
Security Headers: A Revenue Conversation, Not a Compliance Checkbox
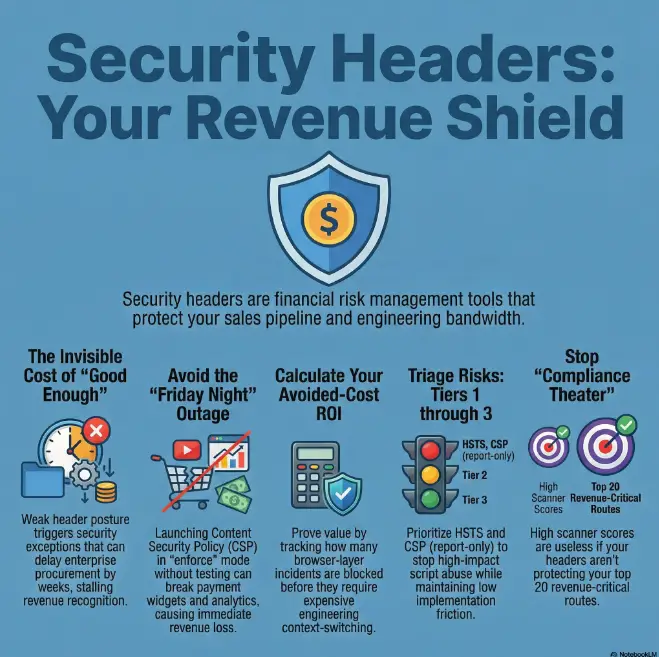
A security incident does not need to be catastrophic to be expensive. Sometimes it is just a quiet browser-layer failure that bleeds support hours, slows enterprise deals, and dents conversion where trust matters most.
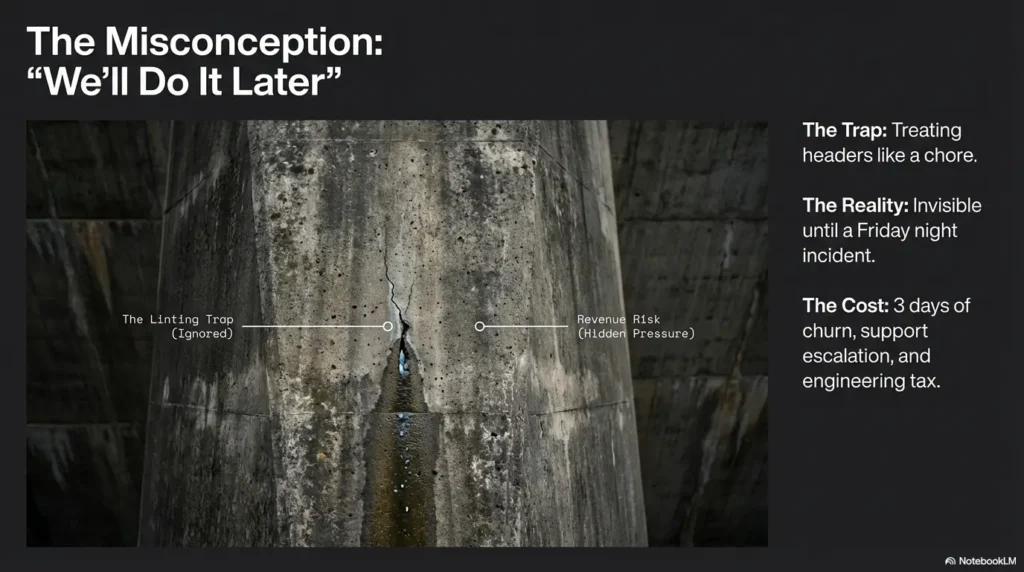
Most teams still treat headers as “we will fix it later” hardening. Meanwhile, script drift, weak framing controls, and inconsistent edge policies create hidden operational drag.
You feel it as procurement exceptions, noisy incident reviews, and Friday-night firefighting that never makes a headline but always shows up in cost.
“Keep postponing, and the bill compounds in churn risk, delayed recognition, and engineering context switching.”
What’s Inside the Guide:
- ✔ 30-60-90 rollout plan for HSTS, CSP, and frame protections.
- ✔ Triage matrix to prioritize by business impact.
- ✔ Lightweight ROI modeling tied to support and incident data.
Table of Contents
1) ROI First: Why security headers belong in your revenue conversation
The hidden P&L line item: preventable browser-layer incidents
Security headers are cheap controls at the edge of user trust. They don’t replace auth hardening, detection engineering, or secure SDLC. But they do remove entire classes of browser abuse before abuse becomes a ticket queue, a fraud write-off, or a “why did checkout break?” incident review. If your team is building out founder-level reporting, this maps neatly to a practical security metrics framework for founders that tracks incident cost instead of vanity scores.
I’ve seen this pattern in lean teams: someone says “we’ll do CSP later,” then a third-party script issue triggers account session weirdness on Friday night. No blockbuster breach, just three days of churn risk, support escalation, and engineering context-switch tax. It rarely headlines. It always invoices.
What “good enough security” costs when a deal is on the line
Enterprise buyers do not reward perfect architecture documents. They reward confidence that you won’t become their next incident dependency. A weak header posture often turns into “security exception requested,” then “follow-up questionnaire,” then two extra procurement weeks. That delay has a cost: slower revenue recognition and more sales engineer hours burned in repetitive clarifications. Teams that prepare answers in advance usually move faster through a vendor security questionnaire process.
Let’s be honest… breaches rarely start where dashboards are brightest
Most teams monitor backend API errors beautifully and under-instrument browser trust boundaries. Headers close that gap. If your app has login, billing, admin, or embedded third-party scripts, headers are not cosmetic, they’re controls with measurable downside reduction.
- They cut exploitable browser pathways.
- They reduce support, fraud, and incident overhead.
- They speed security reviews when buyers ask hard questions.
Apply in 60 seconds: Rename your internal task from “Header cleanup” to “Revenue-surface hardening” and watch prioritization improve.
2) Header Triage Matrix: Which headers to implement first (and why)
Priority Tier 1 (immediate): HSTS, CSP (report-only), X-Content-Type-Options
If engineering time is constrained, start where risk reduction is strong and breakage is manageable. The same triage thinking appears in MVP threat modeling for startups: prioritize controls by attack surface and business blast radius first, elegance second.
- HSTS: Forces HTTPS usage after first trusted visit. High upside, medium operational caution.
- CSP (report-only first): High upside, high operational load, but safe to begin in observation mode.
- X-Content-Type-Options: nosniff: Small change, usually low friction, practical hardening against content-type confusion.
Priority Tier 2 (next sprint): frame protections, Referrer-Policy, Permissions-Policy
These controls tighten embedded behavior, referrer leakage, and unnecessary browser feature exposure. They’re especially useful on auth, payments, account settings, and admin surfaces.
Priority Tier 3 (contextual): COOP/COEP/CORP for high-risk app surfaces
Cross-origin isolation headers can be decisive for specific app architectures (sensitive workflows, advanced browser capabilities, strict isolation needs). They also bring compatibility decisions. Use them where threat model and product architecture justify the trade.
Decision lens: exploit probability × business impact × implementation cost
Use one matrix for security and finance alignment:
| Header / Control | Exploit Probability | Business Impact if Missing | Implementation Friction | Recommended Phase |
|---|---|---|---|---|
| HSTS | Medium | High on trust and transport safety | Medium | Tier 1 |
| CSP (report-only to enforce) | High | Very high on script abuse prevention | High | Tier 1 start / Tier 2 enforce |
| X-Content-Type-Options | Medium | Medium-high for file/script routes | Low | Tier 1 |
| Frame protections | Medium | High on auth/payment/admin flows | Low-medium | Tier 2 |
Neutral action: Score each revenue-critical route in this matrix before assigning sprint points.
3) CSP Economics: The highest upside with the highest operational drag
Why CSP is powerful but expensive to do badly
CSP is where teams either level up or accidentally break production. Strong CSP can dramatically reduce script injection blast radius. Bad CSP rollout can quietly block conversion scripts, payment widgets, analytics tags, and customer support embeds. Translation: security win on paper, revenue bruise in reality.
My own “learned it the hard way” moment came from a launch where we locked down scripts before a complete asset inventory. We didn’t get breached. We just confused attribution, triggered false alarms, and spent 11 hours untangling exceptions. Useful lesson, expensive tuition.
Start with report-only to avoid breaking revenue-critical flows
Report-only mode buys you visibility without immediate user impact. It lets you map what is actually loading, where, and why. This is where disciplined teams outperform: they turn logs into ownership, not into dashboard noise.
Eligibility checklist: Is your team ready for CSP enforcement?
- Do you have a route inventory for login, checkout, billing, admin, and embed-heavy pages? Yes/No
- Can you attribute third-party scripts to an owner? Yes/No
- Do you have rollback authority defined for on-call? Yes/No
- Can you separate noisy violations from exploitable patterns? Yes/No
Neutral action: If any answer is “No,” stay in report-only and close that gap first.
Converting noisy violation logs into deployment-ready policy changes
Think in batches: high-frequency benign first, high-risk unknown next. Don’t chase every violation in week one. Cluster by route and script owner. Enforce policy by route cohort, not globally in one dramatic Friday cutover.
Here’s what no one tells you… CSP ROI depends on inventory discipline, not syntax tricks
Nonce strategies and directive tuning matter. But ownership discipline matters more. Teams that maintain script intake policies usually cut exception churn fast. Teams that don’t keep paying “security interest” every sprint. If script sprawl is already becoming a cloud-side governance issue, align this with your cloud misconfiguration prevention workflow.
Show me the nerdy details
For practical CSP progression: begin with script-src and object-src controls in report-only, collect route-tagged reports, classify by first-party/third-party, then graduate high-confidence routes to enforce mode with canary cohorts. Methodology beats “perfect policy” ambition.
4) HSTS and TLS Confidence: The low-drama, high-certainty win
Preload vs non-preload: when “strict” helps and when it hurts
HSTS often delivers one of the cleanest risk-reduction curves when rolled out carefully. Non-preload gives you operational flexibility while you validate subdomain readiness. Preload is stronger but far less forgiving. If legacy subdomains exist, preload can convert hidden debt into visible outages fast.
Subdomain implications that can break legacy services
If you use includeSubDomains without full inventory, you may lock down legacy properties still expecting mixed assumptions. The fix is boring and effective: discover all active hostnames, verify certificate coverage, and phase max-age upward over time.
Measuring trust impact: checkout confidence, enterprise questionnaire pass rate
HSTS won’t magically increase conversion by itself. But it supports cleaner “secure-by-default” posture, fewer transport trust exceptions, and better answers in security reviews. In B2B cycles, that matters. In consumer flows, confidence frictions compound.
- Start scoped and increase strictness in phases.
- Inventory hostnames before strict includeSubDomains decisions.
- Treat preload as a commitment, not a checkbox.
Apply in 60 seconds: Ask your infra owner for a current hostname inventory before changing HSTS scope.
5) Clickjacking and MIME Sniffing: Small headers, big incident prevention
X-Frame-Options / frame-ancestors for payment and admin surfaces
Clickjacking protections are frequently underappreciated because their implementation looks small. That’s exactly why they’re high-ROI in lean teams. For critical UI surfaces, reducing framing abuse risk is the kind of move that prevents strange downstream incidents nobody wants to explain to customers.
X-Content-Type-Options to stop content-type confusion attacks
nosniff can be one of the fastest risk reducers you’ll ever deploy. It won’t solve every script risk, but it tightens behavior in ways that pay back quickly, especially on mixed-content delivery paths and legacy file routes.
Why these two often pay back fastest in lean teams
They’re straightforward, auditable, and usually easy to test. In one small product org I worked with, these controls plus route-level header consistency checks were implemented in under a sprint and removed recurring scanner noise that had been burning ops time for months.
Decision card: When A vs B
When A (fast baseline): Use frame protections on auth, billing, admin, and account settings routes immediately.
When B (broader control): Extend and centralize policy once route ownership and exceptions are documented.
Time/cost trade-off: A takes hours to days; B takes days to weeks but scales cleaner.
Neutral action: Start with A on revenue-critical routes this week, then plan B in the next sprint.
6) Mistakes That Burn Budget: Don’t ship headers like a compliance theater project
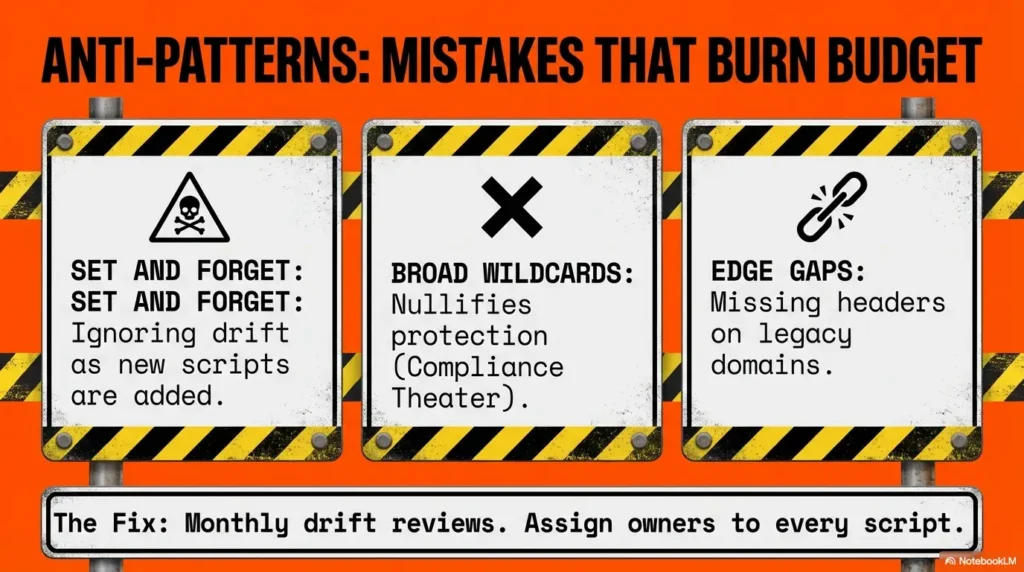
Copy-pasting “secure defaults” without app-specific testing
Generic policies are useful as a starting map, not a destination. Your script graph, partner embeds, CDN routes, and legacy pages are unique. A pasted policy can pass a scanner while quietly breaking a critical customer journey.
Shipping CSP in enforce mode on Friday
If you want one simple rule: avoid irreversible rollouts before low-coverage support windows. Roll security like product: canary, monitor, rollback, repeat. Incident fatigue is expensive, and “we’ll just watch it” is not a plan.
Ignoring third-party scripts that quietly violate policy
The third-party ecosystem shifts under your feet. Tag managers, analytics tools, chat widgets, and A/B testing platforms can drift over time. If intake ownership is vague, your CSP debt grows invisibly. A lightweight startup secrets management policy and script ownership register can prevent this drift from becoming production debt.
Treating scanner scores as business outcomes
Scanner scores are proxies. Useful, but incomplete. If scores rise while fraud, support escalations, or change-failure rate worsen, you’re polishing optics and missing outcomes. Operational rigor is much clearer when paired with defined vulnerability remediation SLA targets.
- Test controls on real revenue routes.
- Use canary + rollback guardrails.
- Measure business outcomes, not only scanner optics.
Apply in 60 seconds: Add “business impact if broken” as a required field in header change tickets.
7) Who this is for / not for
Best fit: SaaS products, fintech-adjacent apps, marketplaces, B2B platforms
If users authenticate, pay, administer settings, or integrate third-party scripts, this framework fits. It’s especially useful where customer trust and procurement scrutiny directly affect pipeline speed.
Not a fit (yet): static brochure sites with no auth, no PII, and no dynamic scripts
You still want sane defaults, but the full ROI framework may be overkill if your threat surface is truly minimal. Keep baseline hygiene, avoid unnecessary complexity, and reassess as soon as your app gains login or payment pathways.
If you’re pre-PMF: minimum viable baseline vs enterprise-grade posture
Pre-PMF teams should avoid gold plating. The winning move is a minimum viable baseline now, plus a deliberate path to stricter posture once product-market traction stabilizes. Security maturity should climb with business exposure. If you need to keep planning realistic, tie controls to a SOC 2 budget calculator style roadmap before promising enterprise-grade timelines.
Coverage tier map: what changes from Tier 1 → Tier 5
- Tier 1: Basic header presence on primary web routes.
- Tier 2: Route-specific policies for auth, billing, admin.
- Tier 3: CSP report-only with owned triage process.
- Tier 4: Progressive CSP enforcement + exception governance.
- Tier 5: Continuous drift review, procurement-ready evidence, ownership SLAs.
Neutral action: Mark your current tier today and define one-tier-up criteria.
8) Measurement Stack: How to prove header ROI to engineering and finance
Leading indicators: blocked exploit classes, CSP violations reduced, insecure request drops
Leading indicators tell you whether controls are tightening. They are not victory laps, they are steering signals. Focus on trend direction by route class and risk criticality, not vanity totals.
Lagging indicators: incident frequency, MTTR, fraud/abuse losses, support escalations
Lagging indicators are where finance listens. If incidents become less frequent, shorter, and less costly, your header program is doing real work. Tie these to error budgets and support workload to show operational leverage.
Revenue proxies: conversion trust signals, procurement velocity, reduced security exceptions
You may not get a perfect “header-to-revenue” equation. You can still prove value through proxies: fewer security exceptions in deal cycles, faster questionnaire closure, fewer trust blockers in procurement, and less conversion disruption during change windows.
Dashboard blueprint: security metric → business metric → executive narrative
Use a one-line chain for every major control: “What changed technically, what changed operationally, what changed commercially.” This keeps engineering, product, and finance in one conversation. For teams that need a starter template, adapt the narrative style used in security metric dashboards for founders.
Mini calculator (quick estimate)
Inputs (max 3): (1) incidents/quarter linked to browser-layer weakness, (2) average internal cost per incident, (3) expected reduction rate after rollout.
Output: Estimated quarterly savings = incidents × cost × reduction rate.
Example: 6 × $18,000 × 0.30 = $32,400 estimated quarterly avoided cost.
Neutral action: Run this estimate before budget planning and revisit after 90 days.
Show me the nerdy details
For stable trend quality, segment telemetry by route category (auth, checkout, admin, static), environment (staging vs production), and release cohort (canary vs full). Aggregate weekly, review monthly with security and product ops together.
9) Rollout Playbook: 30-60-90 day sequence that avoids outages
Days 1–30: asset inventory, report-only policies, staging simulations
Map revenue-critical URLs first: login, checkout, subscription management, admin, and top referral landing pages. Turn on report-only CSP where applicable. Validate HSTS scope in staging. Establish ownership for third-party scripts by team, not by hope.
Days 31–60: progressive enforcement by route, canary cohorts, rollback guardrails
Pick one route cluster with predictable behavior and enforce there first. Canary to a small cohort, monitor conversion and error deltas, then expand. Treat rollback as a designed feature, not a panic response. This is the same discipline teams use when they follow a practical security scope-of-work template and predefine rollback ownership.
Days 61–90: tighten directives, prune exceptions, formalize ownership
Now you remove lazy wildcards, document exceptions, and define review cadence. This is where programs either mature or drift. If no owner is assigned, drift always wins.
Change management: who approves, who monitors, who can rollback
Define three roles clearly: approver, monitor, rollback authority. Ambiguity here is the quiet root cause of long incident nights. I once joined a war room where five teams assumed another team owned rollback. Nobody did. That memory still pays dividends in process design.
Infographic: 30-60-90 Header ROI Roadmap
Days 1–30
- Inventory top 20 revenue routes
- CSP report-only + triage board
- HSTS scope validation
Outcome: Visibility without disruption
Days 31–60
- Route-level enforcement canaries
- Monitor conversion + incident deltas
- Rollback runbook tested
Outcome: Controlled risk reduction
Days 61–90
- Tighten policies, prune wildcards
- Formalize script intake ownership
- Executive ROI narrative monthly
Outcome: Durable governance + faster deals
10) Common mistakes (the repeat offenders)
“Set and forget” headers with no policy drift review
Headers are living controls because your application is a living system. New routes, new tags, new partners, new experiments, drift is guaranteed. Review cadence is not bureaucracy, it’s maintenance.
Broad wildcards in CSP that nullify protection
When policies become too permissive, you keep operational burden and lose protective value. That’s the worst trade in the room. Better to enforce narrowly where confidence is high, then expand with intention.
Missing headers on edge routes (CDN, API gateway, legacy domains)
Coverage gaps on edge paths are extremely common. A single ungoverned legacy domain can undercut your “secure-by-default” claim during reviews.
No ownership model for third-party script intake
If nobody owns intake, everyone owns incident clean-up. Require owner, purpose, retention, and rollback plan before any new script is admitted. Teams already formalizing incident terms in legal docs often extend that clarity into controls using a clear limitation-of-liability framework for security work.
Short Story: The expensive “almost secure” launch
A mid-size B2B platform I advised had decent scanner scores and a proud dashboard. During a product growth push, marketing added two new third-party scripts and a support widget across key onboarding routes. No intake gate, no ownership, no rollback owner. Two weeks later, CSP went partially enforce mode with a broad wildcard that looked strict enough in review slides.
It blocked little, protected less, and broke one critical onboarding path intermittently for enterprise users behind strict browser settings. Nobody noticed for 48 hours because core API uptime was clean. Sales blamed onboarding copy. Support blamed SSO. Security blamed browser quirks. The fix took six hours. The deal slippage lasted six weeks. The lesson was blunt: “almost secure” can be more expensive than plainly unfinished because it creates false confidence exactly where business risk is highest.
- Review for drift on a calendar, not by memory.
- Eliminate wildcards gradually but relentlessly.
- Assign script intake ownership before rollout.
Apply in 60 seconds: Add a monthly “header drift + third-party intake” review to your security ops calendar.
FAQ
Do security headers improve SEO directly or indirectly?
Mostly indirectly. Headers don’t function like a direct ranking boost knob. They improve site integrity and reduce incident-driven disruption, which protects availability, trust, and user experience signals that matter commercially.
Which security header should a startup implement first?
If you need one fast move, start with X-Content-Type-Options: nosniff and frame protections on critical routes, then implement HSTS carefully. Start CSP in report-only as early as possible so learning begins before enforcement pressure appears.
Is CSP worth it for small teams with limited DevOps bandwidth?
Yes, if you phase it. Report-only first, route-level scope, clear ownership, and canary enforcement. CSP becomes expensive when treated as a one-shot launch instead of a managed program.
Can HSTS break subdomains or staging environments?
Yes, especially with includeSubDomains or preload if your subdomain and certificate inventory is incomplete. Validate scope and readiness before strict commitments.
How do we quantify ROI if we haven’t had a visible breach yet?
Use avoided-cost modeling and operational proxies: incident reduction rate, escalation volume, on-call hours recovered, and procurement cycle friction reduced.
Are legacy headers like X-XSS-Protection still relevant?
Modern guidance generally favors stronger contemporary controls like CSP and robust output encoding over relying on legacy browser-specific protections. Prioritize controls with current practical value.
Should API responses use the same headers as web pages?
Not always one-to-one. Some headers are page-context specific, while others still support consistent hardening posture. Apply by response type and threat model, not by blind uniformity.
How often should we review and tighten policies?
Monthly for active products is a practical baseline, plus review on significant front-end architecture changes, major partner script changes, or security incidents.
What’s the difference between passing a scanner and reducing real risk?
Passing a scanner means a checklist snapshot looks good. Reducing real risk means exploit pathways are actually constrained on revenue-critical routes under real user traffic and change conditions.
Do enterprise customers actually care about header posture in procurement?
Yes. Not every buyer goes equally deep, but security questionnaires and exception workflows often surface browser-layer controls as trust signals in broader posture evaluation.
12) Next step: one concrete action you can take this week
Run a header baseline + route inventory on your top 20 revenue-critical URLs, then deploy:
- HSTS (carefully scoped),
- X-Content-Type-Options,
- frame protections,
- CSP in report-only with logging to a shared triage board.
Set a 14-day review to convert the first CSP subset into enforce mode.
Don’t aim for perfect policy in one leap. Aim for controlled gains that survive real traffic. The curiosity loop from the opening is simple: yes, headers can protect revenue, but only when you prioritize them like operators, not checklist collectors.
Quote-prep list (before you compare tooling or services)
- Top 20 revenue URLs and route owners
- Current header snapshot by environment
- Third-party script inventory and business owner
- Rollback process owner and SLA
- Quarterly incident/support baseline
Neutral action: Gather these first, then evaluate tools or partners with less guesswork and fewer surprises. If you are evaluating external help, compare providers against a structured penetration testing cost model and scope clarity checklist.
If you have 15 minutes, run the baseline on five routes today. Not twenty, not someday. Five. That small operational promise is where security ROI starts becoming real and measurable. If you want a practical execution rhythm after baseline, pair this with a lightweight pentest reporting template so weekly findings translate into accountable action instead of slideware.
Last reviewed: 2026-02.

