
Stop Letting Security Reviews Kill Your Enterprise Momentum
Enterprise deals usually do not collapse in the pitch room. They stall in the security lane, where a single missing control can quietly add 10 to 21 days of drag and turn a “verbal yes” into quarter-end silence. For B2B SaaS teams entering enterprise motion, SAML SSO is rarely a technical vanity project. It is the difference between pipeline momentum and procurement limbo, especially when it appears alongside recurring concerns in your vendor security questionnaire process.
The pain is specific: late-stage “SSO required” objections, expansion freezes at IT review, and champions who lose internal leverage at handoff.
This guide provides a practical timing model to decide when SAML becomes revenue-critical, what Minimum Viable SAML must include, and how to roll it out without overbuilding.
The Roadmap
- • Where most teams get it wrong
- • When the signal becomes unmistakable
- • Turning identity friction into closed-won velocity
30-Day Execution Blueprint Included
SAML SSO becomes urgent when revenue friction is measurable, not when engineering has spare time. If two or more triggers are active, repeated “SSO required” objections, enterprise-only cycle extension, procurement drop-off, expansion freezes, and security-review stalls, SAML moves from “nice roadmap item” to “pipeline protection infrastructure.”
Table of Contents
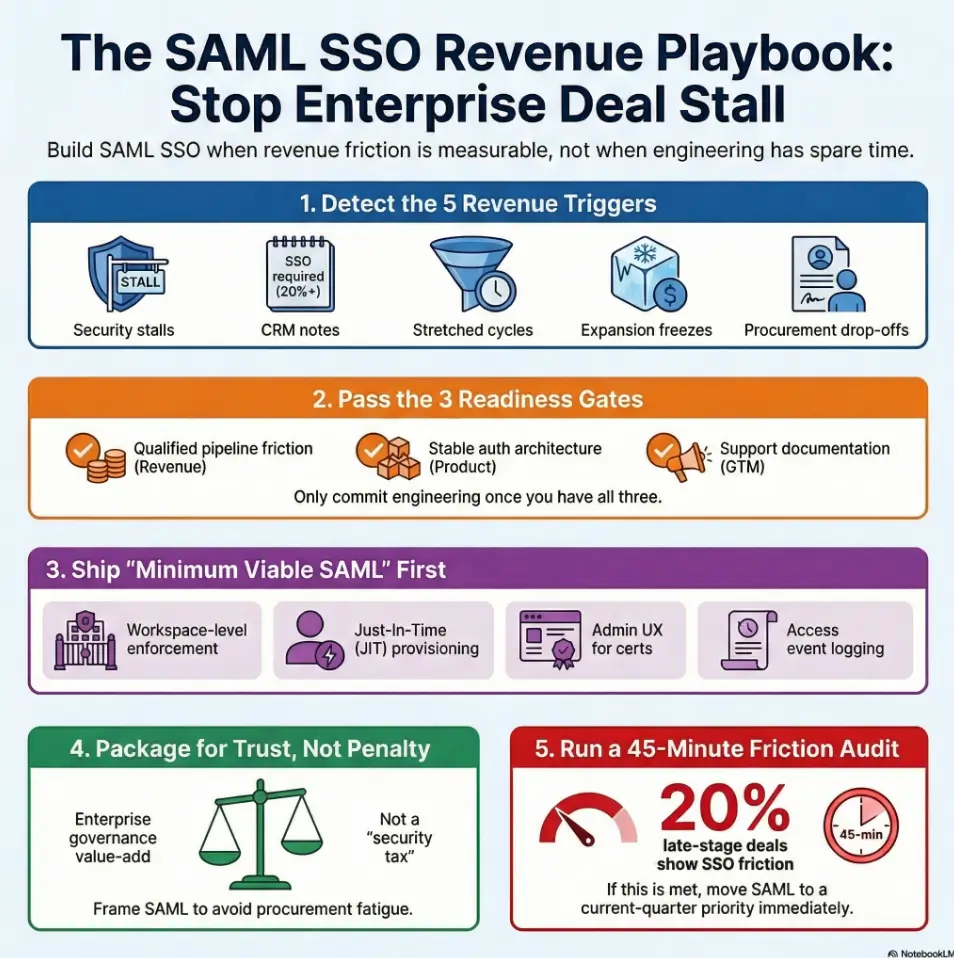
1) Trigger First: The Revenue Signals That Mean “Build SAML Now”
Signal #1: Security review stalls after verbal yes
I have seen this movie too many times: clean demo, excited champion, verbal “we love it,” and then a two-week silence during security intake. The silence is usually not indecision. It is a control gap. SAML SSO is often one of the first practical controls buyers scan for because it ties identity policy to corporate risk posture.
If security review introduces a delay of 10 to 21 days in enterprise opportunities while SMB motion remains stable, that split is a bright red timing signal. The deal is not dead. It is stuck behind identity governance expectations, often alongside weaknesses in security testing strategy and documented controls.
Signal #2: “SSO required” appears in late-stage notes weekly
When this phrase repeats across multiple accounts, do not treat it as noise. Treat it as a demand cluster. One founder told me, half joking, “Our CRM has a new religion and it is called ‘must support Okta.’” The joke was funny. The lost quarter was not.
Practical benchmark: if “SSO required” appears in 20% or more of late-stage enterprise notes for two consecutive weeks, SAML is likely a current-quarter priority candidate.
Signal #3: Time-to-close stretches in enterprise segment only
Watch cohort-specific cycle time, not blended averages. Blended dashboards hide enterprise drag the way fog hides cliffs. If enterprise cycle length expands by even 15% while PLG or mid-market remains flat, identity requirements are often part of the bottleneck stack.
Anecdote from the trenches: one product-led company thought pricing caused delays. After a stage-level audit, the longest extension lived between security questionnaire and legal handoff. SAML plus better security-response docs cut that stage friction dramatically.
Signal #4: Expansion deals freeze at IT approval
Expansion deals are where “we can live without SAML for now” starts charging interest. Departmental buyers may get started with local auth. Company-wide rollout usually cannot. Central IT asks for policy enforcement, controlled provisioning, and offboarding confidence.
If your expansion pipeline has healthy product usage but repeated IT holds, that is not a customer success problem. It is a platform trust problem, and frequently shows up with gaps in security metrics leadership can track.
Signal #5: Champion momentum dies in procurement handoff
Champions sell internally with narrative. Procurement asks for controls and evidence. This is where momentum turns fragile. Without SAML, your champion must defend exception risk. Most will not spend political capital there.
Pattern interrupt: If your CRM says “next quarter,” this may be why. The opportunity did not vanish. It hit an internal policy wall you did not design for.
- Track SSO objections by stage, not by anecdote.
- Split cycle-time analysis by segment.
- Escalate when two or more triggers persist for one sprint.
Apply in 60 seconds: Add an “SSO blocker” checkbox in CRM for every enterprise opportunity this week.
2) Cost of Delay: What SAML Absence Quietly Does to ARR
Pipeline leakage math: where “almost won” turns into zero
Most startups underestimate identity-related leakage because they classify it as “timing” or “internal budget.” In practice, missing SAML creates a distinctive decay pattern: opportunity stays open, confidence drops, competitor with enterprise-ready auth gets preferred, then your forecast slips into soft excuses.
Simple leakage lens: count late-stage enterprise opps where SSO is requested, then multiply by historical win probability if that blocker were absent. Even conservative math can expose six-figure quarterly leakage in seed-to-Series C motions.
Hidden CAC inflation from repeated security escalations
Every extra security call pulls senior people into custom reassurance loops. That labor is real CAC. Founder time, security lead time, and sales engineering time all compound. One team I advised tracked 11 extra hours per enterprise deal on “auth reassurance” alone, with no durable asset created.
SAML does not eliminate questions, but it converts bespoke reassurance into repeatable process. That shift protects both margin and morale, especially if paired with a clear incident response retainer plan for enterprise diligence.
Churn-by-design risk in multi-team accounts
Without centralized identity controls, multi-team growth can create account fragility. When a security incident or offboarding scare hits, trust can crack quickly. You may retain usage in one pocket while losing strategic footprint in another.
Open loop: The deal didn’t die, it decayed. Can you spot where? Usually at the seam between product enthusiasm and enterprise governance.
Money Block: Mini Calculator (SSO Friction Cost)
Use this quick model in your RevOps meeting:
- Input 1: Late-stage enterprise opps this quarter with SSO objection
- Input 2: Average contract value (ACV)
- Input 3: Estimated win-rate lift if SAML blocker is removed (conservative)
Output: Potential protected ARR = Opps × ACV × Win-rate lift.
Neutral action: run this with low, medium, and high assumptions before roadmap planning.
Show me the nerdy details
Deeper technical notes, benchmarks, or methodology. In practice, use stage-conversion cohorts rather than top-of-funnel volume. Compare opportunities with explicit SSO objections versus matched opportunities without them. Control for segment and ACV band to avoid false confidence.
3) Buyer Reality Check: What Enterprise Security Teams Actually Ask
Baseline controls buyers expect before legal redlines
Enterprise buyers do not evaluate SAML as an isolated checkbox. They read it as part of operational maturity. The baseline conversation usually includes SSO enforcement options, role control clarity, access logging, and incident response posture. If these answers sound improvised, procurement confidence drops fast.
In US enterprise buying flows, references to SOC 2 reports, NIST-aligned practices, and identity standards are common because they reduce diligence ambiguity. Familiar frameworks help security teams move from suspicion to decision, and tools like a SOC 2 budget calculator help founders frame tradeoffs earlier.
IdP compatibility expectations (Okta, Entra ID, Google Workspace)
Most US B2B motions should prioritize compatibility with widely deployed enterprise identity providers: Okta, Microsoft Entra ID, and Google Workspace. Supporting these does not mean custom-building for every tenant edge case on day one. It means your onboarding path is predictable for the majority.
I once watched a strong product lose momentum because the team optimized for a niche identity stack first. They were proud of technical elegance, and honestly, deserved some pride. Revenue, however, cares about common-path readiness.
Role mapping and deprovisioning questions that kill velocity
Security reviewers will ask what happens when employees move teams or leave. If your answer is “admin removes users manually,” expect hard follow-ups. Deprovisioning clarity is not bureaucracy theater. It is risk containment with audit consequences.
Pattern interrupt: Let’s be honest… “We have OAuth” won’t satisfy this stage. OAuth is useful for delegated authorization scenarios, but procurement frequently needs enterprise identity lifecycle confidence anchored in SAML SSO patterns and admin governance.
Money Block: Decision Card (When A vs B)
When OAuth-led login is enough: early PLG adoption, individual accounts, low governance requirements.
When SAML becomes mandatory: centralized IT purchasing, formal security review, policy-enforced enterprise rollouts.
Time/cost trade-off: OAuth may ship faster; SAML often closes larger deals faster once enterprise motion begins.
Neutral action: align auth strategy to your top two segments, not to engineering preference.
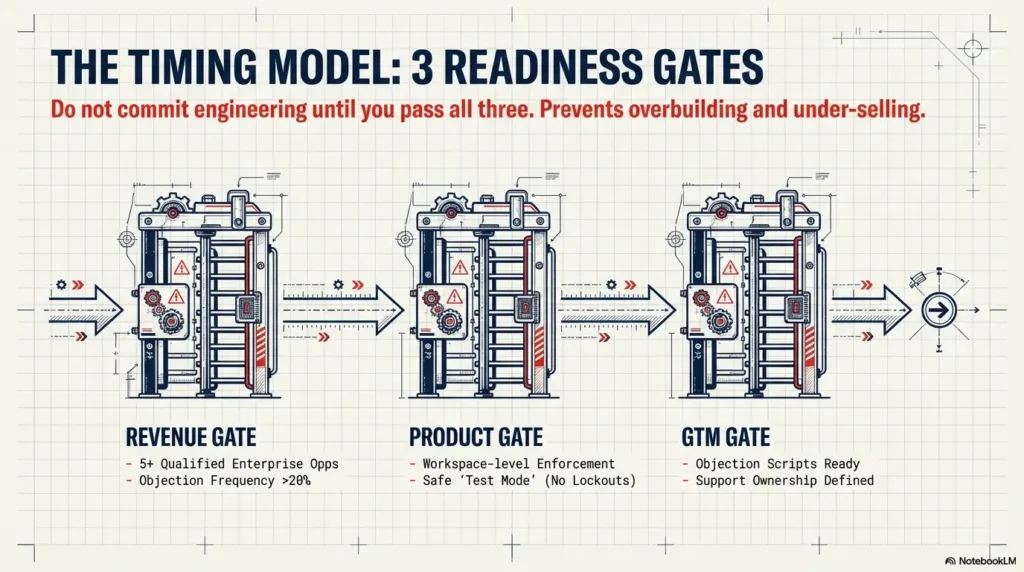
4) Timing Model: The 3 Readiness Gates Before You Commit Engineering
Gate 1: Revenue gate (qualified pipeline threshold + objection frequency)
Do not start with architecture. Start with proof of friction. A practical revenue gate might be: at least 5 qualified enterprise opportunities in active cycle plus SSO/security objections in 20% or more of late-stage notes. Your exact numbers can vary by ACV profile, but the logic should not.
When I skip this gate with teams, two bad endings appear: overbuilt features that never monetize, or delayed builds that cost two quarters of enterprise momentum.
Gate 2: Product gate (auth architecture can support enterprise controls)
Can your current auth model enforce workspace-level SSO? Can admins safely test without locking out teams? Can you separate tenant configuration cleanly? If the answer is “kind of,” you need scope discipline before coding begins.
This gate is where hardcoding shortcuts become future migration taxes. I have watched teams pay that tax twice: once in rushed implementation, once in painful refactor during growth. A lightweight MVP threat modeling pass helps prevent that.
Gate 3: GTM gate (sales, SE, support can operationalize launch)
Even perfect SAML code fails commercially if GTM cannot sell and support it. You need objection-handling scripts, onboarding checklists, admin docs, and ownership for IdP setup calls. Otherwise, launch week becomes support roulette.
Open loop: Most teams pass two gates and still miss the quarter. Why? Because they forget the third gate and assume engineering completion equals market readiness.
- Revenue gate proves urgency.
- Product gate prevents brittle architecture.
- GTM gate converts capability into closed-won outcomes.
Apply in 60 seconds: Score each gate 0-2 today; do not greenlight if any gate is 0.
5) Build Scope Discipline: What “Minimum Viable SAML” Must Include
Must-have #1: SAML login + enforced SSO policy at workspace level
MVP means shippable trust, not partial auth theater. At minimum, admins need the ability to require SSO for workspace users, with safe rollout controls. If enforcement is impossible, procurement confidence remains fragile.
Must-have #2: JIT provisioning and clean user lifecycle handling
Just-in-time provisioning can cut onboarding friction and reduce manual account setup. But lifecycle handling matters just as much. What happens when an email changes? What about role shifts? Document these behaviors in plain language for sales and support teams.
Must-have #3: Admin UX for domain claim, cert rotation, test mode
Admins do not buy your internal architecture diagram. They buy confidence in operations. Domain claim workflows, certificate management, and explicit test mode reduce rollout fear. If these are hidden behind support tickets, adoption slows.
Must-have #4: Auditability for access and auth events
Enterprise buyers need visibility into who accessed what and when. Access event logs, auth success/failure visibility, and export-friendly formats all improve trust and incident response readiness.
Don’t overbuild yet: SCIM, advanced policy engines, custom mappings
SCIM is valuable, but not always day-one mandatory if SAML urgency is immediate and resources are constrained. Advanced policy engines can wait until buyer demand proves the need. Your goal is minimum viable enterprise confidence, not maximum theoretical flexibility.
Money Block: Eligibility Checklist (Yes/No)
- ☐ Can admins enforce SSO per workspace?
- ☐ Can customers test SSO without risking lockout?
- ☐ Do logs capture auth events in a supportable format?
- ☐ Does onboarding include clear IdP setup guidance?
- ☐ Is there explicit owner for enterprise identity support?
One-line next step: If 3 or fewer boxes are checked, pause launch and fix operational gaps first.
Neutral action: review this checklist in product + support + RevOps together.
Show me the nerdy details
Deeper technical notes, benchmarks, or methodology. For cert rotation, publish expected renewal behaviors and alert windows. For failure modes, define fallback login policies with explicit safeguards. For event logs, ensure consistent tenant identifiers and timestamps useful for incident timelines.
6) Packaging & Pricing: Don’t Let Monetization Undo the Win
Plan placement: Enterprise-only vs premium add-on tradeoffs
Pricing SAML too aggressively can create procurement fatigue. Pricing it too loosely can undercut enterprise positioning. The decision depends on segment mix, ACV strategy, and sales model maturity.
Enterprise-only packaging can simplify messaging if your target accounts already expect that structure. A premium add-on can work in transitional phases when mid-market buyers request SSO but cannot justify full enterprise bundles.
Pricing psychology: security as trust enabler, not penalty fee
Buyers accept paying for value. They resist feeling punished for baseline security hygiene. Frame SAML as part of enterprise trust operations, tied to onboarding reliability and governance support, not as a toll booth at contract stage.
I once watched a team win technical approval, then lose signature momentum because pricing language sounded like “extra fee to be safe.” Words matter when budgets are political.
Contract language that avoids backdoor custom commitments
Be explicit about what “SAML support” includes in standard scope. Otherwise, every new enterprise account can become a custom integration project hiding inside legal redlines. Pair this with clear boundaries in your security scope-of-work template so expectations stay sane.
Open loop: Could your pricing model be causing “security procurement fatigue”? If buyers keep asking for exception terms, your packaging message may be the friction source.
Money Block: Fee/Rate Table (Illustrative Positioning Framework)
| Year/Stage | Packaging Pattern | Range | Notes |
|---|---|---|---|
| Early enterprise motion | Premium add-on | Low to moderate uplift | Use when enterprise segment is emerging and price sensitivity is high. |
| Maturing enterprise motion | Enterprise tier inclusion | Bundled into higher ACV | Simplifies procurement and reduces custom terms. |
| Large strategic accounts | Included + enablement package | Contract-specific | Tie to onboarding scope and clear support boundaries. |
Neutral action: choose one default packaging rule and one exception rule, then train sales on both.
7) Common Mistakes That Make SAML Launch Backfire
Mistake #1: Building SAML without a security questionnaire playbook
Shipping code without response playbooks is like opening a theater with no box office. The show exists, but nobody gets in smoothly. Security teams ask predictable questions. Prepare concise, reusable answers and ownership paths.
Mistake #2: Shipping auth flow but ignoring break-glass admin access
Lockout scenarios happen. Break-glass mechanisms with strict controls and audit trails are part of responsible enterprise operation. Without them, support incidents escalate into trust incidents.
Mistake #3: No internal ownership for IdP onboarding support
Someone must own first 10 enterprise identity onboardings end-to-end. If ownership is fuzzy, customers become your process designers, and that is an expensive way to learn.
Mistake #4: Treating SAML as checkbox, not sales-stage accelerant
When SAML is framed as “we checked a compliance box,” teams miss its commercial value. Properly operationalized, it reduces late-stage friction and increases confidence in expansion paths.
Here’s what no one tells you… onboarding docs close deals too
Clear admin docs can move deals forward when engineering is already done but buyer anxiety remains. A two-page onboarding guide with screenshots has rescued more deals than some fancy roadmap slides I have seen.
- Prepare security-response templates before GA.
- Define break-glass policy and owner.
- Publish onboarding docs early, not after escalation.
Apply in 60 seconds: Assign a single DRI for the first 10 SAML onboardings.
8) Don’t Do This: 7 SAML Decisions You’ll Regret in 6 Months
Don’t hardcode tenant assumptions you can’t migrate later
Hardcoded shortcuts look efficient in sprint planning and painful in quarter planning. Design tenant boundaries with migration in mind from day one.
Don’t skip metadata/certificate rotation workflows
Rotation issues become emergency tickets at the worst times. Treat certificate lifecycle as a first-class operational path, not a hidden admin footnote.
Don’t ship without failure-mode UX and fallback login policy
Users need clear error messaging and safe fallback behaviors. Ambiguous login failures increase support load and reduce buyer confidence quickly.
Don’t let support discover edge cases before QA does
Pre-launch scenario testing across common IdPs prevents post-launch incident theater. Include expired certs, misconfigured attributes, and partial domain verification in test plans.
Three more regrets to avoid
- Do not promise custom mappings in contracts before product validates a repeatable model.
- Do not hide enterprise identity docs behind sales-only channels.
- Do not launch without internal escalation SLAs for auth-related incidents, alongside a realistic vulnerability remediation SLA.
Money Block: Quote-Prep List (Before Buyer Comparison)
Gather these before enterprise calls:
- Supported IdPs and tested configuration notes
- SSO enforcement options and admin controls
- Auth event logging capabilities
- Break-glass process summary
- Onboarding timeline expectations
Neutral action: keep this as a one-page internal artifact for sales + SE + support.
9) Who This Is For / Not For
This is for: Seed-to-Series C SaaS with emerging enterprise motion
If your pipeline includes IT-managed buyers, procurement workflows, and multi-team account expansion, this framework is for you.
This is for: Teams seeing repeated procurement or IT gate friction
If objections cluster around identity and access governance, SAML timing should be evaluated now, not after another slipped quarter.
Not for: PLG-only products with no admin/security requirements
If your buyers are individuals or tiny teams with low governance overhead, SAML can remain lower priority while you focus on PMF and retention mechanics.
Not for: Startups pre-PMF still searching for core retention
If core value is unstable, enterprise auth can become a costly distraction. Stabilize retention first, then introduce enterprise controls as demand becomes real.
Short Story: The Quarter We Misread “Interest” as Readiness (120–180 words)
A few years ago, I worked with a startup that had brilliant product adoption in small teams. Enterprise logos started showing up in demos, and everyone assumed we were “enterprise-ready.” We built slide decks, adjusted pricing, and celebrated pipeline growth. Then contracts slowed. Security questionnaires got longer. Champions sounded supportive but less decisive. In one painful month, three near-wins drifted into polite silence.
We blamed budget cycles, then seasonality, then almost anything except ourselves. Finally, we ran a stage-level audit. The pattern was painfully clear: identity governance concerns surfaced late, and we had no credible SSO path, no onboarding guide, and no owner for IdP setup. We were not losing on product value. We were losing on operational trust. Six weeks later, after a focused SAML MVP plus enablement docs, the same segment moved again. Not magically, but measurably.
10) Rollout Blueprint: 30-Day Plan to Turn SAML Into Closed-Won
Week 1: Pipeline audit + trigger confirmation
Pull recent enterprise opportunities and tag SSO/security friction points. Quantify stage delays where identity concerns appear. Confirm whether at least two revenue triggers are active.
Week 2: MVP scope lock + buyer requirement matrix
Define minimum viable SAML scope with clear “now vs later” boundaries. Build a requirement matrix for top buyer scenarios (Okta, Entra ID, Google Workspace common paths).
Week 3: Pilot with 2 design partners + objection handling scripts
Run controlled pilots with two customers willing to collaborate. Capture setup issues, docs gaps, and support friction. Turn findings into repeatable scripts for sales and SE.
Week 4: Enablement launch (sales, CS, support, docs, security FAQs)
Launch is not just feature availability. It is operational reliability. Enable sales decks, security response snippets, support macros, and concise admin documentation.
KPI board: cycle time, win rate, enterprise conversion, expansion speed
Track outcomes weekly for at least one full sales cycle. If cycle time shrinks and enterprise stage conversion improves, SAML is paying commercial rent. If not, inspect onboarding and pricing friction before blaming product. Also monitor adjacent controls such as API authentication and authorization maturity and startup secrets management hygiene.
Money Block: Coverage Tier Map (Tier 1 → 5)
- Tier 1: Basic SAML login only
- Tier 2: Workspace enforcement + test mode
- Tier 3: Lifecycle clarity + onboarding docs
- Tier 4: Operational logging + incident-ready support paths
- Tier 5: Advanced governance features (as demand proves)
Neutral action: decide your current tier and next-tier milestone before next sprint planning.
Infographic: From Friction Signals to Closed-Won
Security stalls, SSO objections, cycle stretch, expansion freeze, procurement drop-off.
Revenue proof, product readiness, GTM operational readiness.
Enforcement, lifecycle handling, admin UX, auditability.
Packaging that enables trust, avoids procurement fatigue.
Cycle time, win rate, enterprise conversion, expansion velocity.
FAQ
Is SAML SSO necessary before we have enterprise customers?
Not always. If you are pre-enterprise and not seeing governance-driven objections, SAML can wait. But if enterprise-qualified opportunities repeatedly stall on identity controls, delay becomes costly.
What ARR level usually justifies building SAML SSO?
There is no universal ARR threshold. A better trigger is friction density: frequency of SSO objections, stage-level delays, and expansion blockers. A single large strategic segment can justify earlier investment even at modest ARR.
How is SAML different from OAuth or “Sign in with Google”?
OAuth and social sign-in are useful for delegated access and user convenience. SAML is commonly used for enterprise identity federation and policy-driven organizational control. Procurement often evaluates these differently.
Should startups launch SAML or SCIM first?
If deals are blocked today on login and policy enforcement, SAML usually comes first. SCIM becomes higher priority when provisioning and deprovisioning automation requirements become frequent and explicit.
Can we charge extra for SAML without hurting close rates?
Yes, if pricing aligns with segment expectations and value communication is clear. The risk comes from framing security as a penalty, which can create negotiation drag and procurement fatigue.
How long does a practical MVP SAML implementation take?
Timeline varies by architecture and team capacity. Many startups can scope and deliver a practical MVP over several focused sprints if they keep scope disciplined and pair engineering with enablement work.
Which IdP should we support first for US B2B buyers?
Common priority order is usually Okta, Microsoft Entra ID, and Google Workspace due to broad enterprise adoption patterns and buyer familiarity.
What evidence should sales provide to prove SAML urgency?
Use stage-level CRM evidence: objection frequency, cycle delays tied to security review, procurement drop-off rate, and expansion freezes linked to identity requirements.
12) Next Step: One Concrete Action
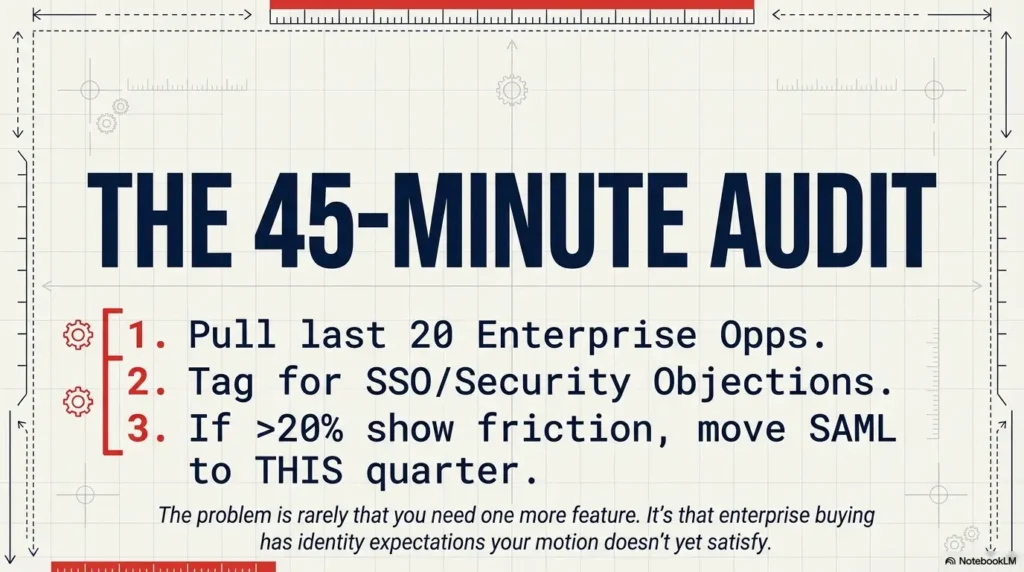
Run a 45-minute “SSO Revenue Friction Audit” this week
- Pull the last 20 enterprise opportunities.
- Tag each for SSO/security objection presence.
- Measure cycle delay and stage drop-off where SAML was missing.
- If 20%+ of late-stage opportunities show SSO friction, move SAML into current-quarter priority.
Here is the curiosity loop we opened at the top and now close plainly: the problem is rarely “we need one more feature.” The problem is that enterprise buying has identity expectations your current motion may not yet satisfy. When you see the pattern early, you protect ARR before pipeline optimism turns into forecast fiction.
Your next 15-minute move: schedule the audit, assign one owner, and make a go/no-go call using real stage data. No drama. Just decision clarity. For teams that need parallel hardening, map identity work with WAF vs RASP vs CSP tradeoffs for startups, and close obvious trust gaps with a quick security headers ROI pass.
Last reviewed: 2026-02.

