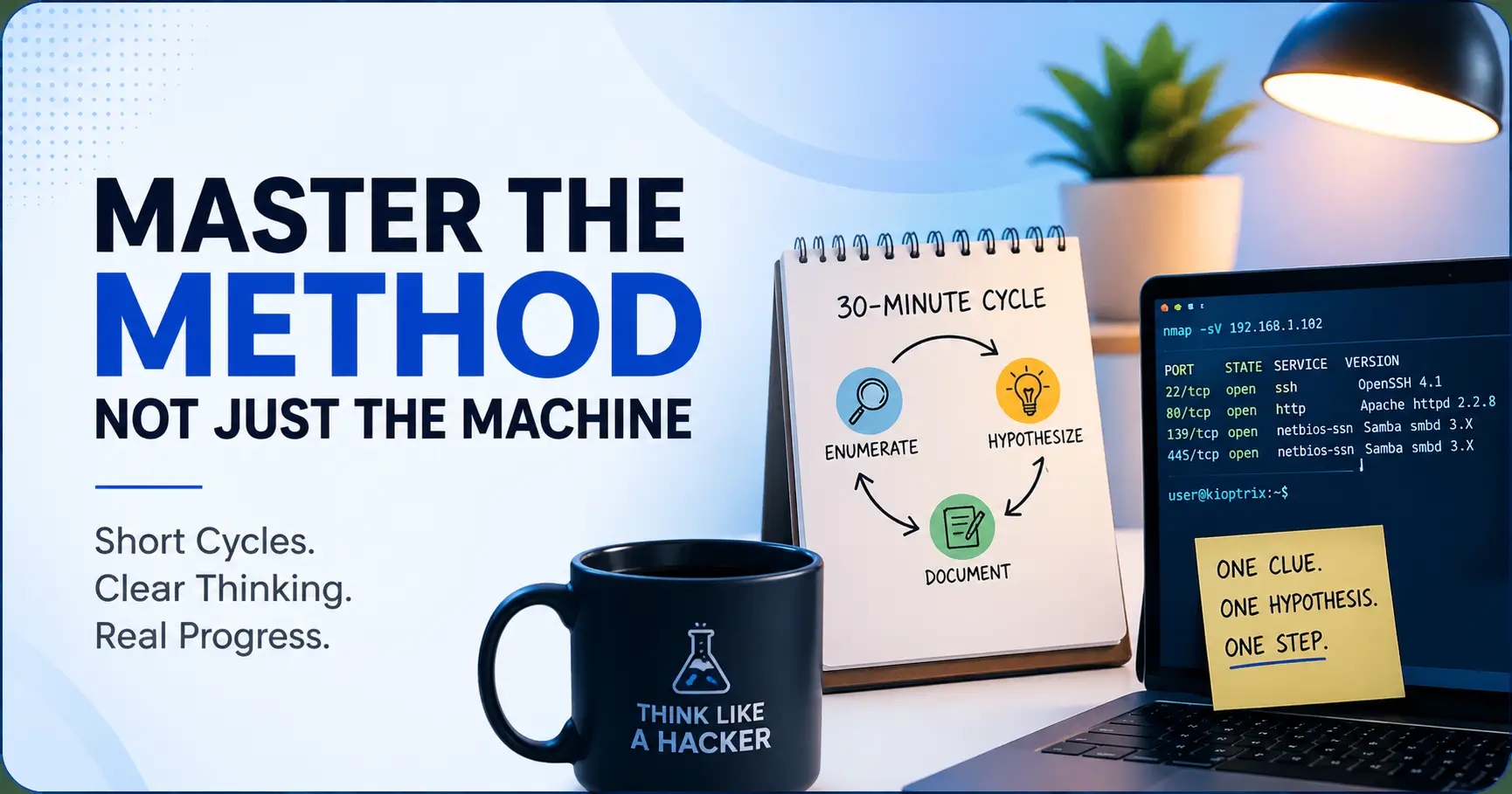
Why Kioptrix Level Works Better When You Practice in Short Cycles
Master the Method, Not Just the Machine Escaping the beginner trap of the Kioptrix “fog.” You sit down for a “quick” Kioptrix session—one scan, three tabs, two service banners—and end the hour with more terminal output than understanding. This is the beginner trap: not laziness, but a collapse of enumeration, hypothesis, and documentation into a … Read more