Beyond OSCP: Escaping the Certification Vacuum
Passing OSCP doesn’t create a plan—it creates a vacuum. That vacuum is where people burn six months stacking “same-same” badges that don’t change a single hiring outcome.
The pain is modern and specific: your calendar is chaos, recruiters want a clean role narrative, and your brain keeps defaulting to “harder must be better.” Meanwhile, your proof is scattered—no report you’re proud to show, no demo loop, no job-shaped story that survives an interview.
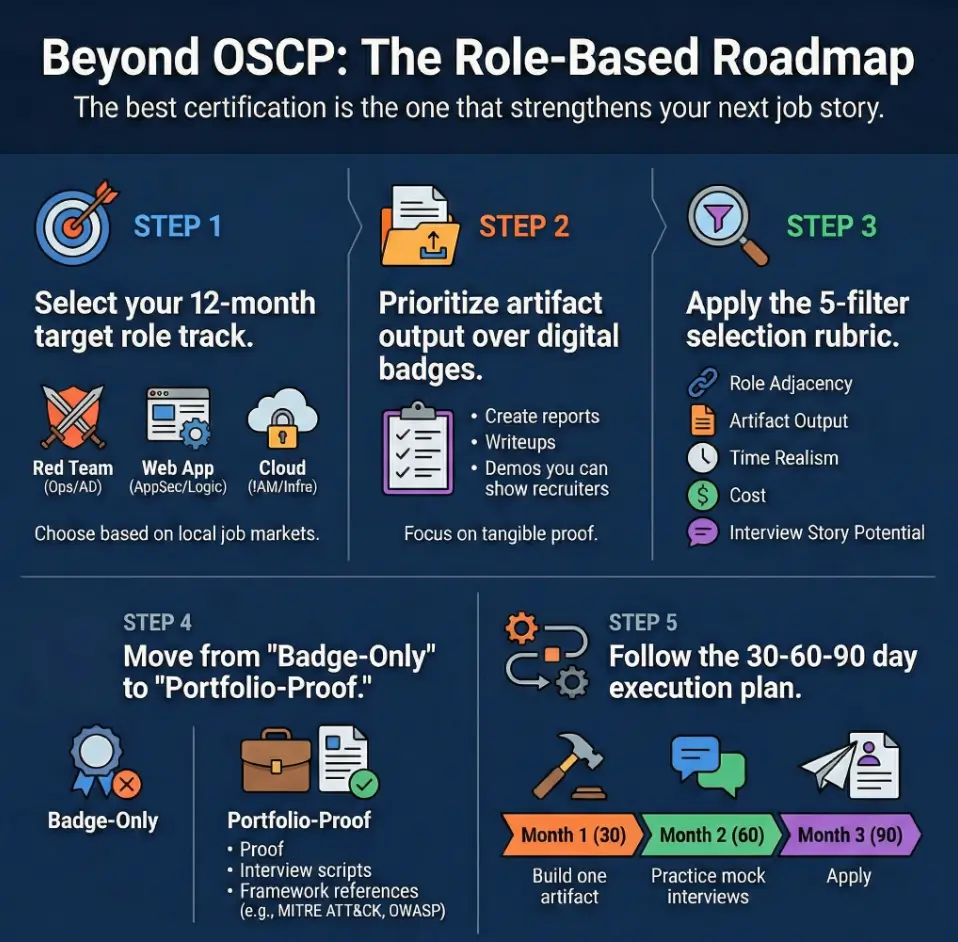
The Strategy: Pick one track (Red Team, Web App, or Cloud) and select an “artifact-forcing certification.” The real output isn’t the badge—it’s the work product you hand to a hiring manager: clean reports, reproducible writeups, and cloud lab stories.
Stop guessing. Build momentum. Apply like you mean it.
Table of Contents
Role first: The 3-track decision gate (Red Team / Web / Cloud)
Let’s make this painfully practical: the “right” certification after OSCP is the one that strengthens your next job story.
Not your identity. Not your ego. Your next job story.
Target role in 6–12 months: pick one sentence
Choose the sentence you want a recruiter to repeat back to you:
- Red Team / Adversary Emulation: “I can run disciplined operations and communicate risk like an operator.”
- Web App / AppSec: “I can break real software and write fixes like a teammate, not a drive-by.”
- Cloud Security: “I can reason about IAM, networking, logging, and real incident paths in modern infra.”
Evidence you can ship: demos, writeups, labs, or internal-style reports
If you can’t show it, it doesn’t exist—at least not to an ATS screen or a busy hiring manager.
A tiny confession from the trenches: the first time I helped a friend prep for interviews, their skills were fine, but the evidence was foggy. We fixed it by shipping one small, demo-ready artifact per week. The mood changed instantly.
If you want this to stay boring (meaning it works), treat evidence like a system: a repeatable schedule, tight note discipline, and clean capture hygiene—down to your screenshot naming pattern that keeps proof searchable under pressure.
Hiring signal strength: “recognizable badge” vs “portfolio proof”
Some orgs hire by badge. Some hire by proof. Most do a messy blend. Your move is to pick a cert that produces interview-transferable stories and leaves behind a portfolio you can point to without apologizing.
- Pick a role target (Red/Web/Cloud) for the next 6–12 months
- Choose a cert that outputs artifacts, not just a badge
- Build stories you can tell in interviews without rambling
Apply in 60 seconds: Write your one-sentence target role on a sticky note and keep it on your monitor for the next 7 days.
Show me the nerdy details
If you want a grounded way to label roles, the NIST NICE Framework is a common reference point for cybersecurity work roles and skills. It won’t pick your cert for you, but it helps you describe your target role in language hiring teams recognize. Use it to map your “next cert” to the tasks you actually want to do.
Fit check: Who this is for / not for
For: OSCP passers who want a job story, not another grind
If you’re time-poor and purchase-intent (same), you’re probably not looking for “a fun learning journey.” You want ROI. You want momentum. You want to stop being the person who’s always studying and never shipping.
For: people switching lanes (IT → security, blue → red, dev → appsec)
Lane switchers win when their proof looks like the job. One of the most common post-OSCP emotions is: “I can do a lot… but none of it looks like what they’re hiring for.” That’s fixable.
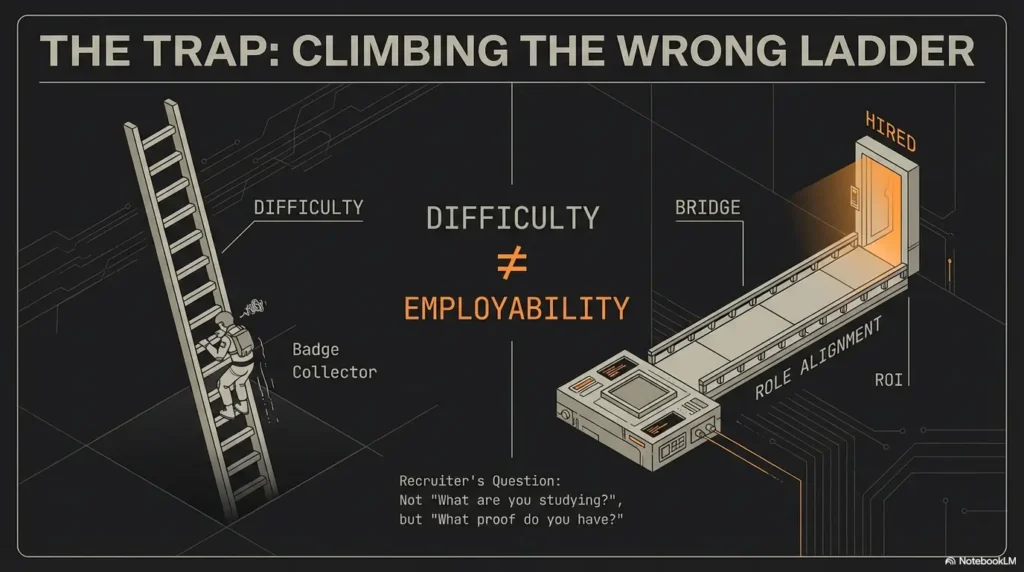
Not for: “collectors” chasing the hardest cert next without a role target
There’s a specific kind of burnout that comes from constantly climbing difficulty ladders. It feels productive. It’s also how people lose a year without getting hired.
Not for: anyone who hasn’t built a repeatable weekly practice system
If your plan is “study when motivated,” the next cert will eat you alive. You don’t need more motivation; you need a weekly system. Even 4–6 hours/week can move the needle if the outputs are right.
Mini anecdote: a friend once told me, “I’m going to do 20 hours every weekend.” Three weekends later: silence. We switched them to two 90-minute blocks during the week, one 2-hour block on Saturday, and suddenly the progress looked boring—meaning it worked.
If you need a realistic rhythm that doesn’t collapse in month two, borrowing a 2-hour-a-day routine you can actually sustain often beats “hero weekends” every time.
The hidden trap: Why “harder” isn’t always “better”
Curiosity gap: the question recruiters actually ask (and it’s not “what cert next?”)
Recruiters rarely lead with “What are you studying next?” They ask some version of:
“What kind of work do you want, and what have you done that proves it?”
Certs are shortcuts. But they only help when they align with that question.
Map your gap: skill depth vs surface breadth vs credibility signal
Post-OSCP, your gaps usually fall into one of three buckets:
- Depth gap: you need stronger expertise in a specific domain (AD ops, web logic, IAM).
- Breadth gap: you’re narrow; you need basic fluency across adjacent tasks (writing, scoping, detection thinking).
- Signal gap: you have skills, but hiring screens can’t see them fast enough.
Choose your bottleneck: interviews, on-the-job tasks, or passing screens
Your next certification after OSCP should attack your bottleneck.
If you’re failing screens, pick a credential that’s recognizable in job postings.
If you’re failing interviews, pick a track that generates stories.
If you’re failing on-the-job tasks (practicals, take-homes), choose the cert that forces realistic outputs.
One more lived-feeling moment: picture your next interview. You’re asked, “Tell me about a time you found a security issue and drove it to remediation.” If your brain immediately tries to translate OSCP lab memories into a business story… that’s your signal to choose a certification that forces engagement narrative and reporting—and to stop bleeding time into rabbit holes you can’t justify afterward.
- Yes/No: I can commit to a repeatable weekly schedule (minimum 4 hours/week) for 8–12 weeks.
- Yes/No: I have a clear target role sentence (Red/Web/Cloud) written down.
- Yes/No: I can publish or privately package 3 artifacts (writeups, reports, demos) during the run.
- Yes/No: I’ve read at least 20 job postings and tagged required skills.
Red Team track: Build operator credibility (without becoming a cert hoarder)
Choose your lane: internal pentest, external consultancy, or purple-team path
Red Team isn’t a single job. It’s a cluster of jobs with different constraints:
- Internal: you learn the environment deeply, work with defenders, and ship improvements.
- Consultancy: you deliver fast, scoped results under time pressure and report like a pro.
- Purple-team: you bridge offense and defense, and your value is communication and detection impact.
Skills that compound: AD tradecraft, OPSEC habits, reporting under constraints
OSCP taught you persistence. Red Team hiring often wants something extra: discipline.
Not “I can pop boxes.” More like: “I can plan, execute, and communicate under rules.”
Curiosity gap: what your OSCP didn’t force you to learn (but jobs will)
OSCP rarely forces deep engagement structure. Real work does:
- Scoping and “what’s in / out” boundaries
- Evidence handling and clean note discipline
- Risk communication that non-security people actually understand
Micro (pattern interrupt): Let’s be honest—“I can pop boxes” isn’t a role
It’s a skill. A good one. But roles are stories—beginning, middle, end.
Your post-OSCP certification should help you translate wins into: scoping → access → impact → remediation.
If your “Red Team” instincts keep snapping back to Windows fundamentals (good), build a small set of repeatable privesc narratives you can explain cleanly—like how you validate unquoted service path risk on Windows or when sudo NOPASSWD privileges become an escalation story that an interviewer actually remembers.
- Pick the lane (internal, consultancy, purple-team) before picking a cert
- Practice writing findings like the client will act on them tomorrow
- Build one “engagement-style” report that reads like real work
Apply in 60 seconds: Draft a 6-line engagement summary: goal, scope, method, key access path, business impact, remediation theme.
Short personal-feeling snapshot: I once watched someone answer an interview question by listing tools for two minutes straight. The interviewer’s eyes glazed over. Then they tried again: “I validated access, confirmed blast radius, and documented remediation steps.” Same person—completely different signal.
If Active Directory is your lane, make it job-shaped (not tool-shaped): practice AD enumeration without BloodHound when you’re constrained, and pair it with a clear explanation of why that constraint matters in real engagements.
Web App track: Prove you can break real software (and explain it)
Decide your audience: appsec teams vs product eng vs bug bounty-style work
Web security splits quickly by audience:
- AppSec teams: love clean repro steps, impact, and mitigation guidance.
- Product engineering: wants fixes that fit their code and release constraints.
- Bounty-style: values creativity, chaining, and high-signal writeups.
What changes vs OSCP: threat modeling, auth logic, chained vulns, clean writeups
OSCP is often infrastructure-flavored. Web App work is logic-flavored.
You’re thinking about sessions, authorization boundaries, data flows, and how a “harmless” endpoint becomes dangerous after one weird sequence.
Portfolio proof: 3 writeups that read like internal security tickets
If you want to stand out, write like you’re on the team. Your writeup should include:
- Impact in plain English (what could happen, who is affected, why it matters)
- Reproduction steps (minimal, deterministic)
- Fix guidance (practical, not theoretical)
If you want a clean “web artifact” that reads like real work, start with one focused pattern and ship it: for example, a report built around file upload bypass checks that prevent classic foot-guns, then tighten your discovery pipeline using FFUF wordlist tuning that improves signal-to-noise.
Micro (pattern interrupt): Here’s what no one tells you—web certs reward writing
Yes, you need technical skill. But the hiring edge comes from communicating like a teammate.
Your report quality can beat raw exploit speed more often than you think.
- 3 target job postings (AppSec, Security Engineer, Product Security)
- One app you can legally test (intentionally vulnerable app, CTF platform, or your own demo app)
- A writeup template (impact, repro, root cause, fix, verification)
- A weekly publishing plan (private PDF report is fine if you can’t publish publicly)
Another tiny anecdote that might feel familiar: the first time you write a web finding cleanly, you’ll notice something weird—your own understanding sharpens. It’s like explaining a chord progression to someone else: suddenly you can hear what you were missing.
And if your workflow relies on proxy tooling, set it up like an adult so your artifacts don’t collapse mid-demo—this includes a stable Burp external browser setup in Kali and a habit of checking for environment issues before blaming your brain.
Cloud track: Become “useful on day one” in modern infra
Pick a cloud reality: AWS/Azure/GCP (don’t multi-cloud too early)
Cloud security looks impressive when it’s specific. “Cloud” as a vague blob is not a hiring signal.
Pick the platform that matches your local job market and your target roles. Then go deep enough to be useful.
What hiring teams want: IAM reasoning, network segmentation, logging, incident paths
Cloud hiring often tests reasoning, not memorization:
- IAM: “Who can do what, from where, and why is that dangerous?”
- Networking: “What can talk to what—and what should never talk to what?”
- Logging: “If this goes wrong, how would we know, and what would we do?”
If “logging” is still a fuzzy word for you, make it concrete by practicing lab logging that turns chaos into a readable timeline—because cloud interviews often reward people who can narrate “what would we see?” as easily as “what would we do?”
Portfolio proof: one end-to-end lab—misconfig → exploit → detection → fix
If you do only one portfolio project after OSCP, do this: build a small cloud lab that tells a complete story.
Not just “I got access.” The whole arc: misconfiguration, exploitation, detection signal, and remediation steps.
In the real world, defenders love people who think in loops.
Show me the nerdy details
For cloud roles, a helpful mental model is to map your actions to a common technique taxonomy. MITRE ATT&CK is widely used to describe adversary behaviors and can help you explain your work clearly across teams. Even if you’re not “doing red team,” using shared language reduces confusion in interviews and incident reviews.
Personal-feeling snapshot: I’ve seen candidates lose cloud interviews because they could describe exploits but couldn’t answer, “What log would show this?” The winning candidates don’t know everything—they know what to check first.
Cert selection rubric: The 5 filters that prevent regret
This is the part that saves you money and prevents “six months later, still no interviews.”
Use these five filters like a gate. If a certification fails two of them, it’s probably not your next move.
Filter 1: Role adjacency (does it match job postings you’ll apply to?)
Read 20 postings. Literally. Tag them Red/Web/Cloud. If you can’t find the cert’s keywords in real postings, you’re buying vibes.
Filter 2: Artifact output (what will you show after you pass?)
After passing, what exists in the world? A report PDF? A writeup series? A demo video? A detection walkthrough?
If the answer is “a badge,” slow down.
A high-signal starting point is to adopt a professional format early—e.g., a pentest report template you can reuse so every new lab becomes a portfolio asset instead of a pile of notes.
Filter 3: Timebox realism (8–12 weeks vs 3–6 months)
Be honest about your life. If your calendar is chaos, choose a shorter timebox and stack artifacts instead of suffering in silence for half a year.
Filter 4: Cost + retake risk (budget like an adult)
You’re allowed to want premium training. You’re also allowed to protect your budget.
Plan for the possibility of a retake without spiraling.
Filter 5: Interview transfer (does it create stories you can tell?)
A great certification after OSCP gives you repeatable stories:
- “Here’s how I approached the problem under constraints.”
- “Here’s what I did when I got stuck.”
- “Here’s how I communicated impact and remediation.”
- If postings don’t mention it, treat it as optional
- If it doesn’t produce proof, it won’t move hiring outcomes
- If it doesn’t create stories, interviews will feel shaky
Apply in 60 seconds: Pick one certification and write 3 artifacts it will force you to create—if you can’t name them, reconsider.
Common mistakes: The two ways people waste the post-OSCP year
Mistake #1: “Same-same” stacking (another pentest badge, same narrative)
If your last cert proved “I can exploit,” and your next cert proves… “I can exploit,” you might not be changing the hiring outcome. You’re just deepening one signal. That can work—but only if your target job wants that exact depth.
Mistake #2: Tool obsession without fundamentals (shiny > signal)
Tools change. Mental models compound.
Hiring teams notice when someone can reason about permissions, boundaries, and detection paths—even if they don’t know the latest tool name.
Mistake #3: No artifacts (you pass… and still can’t show work)
The painful version is: you pass the next cert, you update LinkedIn, and interviews still don’t appear.
Not because you’re bad—because the proof isn’t visible enough.
This is where process beats inspiration: a consistent proof screenshot workflow that captures what matters turns “I did a thing” into “I can show a thing.”
Mistake #4: Learning in public with zero structure (burnout in 6 weeks)
Public learning can be great. But if you’re posting every day and not shipping coherent artifacts, you’re performing progress instead of building it.
- Don’t collect badges that don’t change your narrative
- Ship artifacts weekly, even small ones
- Structure beats motivation in month two
Apply in 60 seconds: Write your next 3 artifacts on paper and schedule the first one this week.
Short Story: The week after one OSCP pass, a candidate felt “behind” because others were already studying for the next hard thing. They picked a new certification immediately and disappeared for two months. When they returned, they had knowledge—but no proof. We rewound the plan: one track, one cert, three artifacts.
In week one, they wrote a clean internal-style report for a small lab scenario. In week two, they made a 5-minute demo walkthrough. In week three, they turned the same work into an interview script. The funny part? Their confidence didn’t come from learning more. It came from finally having something to show—something that looked like the job.
Don’t do this: The “next cert” anti-patterns (and what to do instead)
Anti-pattern: choosing by difficulty flex
Difficulty is not ROI. Difficulty is just difficulty.
Choose by job alignment and artifact output. Your future self will thank you.
Anti-pattern: picking a cert before reading 20 job postings
This is the most common mistake among smart people. They “choose first,” then try to justify later.
Flip it: read postings, pick a track, then pick a cert.
Anti-pattern: ignoring writing (reports are the job)
Even in offensive roles, the report is often what gets acted on. If you can’t communicate clearly, your technical work doesn’t land.
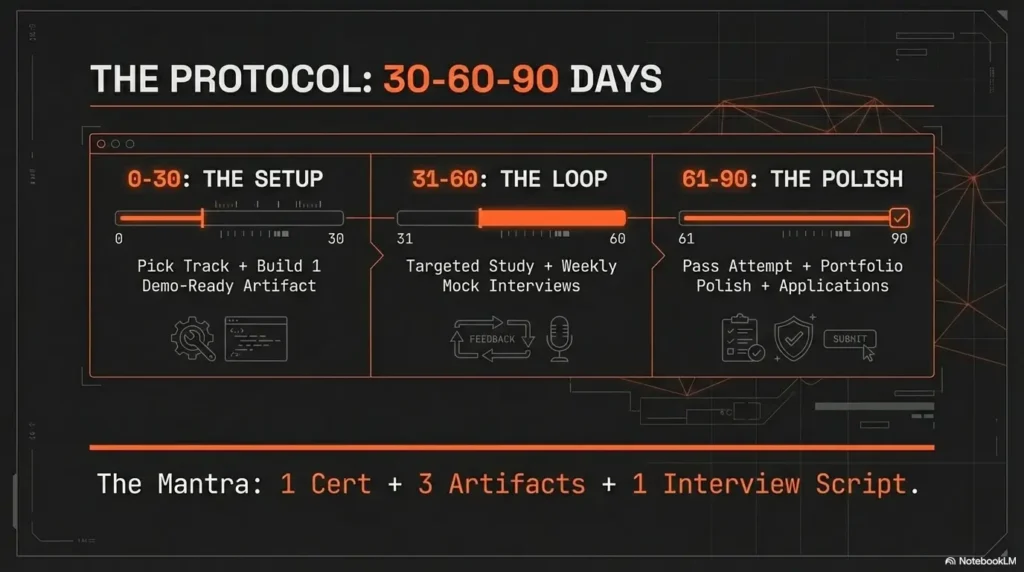
Replacement plan: 1 cert + 3 artifacts + 1 interview script
This is your clean replacement:
- 1 certification after OSCP that matches your role target
- 3 artifacts that prove you can do job-shaped work
- 1 interview script built from those artifacts (STAR format, short and specific)
Show me the nerdy details
If you want a “shared language” for how attacks and defenses map, OWASP Top 10 is often used for web risk conversations, while ATT&CK is commonly used for adversary behaviors. Using common frameworks doesn’t replace skill—it makes your explanations faster and more credible during interviews and cross-team work.
Timeline plan: 30–60–90 days with checkpoints (not vibes)
Days 1–30: pick track + build one “demo-ready” artifact
In the first 30 days, don’t try to “finish the cert.”
Try to finish one artifact that could survive scrutiny: a clean report, a reproducible web writeup, or a cloud lab walkthrough.
A tiny memory-rich moment: treat this like cleaning your workspace after a concert—packing cables neatly so the next show doesn’t start in chaos. Your first artifact is the cable wrap.
If your biggest risk is “I’ll drift,” anchor the month with a schedule you can repeat: borrow an OSCP-style time management plan you can adapt post-pass, and keep the scope tight enough that the artifact ships.
Days 31–60: targeted study + weekly mock interview loop
This is where most people drift. Prevent it by adding a weekly loop:
- One 20-minute mock interview (record yourself if needed)
- One artifact update (tighten clarity, improve visuals, fix wording)
- One “story” practice: how you approached, what you learned, what you’d do next
Days 61–90: pass attempt window + portfolio polish + applications
Now you apply pressure: attempt window, polish, apply.
Your goal isn’t “perfect portfolio.” Your goal is “good enough proof plus a coherent story.”
And yes—applications can run in parallel. You don’t need to wait until you feel worthy.
Next step: One concrete action (do this today)
Open 20 US job postings → tag them Red/Web/Cloud → copy required skills into a one-page gap list
Do it today. Not because it’s fun—because it removes uncertainty.
Tag postings. Copy skill requirements. Then circle the missing ones that also match your interest.
That one-page list becomes your entire plan.
Pick one track and one cert that forces the missing artifacts you don’t have yet
If you feel torn, pick the track that creates the clearest artifacts fastest. Momentum is a feature.
You can change lanes later. Right now, you need one story that’s believable.
- Tag 20 postings by track (Red/Web/Cloud)
- Extract a one-page gap list
- Select a cert that forces the missing proof
Apply in 60 seconds: Save three postings and highlight the top five recurring requirements.
FAQ
Is OSCP enough to get a pentesting job in the US?
Sometimes, yes—but it depends on your market and how you package proof. OSCP can open doors, but hiring often still wants role-shaped artifacts: clean reports, realistic demos, and a coherent narrative of how you work under constraints.
What certification should I take after OSCP for red teaming?
Choose the certification after OSCP that forces Red-Team-shaped outputs: engagement narrative, disciplined ops, and reporting. If your current bottleneck is “I can’t explain impact,” prioritize the option that makes you write and communicate clearly.
Should I do OSWE after OSCP if I want appsec?
If your target role is AppSec, OSWE-style preparation can be strong—especially if you convert study into 2–3 internal-style writeups. The key is not the badge alone; it’s proving you can break real software and explain fixes like a teammate.
Do cloud certifications help if I’m aiming for cloud security roles?
They can—if they match the cloud platform your target jobs use and you pair them with one end-to-end lab (misconfig → exploit → detection → fix). Cloud hiring often tests reasoning about IAM, segmentation, and logging more than tool memorization.
PNPT vs eCPPT vs another OffSec cert—what’s the difference for hiring?
Hiring impact varies by employer. Instead of debating brands endlessly, run the five filters: job-posting relevance, artifact output, timebox realism, cost/retake risk, and interview transfer. Pick the option that best strengthens your specific job narrative.
How long should I wait after passing OSCP before starting the next cert?
If you still have momentum, start within 1–2 weeks—but start with one artifact first. A quick “demo-ready” output prevents drift and keeps you from choosing the next certification after OSCP out of pure anxiety.
Do employers care more about certs or GitHub/writeups?
Many care about both, but writeups often win once you’re past the initial screen. A recognizable cert can get you noticed; strong artifacts can get you hired. Aim for “badge + proof,” not “badge only.”
Conclusion
Remember the hook: “what cert next?” isn’t the real question. The real question is:
What role do you want in 6–12 months, and what proof will make that believable?
That’s the loop. Closed.
If you do one thing in the next 15 minutes: open 20 job postings, tag them Red/Web/Cloud, and write your one-page gap list.
Then pick one certification after OSCP that forces the missing artifacts—because proof beats intention.
Last reviewed: 2026-01-26

