
Silent Failures & Network Primitives
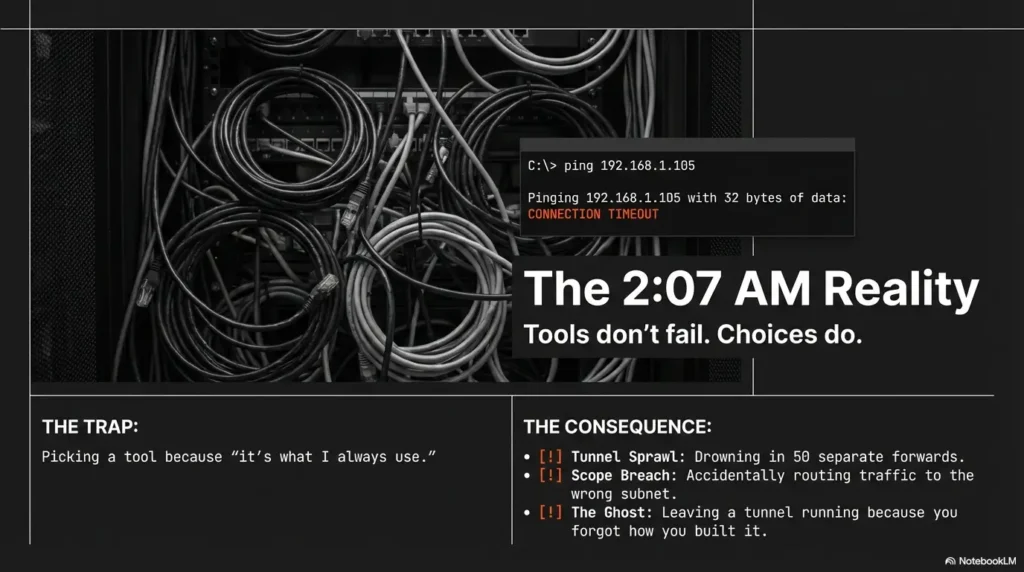
At 2:07 AM, tunnels don’t fail loudly. They fail quietly, with the exact kind of “it should work” confidence that ruins sleep.
If you’re choosing Chisel vs. Ligolo-NG for port forwarding and proxying, the real mistake isn’t picking the “wrong” tool. It’s picking the wrong network primitive and then spending an hour debugging symptoms that were baked into the choice.
Keep guessing and you’ll pay in tunnel sprawl, blown scope, or a pivot that’s harder to explain than the findings. This post helps you pick fast, on purpose: targeted forwards when you know the service, or a VPN-like pivot when you need the network to feel local, with clear blast-radius control and teardown discipline.
Quick definition: A TUN-based pivot uses a virtual network interface so your OS routes traffic through the tunnel like a lightweight VPN, making tools behave more “normally” across subnets. A SOCKS proxy is app-layer: great for selective workflows, but it won’t magically become routing.
- → Selection table first
- → The “why it broke” realities
- → Mini playbooks for your notes
Table of Contents
Who this is for / not for
For: operators who need a decision in 5 minutes
- Pentesters/red teamers choosing a tunnel for a single engagement
- Blue teams validating segmentation and egress controls (authorized testing)
- Lab builders who want repeatable pivot patterns (home lab, CTF, internal), especially if you already maintain a clean Kali lab logging routine for deconfliction and later write-ups
Not for: “I found a random IP and…”
- Anything unauthorized, ambiguous, or outside a signed scope
- “How do I bypass a company firewall” intent without explicit permission
- People needing malware-style persistence (different category, different ethics)
- Define the objective (one service vs many hosts).
- Choose the network primitive (forward / proxy / route).
- Control blast radius and teardown like it’s part of the deliverable.
Apply in 60 seconds: Write one sentence: “This tunnel exists to reach ___ from ___, and it ends when ___.”
Eligibility checklist (authorized tunneling)
- Yes/No: Do you have written scope that permits internal pivoting? (If not, start with a pen test SOW template that explicitly defines pivot allowances.)
- Yes/No: Are allowed egress ports/protocols documented for the test window?
- Yes/No: Do you have an agreed logging/deconfliction contact?
- Yes/No: Do you have a teardown verification step (not just “I closed the terminal”)?
- Yes/No: Are route/forward limits specified (least privilege)?
Neutral next action: If any answer is “No,” fix that in writing before you tunnel.
Choose in 30 seconds: Chisel vs Ligolo-NG selection table
The “what are you actually trying to do?” grid
| Need | Pick | Why | Watch-out |
|---|---|---|---|
| Single port to reach one service | Chisel | Lowest friction; targeted forward | Tunnel sprawl if requirements grow |
| Many services across subnets, “feel on the LAN” | Ligolo-NG | TUN routing; fewer per-port forwards | Routing mistakes expand scope fast |
| SOCKS proxy workflow (browser/proxychains-style) | Usually Chisel | Simple choke point, selective access | DNS/app quirks when it’s not true routing |
| Transparent routing (TUN), fewer forwards overall | Ligolo-NG | Tools behave more “normally” | Debugging becomes a networking quiz |
| Lowest friction drop-in on restrictive hosts | Chisel | One tunnel, one job, predictable | You may still need multiple tunnels later |
| Cleaner multi-host pivot ergonomics | Ligolo-NG | Route once, explore many | Discipline required: routes, exposure, teardown |
Decision shortcuts by constraint
- Egress is tight → favor the tool you can keep minimal and predictable (often Chisel).
- Scope is broad → favor routing-based pivots (often Ligolo-NG).
- Operators are mixed-skill → favor the approach your team can explain at 9 AM and still understand at 9 PM.
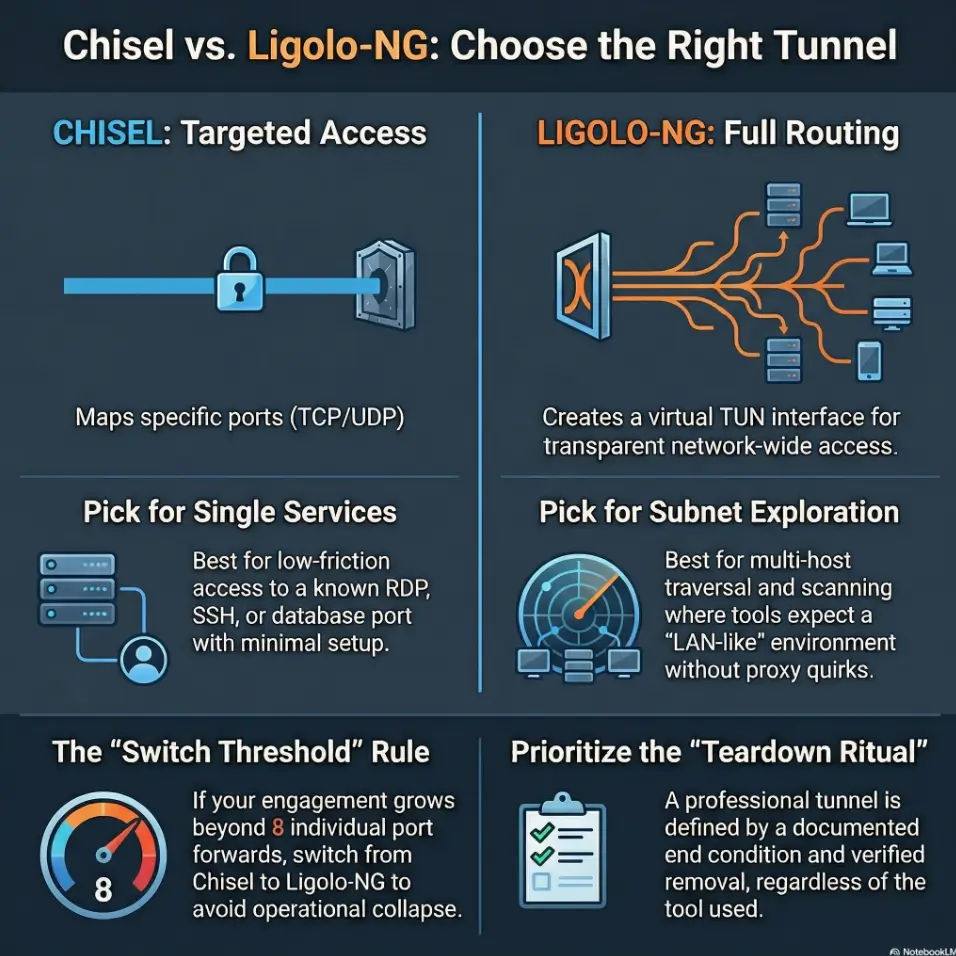
Decision card (print-this-in-your-brain)
Pick Chisel when…
- You know the destination service/port.
- You want minimal moving parts.
- You’re optimizing for fast setup and clean teardown.
Time cost: Low upfront, can grow with each new forward.
Pick Ligolo-NG when…
- You need many hosts/services across routes.
- Your tooling expects “normal” network reachability.
- You can manage routing scope intentionally.
Time cost: Higher upfront, often lower per-new-target later.
Neutral next action: Pick one card, then write the smallest possible route/forward set that satisfies scope.
Use-case anatomy: “Port forward” vs “Proxy” vs “VPN-like pivot”
Here’s the part we pretend is obvious, until it isn’t: these three are different “network primitives.” Mix them up and your tools start gaslighting you. I once spent 42 minutes blaming a scanner, only to realize I’d asked a proxy to behave like routing. That’s like asking a taxi to replace a subway line. (If this section makes your brain itch, keep Networking 101 for hackers bookmarked for the “wait, what’s actually happening?” moments.)
Port forwarding when you know the destination
- Best for: RDP/SSH/DB/admin panels you already identified
- Nice side effect: Easy to explain in a report (“we forwarded X to test Y”), especially when you follow a consistent how to read a penetration test report narrative that maps access paths to findings
- Failure mode: you keep adding forwards until you’re drowning in your own tunnels
Proxying when you want “many things, selectively”
- Best for: quick browsing/internal recon through a single choke point
- Nice side effect: you can constrain tooling through one proxy config
- Failure mode: DNS and app behaviors get weird when not truly “routed” (if you’ve ever chased phantom lookups, you’ll want the ProxyChains DNS leak fix handy)
VPN-like pivot when you want the network to feel local
- Best for: multi-service traversal, scanning, tooling that expects routing
- Nice side effect: less per-port housekeeping when exploring broadly
- Failure mode: you forget routing is powerful and widen blast radius accidentally
Show me the nerdy details
SOCKS (commonly SOCKS5) is an application-layer proxy concept. It helps applications traverse network boundaries via a proxy server, but it does not magically become full network-layer routing. Standards bodies describe SOCKS as a “shim” between application and transport layers, which is a polite way of saying: some tools will be happy; others will throw tantrums.
Chisel, explained like a deployment checklist
Chisel’s superpower is emotional: it reduces decisions. You can treat it like a single-purpose cable. In the Chisel project’s own description, it’s a fast TCP/UDP tunnel transported over HTTP and secured via SSH, which is a fancy way of saying “this thing is designed to be carried into awkward networks and still do its job.”
What Chisel is “best at” in real life
- Fast TCP forwards when you have a known target
- Simple client/server model that’s easy to brief to a teammate
- Predictable “one tunnel, one job” behavior (great for least privilege)
What Chisel is “bad at” (or just annoying at)
- Managing lots of forwards at scale (the tunnel spaghetti problem)
- Feeling “LAN-native” across multiple subnets without extra glue
- Keeping your own notes clean when the scope expands mid-week
Here’s what no one tells you…
Chisel shines when your target list is small. If your scope turns into “the whole internal zoo,” Chisel can become a bowl of cables labeled “TEMP_FINAL2.” I’ve watched talented operators burn 90 minutes simply re-deriving what a forward was for after lunch. That’s not a skill issue. That’s an ergonomics issue.
- Great for targeted validation of a small set of services.
- Easier to justify and document in a report.
- Safer by default when you keep forwards minimal.
Apply in 60 seconds: Write the forward as “Purpose: ___, Destination: ___, Ends when: ___.” If you can’t, you’re not ready.
Ligolo-NG, explained like a pivot workstation
Ligolo-NG is for the moment your engagement stops being “reach that one thing” and becomes “map the neighborhood.” Its design leans into a TUN interface approach, aiming for transparent network access that feels closer to being on the internal network. In the Ligolo-NG project’s own description, it establishes tunnels from a reverse TCP/TLS connection using a TUN interface, intentionally avoiding a SOCKS dependency for the core routing experience. (If you want the operational “from zero to working” version, pair this section with a Ligolo-NG setup guide so you don’t learn TUN basics by stepping on rakes.)
What Ligolo-NG is “best at” in real life
- TUN-based access that feels more like being on the internal network
- Reduced need for per-port forwards when exploring broadly
- More natural workflows for multi-host pivoting when routes are clean
What Ligolo-NG demands from you
- Comfort with routing/TUN concepts (and the humility to test them)
- Operational discipline: what routes are active, what’s exposed, what’s logged
- Team clarity: everyone needs the same mental map of what’s reachable
Let’s be honest…
If you’re rusty on routing, Ligolo-NG can feel like it “works” right up until it doesn’t, and then debugging becomes a networking quiz you did not study for. The upside is worth it: fewer forwards, fewer tool tantrums, and a cleaner story when the engagement requires broader internal traversal. The downside is also real: one sloppy route choice can quietly expand access beyond what you intended.
Show me the nerdy details
A TUN interface is a virtual network interface that operates at the IP layer. It’s a building block used by VPN-like tools to inject and route IP traffic through a tunnel. The “magic” you feel with TUN usually comes from the OS routing table doing what it does best: sending packets where you told it to, including places you might not have meant if you were moving fast.
Mini calculator: “Will I drown in forwards?”
This is not math-magic. It’s a gut-check you can explain to a teammate.
Estimated forwards will appear here.
Neutral next action: If the number surprises you, change the architecture before you change your sleep schedule.
The moment you regret the wrong pick (3 scenarios)
Scenario 1: “It’s just one database… until it isn’t”
You start with one forward (a DB), then you add web, then you add admin, then suddenly there’s a “quick check” on an internal API. Your tunnel list grows like a houseplant you forgot you owned. I’ve been there, staring at a terminal tab bar that looked like a tiny cemetery of intentions.
Open loop: how many forwards is your personal breaking point?
Scenario 2: The toolchain expects routing
Some scanners, updaters, and “helpful” internal tooling behave best when the network path looks normal. If you force everything through a proxy-only posture, you can get partial visibility and confusing misses. That’s the worst kind of failure: the one that looks like success until you write the report. (This is exactly why a well-defined security testing strategy calls out the network primitive up front, not as an afterthought.)
Scenario 3: You need repeatability, not heroics
You’ll run this again next week. If your method requires improvisation, it’s not a method, it’s a performance. Choose the workflow you can document and re-run without negotiating with your future self.
- Chisel fails by accumulation (too many forwards).
- Ligolo-NG fails by misconfiguration (routes you didn’t mean).
- Both fail by poor notes and no teardown ritual.
Apply in 60 seconds: Decide now what “success” looks like: one service reachable, or a set of subnets reachable.
Common mistakes that waste hours (and how to avoid them)
Mistake 1: Treating “proxy” as “routing”
- Symptom: random tools fail, DNS behaves oddly, partial app breakage
- Fix: decide up front whether you need transparent routing
Mistake 2: Building tunnel spaghetti
- Symptom: you can’t explain your own forwards after lunch
- Fix: name conventions + a tiny tunnel inventory (host, port, purpose)
Mistake 3: Forgetting egress reality
- Symptom: works in lab, fails in prod due to outbound restrictions
- Fix: validate allowed outbound ports and protocols early (within scope)
Mistake 4: Over-broad pivot exposure
- Symptom: you accidentally make too much reachable
- Fix: least-privilege routes/forwards, short-lived sessions, explicit teardown
Show me the nerdy details
In practice, the most common time-sink is not the tunnel itself. It’s name resolution, split-horizon DNS assumptions, and application behaviors that implicitly depend on “local” network conditions. Routing-based pivots often reduce these surprises because the OS and tools behave more like they’re on a real network path, but they demand careful scoping to avoid accidental reach expansion.
Quote-prep list (what to gather before you choose)
- Allowed outbound ports/protocols for the test window (and who approved).
- Target list estimate: 1–3 services or multiple subnets?
- Which tools you must run (browser only, scanner suite, custom apps).
- Logging expectations: what defenders will see and how you’ll explain it.
- Teardown verification: how you prove the tunnel is gone (helpful if you already standardize screenshots using a ShareX screenshot naming pattern so evidence is searchable under pressure).
Neutral next action: Paste this list into your engagement notes template and fill it before tunneling.
Don’t do this: risky habits that trigger incidents
“I’ll just leave it running”
Why it’s dangerous: persistence-by-accident, audit nightmares, and a very awkward debrief. I’ve seen this turn a clean engagement into a week of “confirm it’s gone” emails.
Better: session windows + a teardown checklist you actually execute.
“More routes means faster testing”
Why it’s dangerous: expands unintended access paths and can blur what you truly validated versus what was merely reachable.
Better: expand only when a specific test requires it, and document the reason.
- Time-box sessions.
- Keep routes/forwards least privilege.
- Prove teardown.
Apply in 60 seconds: Add a calendar reminder labeled “Verify tunnel teardown” before you start.
Operational fit: stealth, stability, and observability tradeoffs
Stability under flaky networks
Which approach degrades more gracefully depends on topology and goals. The boring truth: fewer moving parts often equals fewer surprises. A targeted forward is mechanically simple. A routed pivot is operationally elegant but introduces more state to reason about. If your link is unstable, plan for it the same way you plan for power outages: with explicit recovery steps and short session windows.
Detection surface and logging reality
Tunnels leave traces. That’s not paranoia, that’s adulthood. The best question is not “can I hide this,” but “can I justify this” inside the engagement report. Plan in advance: what you’ll log, what you’ll avoid, and how you’ll describe the tunnel’s purpose in plain language to stakeholders who do not care about your tool preference.
This is also where scoping language and expectations matter; if your engagement paperwork doesn’t match reality, revisit your penetration test limitation of liability assumptions and align them before you create accidental drama.
The open loop you should answer before you start
If you had to defend your tunnel choice in a post-engagement debrief, what would you say? If your answer is “because it’s what I always use,” that’s a smell. Not a crime. A smell.
Infographic: Tunnel choice in 4 questions
1) Objective?
One service vs many hosts
2) Network need?
Forward / Proxy / Route (TUN)
3) Constraints?
Egress limits, host friction, team skill
4) Scope control?
Least privilege + teardown proof
If “one service” + “forward/proxy”
Start Chisel, keep it minimal, document purpose.
If “many hosts” + “route (TUN)”
Start Ligolo-NG, scope routes tightly, verify teardown.
“Use-case recipes”: pick-your-path mini playbooks
Recipe A: Single-service access (one target, one win)
- Choose: Chisel-first
- Goal: minimal footprint, fast setup, clean teardown
- Operator note: keep a 3-line tunnel inventory: purpose, destination, end condition
I’ve used this pattern for “one internal admin panel” engagements where the real work was the app test, not the network gymnastics. The tunnel should feel like a utility bill: boring, predictable, and paid on time.
Recipe B: Internal exploration across many hosts
- Choose: Ligolo-NG-first
- Goal: route once, explore many, keep scope tight
- Operator note: write down exactly which subnets are in-scope before you route
This is where your future self either thanks you or curses you. When it’s done well, it feels like someone turned the lights on in a complicated building. When it’s done sloppy, it feels like you opened every door and forgot which ones were allowed. If you want a clean “which pivot pattern when” mental model, the OSCP pivoting tool choice breakdown is a surprisingly practical lens even outside exam land.
Recipe C: Mixed reality (you’ll need both)
- Start with: Chisel for quick validation
- Graduate to: Ligolo-NG when traversal turns into multi-host workflow
- Operator note: set the “switch threshold” (e.g., more than 8 forwards, or more than 2 subnets)
Show me the nerdy details
A hybrid plan is often the most honest: forwards are great for precise access and reporting clarity; TUN routing is great for breadth and tool compatibility. The key is to define the moment you switch approaches so it doesn’t happen in a panic at the worst possible time.
Next step: one concrete action
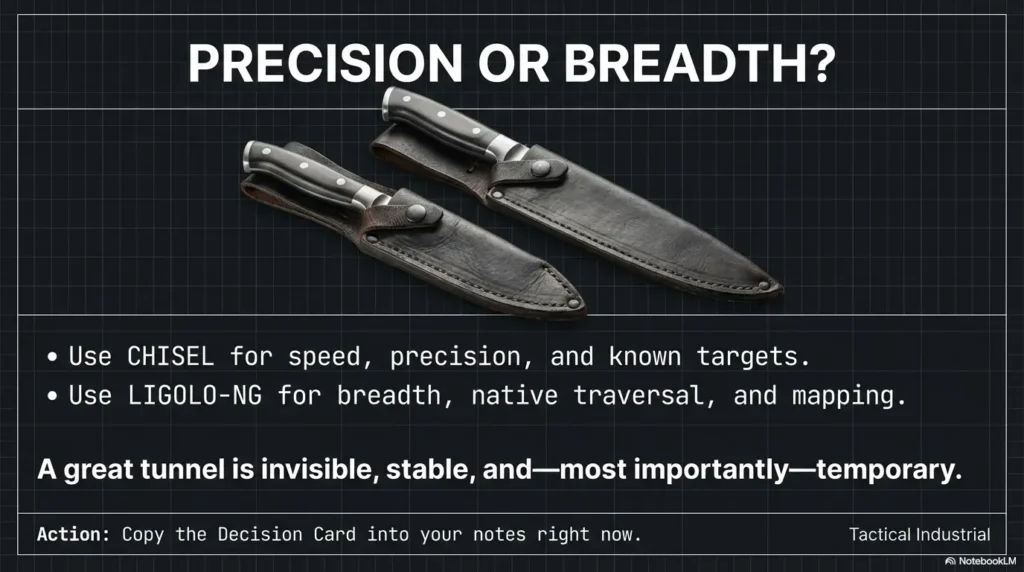
Build your “Tunnel Decision Card” (5 lines)
Write this into your notes template right now. Not later. Your future self is a critic, not a collaborator.
- Objective (single service vs many hosts)
- Network need (forward / proxy / route)
- Egress constraints (known allowed outbound)
- Blast-radius control (what must NOT become reachable)
- Teardown trigger (when session ends, how you verify it’s gone)
- Fewer surprises mid-engagement.
- Cleaner reporting and stakeholder confidence.
- Faster handoffs between teammates.
Apply in 60 seconds: Copy the five lines into your engagement template and fill them before you run anything.
FAQ
Is Chisel or Ligolo-NG better for port forwarding?
If your goal is targeted access to specific services (a known host/port pair), Chisel-style port forwarding is often the simpler, faster fit. If your “port forwarding” is really a proxy for “I need broad internal reach,” you’ll usually be happier moving to a TUN/routing approach like Ligolo-NG so you don’t accumulate dozens of forwards.
When should I use a SOCKS proxy instead of a TUN tunnel?
Use SOCKS when you want selective access for specific apps that behave well behind a proxy (browser, a few tools) and you want one choke point. Prefer TUN when your tools expect normal routing behavior, or when you’re spanning multiple hosts/subnets and don’t want “proxy weirdness” to become your main hobby.
Does Ligolo-NG replace the need for individual port forwards?
Often, yes for exploration, because routed access can make many services reachable without per-port setup. But you may still use individual forwards for tight scope control, for reporting clarity, or for special cases where you want a deliberately narrow path.
What’s the easiest setup when outbound traffic is restricted?
The easiest setup is the one that matches what’s explicitly allowed in scope and egress policy. Practically, many teams start with the minimal, predictable approach first (often a targeted forward) and only expand to broader routing if the engagement requirements justify it. The key is to validate permitted egress early and keep your tunnel purpose narrow.
Which tool is better for pivoting into multiple internal subnets?
When you truly need multi-subnet traversal and your workflow benefits from “LAN-like” behavior, a TUN-based approach tends to fit better. The tradeoff is operational responsibility: routing choices must remain least privilege, documented, and time-boxed.
Can I chain tunnels (multi-hop), and when is that a bad idea?
Multi-hop can be legitimate in authorized testing, but it increases complexity and failure modes. It’s a bad idea when it becomes your default instead of a justified requirement, or when you can’t clearly document the chain, its purpose, and teardown steps. If you can’t explain the chain on one whiteboard, it’s probably too much.
How do I keep tunnel scope least-privilege during an engagement?
Start with the smallest set of forwards/routes that satisfy the test objective. Expand only when a specific test requires it. Document every expansion with a reason and an end condition. Then verify teardown in a way you can defend (not just “I closed my laptop”).
What breaks most often when proxying internal apps?
DNS assumptions, mixed-content behavior in web apps, and tools that don’t respect proxy settings consistently. Proxying is powerful, but it’s not routing. The fastest fix is often deciding up front whether you need transparent routing instead of trying to patch proxy behavior with guesswork.
What should I document in a pentest report about tunneling?
Document the purpose, scope, and controls: what the tunnel enabled (specific test objectives), what was reachable (least privilege), how long it existed (time-box), and how it was torn down (verification). Stakeholders care less about the tool name and more about controlled, explainable behavior.
How do defenders detect tunneling activity in logs?
Defenders look for unusual outbound connections, long-lived sessions, atypical endpoints, unexpected volumes, and patterns that don’t match baseline behavior. In authorized testing, plan deconfliction and logging expectations up front so you can distinguish “expected test traffic” from true incidents. If you’re in the “post-engagement reality” phase, this is also where an incident response retainer conversation becomes the difference between calm triage and organizational chaos.
Conclusion
Remember the curiosity loop from the top: paring knife versus chef’s knife. Here’s the closure: Chisel wins when you want precision and speed, and you can keep the target list small. Ligolo-NG wins when you want network-native traversal, fewer per-port chores, and a workflow that scales to multiple hosts without turning your notes into modern art. Neither is “better.” One is better aligned to your objective and constraints.
If you do one thing in the next 15 minutes, do this: copy the Tunnel Decision Card into your template, fill it, and set a teardown trigger before you open a tunnel. That single ritual saves more hours than any tool debate ever will.
Last reviewed: 2026-02.

