fix the first broken handoff.
Show me the nerdy details
For audit-readiness, create a control-to-evidence matrix with fields for owner, frequency, source system, reviewer, exception path, and retention location. Add “lineage confidence” (high/medium/low). Treat low-confidence controls as risk items with due dates.
Who This Is For / Not For
Best fit: seed to Series B SaaS handling customer or employee data
If your buyers include IT/security reviewers and your product touches customer or employee information, this model gives you a practical path. It is designed for time-poor teams where every hour moved from compliance chaos back to product/sales matters.
Not a fit: pre-revenue prototypes with no enterprise sales motion yet
If you’re pre-revenue and no buyer is requesting SOC 2 signals, full program spend may be premature. You still need sensible security basics, but formal cadence can be lighter until sales motion proves urgency.
Edge case: AI startups with sensitive training/inference data
AI teams often face elevated buyer scrutiny around data governance, access controls, and model-operation hygiene. Even before full attestation timing, document data flows, training data provenance boundaries, and role-based access rules. That documentation pays off in both diligence and internal decision-making.
Money Block: Coverage Tier Map (what changes by budget)
- Tier 1 ($500): Baseline identity, MFA, policy control ownership.
- Tier 2 ($1,000): Device posture + logging basics + stronger JML routine.
- Tier 3 ($2,000): Repeatable monitoring, vendor risk cadence, structured IR drills.
Neutral action: choose the lowest tier that still protects active pipeline opportunities.
Common Mistakes That Inflate SOC 2 Costs
Buying enterprise tools before control ownership exists
Tooling without ownership is expensive wallpaper. I once saw three overlapping products deployed while nobody owned access recertification. Result: more notifications, less accountability.
Treating SOC 2 as an annual project instead of a weekly operating rhythm
Annual sprint thinking creates evidence debt. Weekly rhythm keeps proof small, fresh, and attributable. If a task is “quarterly,” put a monthly checkpoint in front of it to avoid surprise failures. Teams can borrow discipline from exam prep cadence models like an OSCP-style time management plan to keep routine reviews on schedule.
Over-scoping trust criteria too early
Scope creep is real. Start with a pragmatic scope aligned to buyer demand and operational capacity. You can expand later, but retreating from an over-scoped program is messy and morale-draining.
Here’s what no one tells you… the cheapest quarter often becomes the most expensive year
Deferred cleanup compounds. Every skipped review or undocumented exception becomes a future meeting, then a bigger meeting, then a timeline slip. The goal is not “spend less today.” The goal is “avoid rework tax all year.”
Money Block: Mini Calculator
Use three inputs:
- Tooling monthly cost (T)
- Internal monthly hours for SOC 2 tasks (H)
- Blended hourly internal rate (R)
Estimated real monthly spend = T + (H × R)
Example: T=$900, H=22, R=$80 → real spend ≈ $2,660/month.
Neutral action: calculate this once before approving any new software contract.
Don’t Do This: 7 Budget Traps That Trigger Rework
Mistaking “policy complete” for “control operating”
PDFs don’t pass audits; operating controls do. A policy is intent. Evidence is reality.
Ignoring vendor inventory until the auditor asks
Vendor lists built in panic mode are always incomplete. Keep a live inventory with owner and review cadence.
Delaying evidence mapping until pre-audit month
Late mapping creates rework storms. Build evidence mapping from week one.
Underestimating customer-requested add-ons beyond SOC 2
Many buyers ask for more than a report: pen test summaries, incident history statements, encryption details, retention controls, or custom addenda. Plan capacity for these requests and keep a reusable artifact library with a professional reporting template plus a tested proof screenshot standard.
Here are seven traps in one glance:
- Unclear control ownership
- Overlapping tools with no process fit
- No exception workflow
- Stale access review records
- Weak offboarding enforcement
- No tabletop/drill discipline
- Audit scheduled before process stability
Neutral action line: pick the top two traps you’re currently exposed to and assign owners today.
Curiosity Check: Can You Delay SOC 2 and Still Win Enterprise Deals?
Signs you can wait 1–2 quarters without revenue damage
- No enterprise procurement gates in active deals.
- Buyers accept a structured security package instead of report timing.
- Your pipeline is founder-led SMB/mid-market with low formal compliance burden.
Signals you’re already late (RFP friction, procurement stalls, legal redlines)
- Security questionnaires repeatedly escalate to leadership.
- Legal redlines require formal attestation timelines.
- Deals pause at “security review complete?” for multiple accounts.
Open loop: the deal-stage question that predicts whether delay is fatal
Ask your account team: “How many opportunities this quarter include security/procurement steps before signature?” If that number is growing and your response process is manual, delay is usually costly.
Short Story: The Month We Stopped Guessing (120–180 words)
A small B2B startup I supported had nine active deals and one part-time ops owner handling security requests. Everyone believed SOC 2 could wait “one more quarter.” Then procurement asked for evidence trails, not just policy docs. Suddenly, sales calls turned into status apologies. We paused for one week, mapped every control owner, and ran a strict Friday evidence routine.
No new fancy tool on day one—just ownership and cadence. By week three, questionnaire turnaround dropped from “we’ll circle back next week” to same-day for standard asks. The team still felt busy, but no longer brittle. The surprise was emotional: people slept better because they could point to operating controls, not intentions. The biggest lesson wasn’t technical. It was this: confidence appears when work has a home, a person, and a date.
- Track procurement stage frequency in active deals.
- Measure questionnaire turnaround time weekly.
- Escalate budget lane when revenue friction appears.
Apply in 60 seconds: Ask sales for the count of deals currently blocked by security review.
Next Step: Build Your 90-Day SOC 2 Budget Sprint
Week 1: baseline controls + owner assignment
Create a single control register: control name, owner, frequency, evidence location, reviewer. Keep it boring and clear. Boring scales.
Week 2–4: tooling decisions using the $500/$1,000/$2,000 model
Buy only what closes known process gaps. If a tool does not reduce manual evidence time or improve control reliability, defer it. When you test external controls, align technical depth to scope with a right-sized pentesting tool stack instead of adding overlapping platforms.
Week 5–8: evidence map + monthly operating cadence
Run a recurring cadence with a fixed agenda: overdue controls, evidence quality, exceptions, and upcoming buyer requests. Keep notes standardized with a lightweight, searchable system similar to this structured note-taking workflow.
Week 9–12: readiness checkpoint and go/no-go for audit window
Assess maturity honestly: are controls operating predictably, with attributable evidence, across at least one full cycle? If not, shift timeline before paying milestone costs.
Money Block: Quote-Prep List
- Current tool inventory and seat counts
- Control register with owners and frequencies
- Target trust criteria/scope assumptions
- Evidence sample quality from last 30 days
- Expected customer timing pressure (next 2 quarters)
Neutral action: gather these five items before speaking to advisors or auditors to get cleaner estimates.
Infographic: SOC 2 Budget Lanes at a Glance
$500/mo
Goal: Foundational credibility
Focus: Identity + MFA + policy ownership
Risk: Manual evidence fatigue
$1,000/mo
Goal: Sales-ready operations
Focus: Device posture + logging + JML rigor
Risk: Partial automation gaps
$2,000/mo
Goal: Audit-ready repeatability
Focus: Monitoring + vendor risk + IR drills
Risk: Over-tooling without ownership
Bottom line: Choose the smallest lane that protects current revenue motion and can operate every week.
Two frameworks are worth skimming as you operationalize this: NIST guidance can help structure practical control thinking, and CISA’s resources reinforce baseline cyber hygiene expectations for growing teams.
FAQ
How much does SOC 2 cost a startup per month in the US?
For practical planning, many early teams operate in a lane between $500 and $2,000 monthly for program operations, plus periodic milestone costs like readiness and audit. The right number depends on headcount, data sensitivity, and enterprise sales pressure.
Is $500/month realistic for SOC 2 readiness?
Yes, for early teams with tight scope and strong execution discipline. It is realistic when identity, MFA, access lifecycle, and evidence cadence are consistent. It becomes unrealistic when questionnaires, buyer scrutiny, or team complexity accelerate.
What’s included in a $1,000/month SOC 2 budget?
Typically: foundational compliance operations, improved endpoint/device posture checks, basic logging discipline, and stronger onboarding/offboarding rigor. This lane usually buys speed and reliability rather than breadth.
Do I need a security engineer before starting SOC 2?
Not always. Many startups start with ops/founder ownership plus targeted advisor support. You do need clear control ownership and escalation paths. Without ownership, no role title will save the program.
Can I pass SOC 2 with mostly manual evidence collection?
It can be possible in simpler environments, but manual-heavy programs often struggle with consistency over time. As evidence burden grows, selective automation becomes cost-effective because it reduces rework and timeline risk.
What costs are one-time vs recurring for SOC 2?
Recurring: core tooling, ongoing control operations, periodic training and review cycles. One-time or milestone: initial implementation work, readiness projects, and audit/report windows. Keep those categories separate in budgeting.
How long should we budget before the first SOC 2 report?
Timelines vary by maturity and scope. A practical plan starts with a 90-day operations sprint to stabilize controls, then decides whether readiness is strong enough for the next milestone phase. Teams that already run disciplined routines—like a time-boxed weekly execution model—usually adapt faster.
Should we do Type I first or go straight to Type II?
It depends on buyer timing and operational maturity. If immediate assurance signaling matters and operating history is still maturing, teams often use staged approaches. If operations are already steady, planning directly for sustained operation can be sensible.
Can SOC 2 help close enterprise deals faster?
Often yes—especially when your process improves questionnaire speed and confidence during procurement. The report matters, but operational responsiveness during diligence often matters just as much.
What happens if we fail audit readiness on timeline?
You usually absorb delay costs: team distraction, repeated evidence cleanup, and possible pipeline friction. The fix is rarely another tool purchase; it is usually a tighter ownership model and cleaner weekly cadence.
The curiosity loop from the opening closes here: the late-night panic shrinks when your budget model mirrors reality. Separate fixed tools, people-time, and milestone spend. Pick the lane your team can operate every week. Then run a 15-minute kickoff today: assign owners, set first due dates, and calculate your real monthly spend with labor included. That one step turns SOC 2 from a foggy future expense into a controlled operating system.
Last reviewed: 2026-02.

